
Background:
A key problem in an enterprise is to safeguard its user’s accounts against potentially bad actors (or rogue users). The Verizon Data Breach Investigations Report 2021 (DBIR-2021) reported 79,635 incidents and 5,258 breaches involving millions of sensitive records in 2021. Data incidents and breaches are a fact of life and companies need to spend as much effort on planning how to prevent them efficiently as they do on other services.
As it’s evident from the given figure 5. & 6., Social Engineering, System Intrusion and Basic Web application attacks make for the largest proportion of attacks among both the categories & the interesting fact about these attacks is in them being having a property of behaviours over a session or time frame.

Also, it’s evident from fig 7. that 85% of breaches involved the human elements that again indicates the behaviour of an organic entity behind those breaches. Finally, fig 8. sums up the colossal monetary loss that could have been avoided had there been a robust mechanism or platform to avoid or mitigate the breaches & incidents. With tremendous monetary losses, the need for a preventive solution can’t be uncalled for.
User behavioural profiling & Its need:
With the aforementioned discussion, the need for a preventive solution is implied but the traditional solutions, which are rule-based, often goes rogue with the ever new incidents or breaches due to being usually endowed with variable characteristics of environments across websites that make the problem of detecting bad users using a rule-based system very complex & unscalable. However, presuming the actions of a compromised & rogue user are inherently different from its usual behaviour makes this problem somewhat simpler to tackle if the user profile based on its behaviour is maintained. If each of the user’s actions is monitored over time and against actions of similar users, one can bring about a baseline profile of the user’s behaviour, then any deviations from this behaviour can be flagged as potential anomalies that call for further investigation.
Moreover, with the maintenance of users profile of their behaviour, proactive defences come into vogue contrary to traditional reactive defences. Traditional reactive defences operate only when security incidents take place, or immediately thereafter whereas a proactive solution proactively protects users devices and networks. By observing user behaviour, it can predict whether they will be exposed to malicious content on the web seconds before the moment of exposure, thus opening a window of opportunity for proactive defences.

What is a User Behaviour?
The behaviour of an actor is simply a pattern of actions performed by the actor in order to achieve certain goals. Sometimes, according to the problem or objective concerned, its behaviour may also include environments through which the actor has been performing actions. As an instance, time, place, environment, a chronology of page visits, etc. of a user can make for a behaviour.
As shown in the below figure, a machine learning algorithm generally requires a sophisticated & refined user behaviour that is derived or refined from raw information about a particular or batch of user activities.
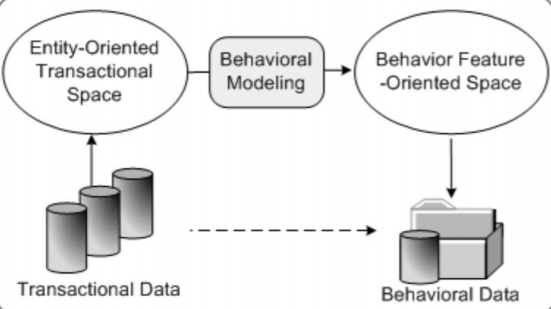
Raw transactional data is modelled to behaviour feature-oriented space ready to be ingested by ML algorithms. The process that creates behaviour to be devoured by algorithms is called behavioural modelling. Behavioural Modelling develops modelling and representation methods to capture behaviour characteristics and dynamics of a user. Once a behaviour is modelled, it could be further devoured by an algorithm, typically an ML one, to provide us with security decisions — whether a user is rogue/bad or not?
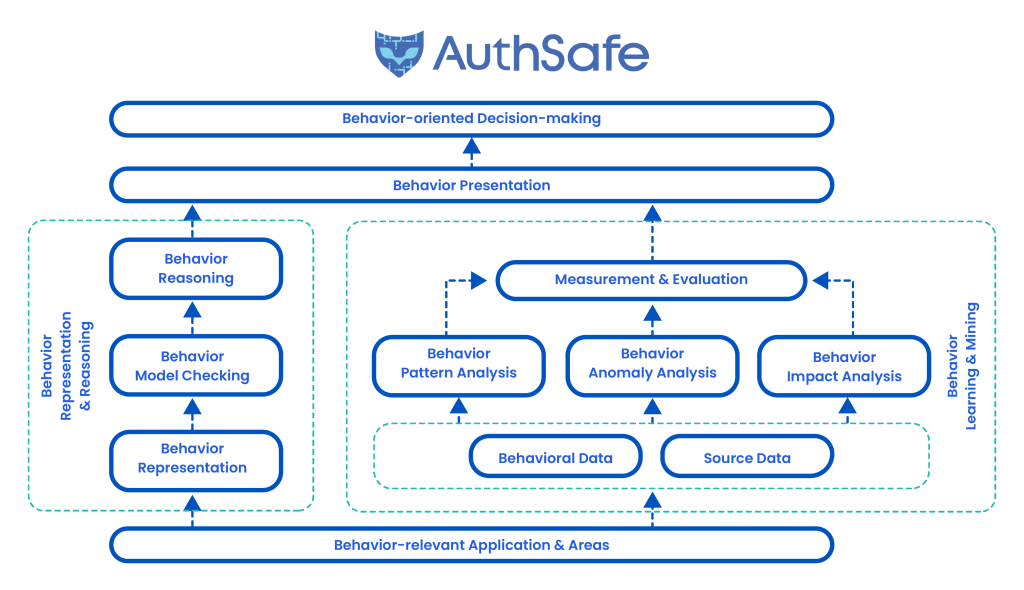
Following is a general diagram succinctly describing the aforementioned dynamics of behaviour with its analysis & modelling to achieve behaviour-oriented decision-making as insecurity.
Graph-Based User Behaviour Modelling:
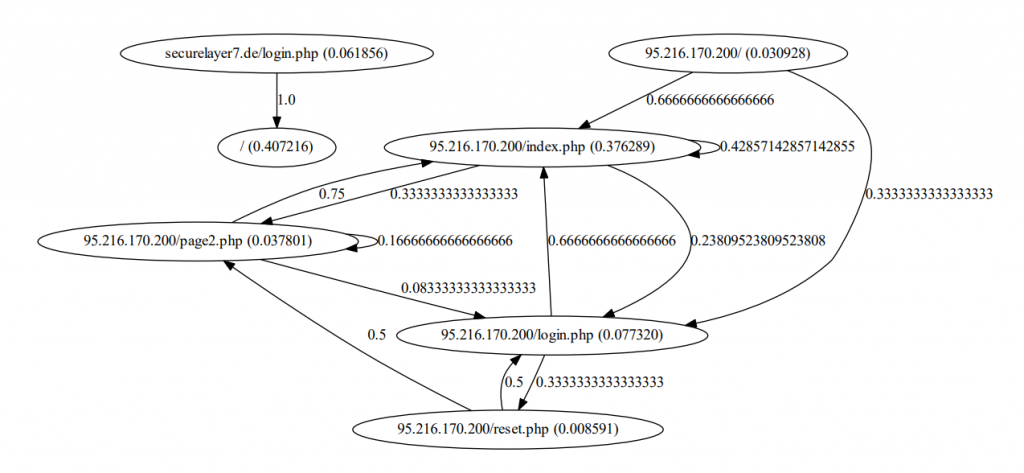
Graph-Based user behaviour modelling is a common way to model the behaviour of an actor. Although the theory & background to understand it in light of behaviour modelling extends way deeper & complex, it could be intuitively understood by a simple state machine, specifically nondeterministic finite automaton.
A state machine is a graph where nodes describe states & edges describe the transition from