
Defining Account Takeover Attack
Let’s start by defining account takeover fraud. Account takeover (ATO), a form of identity theft, involves a third-party assuming control of an online account with malicious intent.
One of the biggest cybersecurity concerns in existence today is account takeover, which has become more common. Attackers who steal online identities have access to private data like social security numbers and financial information.
Attacks like these are carried out to steal information, harm reputations, or commit fraud. They are becoming more widespread as a result of how simple it is to hijack an online account.
Where do Account Takeover attacks originate from?
Account Takeover attempts typically come from a variety of places, including anonymous proxies, botnets, cloud hosting servers, and ISPs. 45 percent of Account Takeover attacks come from the US, according to a breakdown of attacks by nation. The UK, Brazil, China, and Russia are close behind with noticeably smaller percentages. The majority of Account Takeover assaults continue to attempt to impersonate trusted browsers, mostly Chrome, even if many of them are launched from proprietary bot engines or tools (47.2 percent).
ATO Attacks – Targeted Organizations
Financial organizations have historically been primarily concerned about unauthorized access to user accounts. These days, ATO assaults can have an impact on any enterprise with a user-facing login. Financial gain is the main driving force behind cybercrime; these criminals often look for the quickest and easiest ways to make money. Nowadays, doing so entails stealing cryptocurrency, selling customer data, or duping victims into downloading ransomware.
The goal of the cybercriminal varies depending on the circumstance and is to obtain personally identifiable information (PII). Because it may be used to perpetrate identity theft in a number of ways, including committing insurance fraud, getting credit card information, and applying for lines of credit, personal information is highly sought after.
In order to make the fraudulent communications seem more realistic and to make it easier for hackers to find their victims, personal information can be used in spam and phishing campaigns. Attacks of this nature typically target the public sector, the medical industry, and educational organizations.
eCommerce sites are also impacted by ATO attacks. A user’s account can be accessed by cybercriminals, who then use it to make purchases on the user’s behalf. After taking over the account, the attackers will log in, swiftly add valuable items to the shopping basket, then quickly complete the payment using the user’s already saved payment information while changing the shipping address to their own.
How Account Takeover Fraud Happens
Here are some common attack vectors for account takeovers:

Theft of Login Credentials through Data Breach
Every year, data breaches allow access to billions of documents containing personal information. Cybercriminals typically need stolen usernames and passwords in order to access an account. Cybercriminals will try to access many online services using the disclosed usernames and passwords because many people use the same login information for numerous websites or services.
Brute Force Credential Cracking
Cybercriminals can gain access to your personal information by testing a number of passwords to see which one works. They use bots that can check a lot of different password combinations to speed up the process. 8-character passwords can be broken in an hour or less with the methods now available to hackers.
Phishing for Login Information
Cybercriminals may even merely request the victims’ login information. This is accomplished by tricking individuals into disclosing their information through phishing scams. Phishing efforts can be made through a variety of channels, including SMS, emails, phoney websites, chat sessions, malicious phone applications, and more.
Data Theft via Viruses and Malware
Malware and viruses have a wide range of capabilities. They frequently take data from a victim’s device. Many viruses have the ability to monitor your keystrokes as you type in passwords, while others can steal bank information by eavesdropping on your browser. This can be stopped with antivirus software.
Man in the Middle (MitM) Attacks
Before reaching a website, your internet traffic passes via a large number of servers. Without encryption, if someone were to intercept your traffic while it was in transit, they could see all of your online activities, including your usernames and passwords. These man-in-the-middle assaults are typically conducted through public Wi-Fi networks or residential internet routers. Utilizing dependable VPN software will help you protect yourself.
Detecting Account Takeover Fraud in Financial Institutions
ATO is particularly serious in banking institutions because it can immediately result in theft and compromise of a person’s financial accounts. Organizations have the opportunity to spot early warning signs of fraudulent activity that could constitute an account takeover through ongoing monitoring.
Financial institutions will have total visibility into a user’s activities throughout the transaction process thanks to a good fraud detection system. The best safeguard is a system that monitors all bank account activity; before a cybercriminal can steal money, they must first carry out other tasks, such creating a payee.
You can identify patterns of activity that indicate the potential of account takeover fraud by keeping track of every action made on a certain account. Before transferring money from an account, cybercriminals must complete a number of steps, thus a fraud detection mechanism that continuously monitors behaviour can spot clues and trends to determine whether a consumer is being attacked.
A mechanism like this for detecting fraud can also keep an eye on risk depending on information, such as location. For instance, it may be suspicious and indicate that two different people are using the same account if a consumer enters their account first from South America and then 20 minutes later from Asia.
The detection of account takeover (ATO) assaults can be done in a variety of methods. Utilizing a third-party security system that can recognize ATO threats is the most dependable approach. This section will go through how to use these solutions and what features they need to have in order to properly detect ATO assaults.
Anyone can be the victim of account takeover attacks, and the best way to avoid them is by careful monitoring. When a criminal takes control of a person’s online identity and uses it to commit fraud, this is known as an account takeover. This can be accomplished by collecting usernames and passwords, then utilizing them to access the victim’s online accounts.
How to Prevent Account Takeover
Any online business that requires sensitive login and registration must have account takeover protection. The following tips can help you stop account takeover attacks:
Blocking old browser versions
Because of their vulnerabilities and weaknesses, earlier browser versions are preferred by the majority of bot attack facilitators. Therefore, blocking these versions is important.
Reinforcing popular bad bot gateways
For the security of your company, it is essential to identify the gaps in your web design that let bots attack your website. To stop upcoming bot invasions, the hidden paths must also be protected.
Traffic source assessment
The ability to identify artificial traffic and subsequently stop it is facilitated by observation of traffic sources, session length, and bounce rate from sources.
Failed entries monitoring
ATO attack attempts are typically indicated by a high volume of unsuccessful login attempts, gift card or credit card inputs, or by long periods of time between failed login attempts.
Full-stack bot management solutions
You can identify and reduce bots at all website entries with the help of bot management technologies. However, the cost of this approach is high.
2FA
In addition to login credentials, 2-factor authentication adds another layer of verification in the form of an SMS code, email code, or fingerprint for mobile applications.
If the ATO assault compromises the email and you haven’t set up backup mail, the e-mail code option could not be effective.
Advanced CAPTCHA
Modern AI-based Given that it uses behavioral analysis, environmental analysis, and little user friction to combat bot assaults, CAPTCHA is one of the best defenses against account takeover attempts.
Account Takeover Protection
Here are a few strategies you can use to defend your company against ATO.
Multi-Factor Authentication
At this point, ask your user to authenticate using something in addition to their password:
- Something they know – a security question, such as their mother’s maiden name, first pet’s name, etc.
- Something they possess – a token, dongle, or other physical objects.
- Something they are – face ID, iris scan, fingerprint, or the like.
You can design an adaptive approach that changes depending on perceived risk rather than repeatedly requesting this MFA. For instance, once a user attempts to access the account from a different login device or from a strange place, you can request two-factor authentication.
Account Tracking System
You need a procedure in place that will halt new attacks after an account has been compromised. You can examine all activity associated with a questionable account by sandboxing it, then suspend the account if necessary.
AI-Based Detection
More sophisticated account takeover attempts and bot attacks can be discovered using AI-based ATO security and detection systems. Fourth-generation bots are frequently used in ATO attempts because they can mimic human behavior and are hence more difficult to identify. To successfully detect sophisticated ATO attempts and keep an eye out for suspicious activity, advanced AI-based technology is required.
Web Application Firewall (WAF)
- Identifying and blocking requests from known attackers
- Detect bad bots used by attackers as part of ATO attacks
- Identify credential stuffing on login portals
- Detect and block brute force attacks by identifying sessions passing an unusual number of credentials
- Enabling multi-factor authentication (MFA) or authentication via third-party identity providers like Google
- Scan traffic for “fingerprints” indicating credential stuffing tools
Account Takeover Protection with AuthSafe
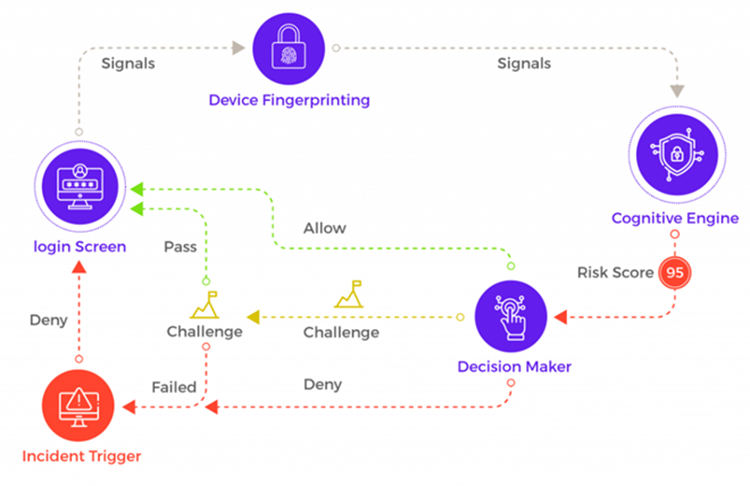
AuthSafe is an identity protection platform that provides information about fraudulent login details in your applications. An easy-to-install, fully automated solution that helps to identify the potentially compromised accounts by predictive fraud research, cognitive engine modeling, and using suspicious account activity.
AuthSafe works with financial services, SaaS products, and online digital goods organizations to detect and prevent account takeovers without compromising customer experience. It helps track the location, time, accessed data, and IP address details of the user. To get started, you need to integrate AuthSafe with your web application.
AuthSafe allows various integrations that include SDKs, API, and JavaScript. To choose the best option and integrate AuthSafe with your web application, refer to the Integration documentation.
Conclusion
Bot attack never known as ATO, is very problematic for both organizations and account owners. For every online enterprise, securing your website or application against ATO is essential. A tested solution to defend your clients from ATO attacks is essential if you want your company to have a spotless reputation, consistent growth, and enhanced LTV and turnover.
Your online account could be taken once more every minute you wait, greatly endangering your company. 98.3% of requests on crucial gateways are made by bad bots. Additionally, they aren’t hanging out. Protect your company straight away from dangerous bot attacks without waiting.
Behind every malicious bot, operation is people trying to profit. The likelihood of an assault is significantly high if stealing user accounts on your website could result in financial gain. Attacks known as account takeovers range in ingenuity, evasiveness, and severity. From low-intensity attacks that go unnoticed to high-intensity attacks that, if left unchecked, could overwhelm the web server and result in Denial of Service. As attackers refine their methods and adapt their strategies, the characteristics and statistics of Account Takeover attacks that were discussed in this blog may vary and develop over time.
Take a look at the industry-leading AuthSafe for a solution that goes beyond bot detection and guarantees business priorities like customer experience and conversion rates remain good.






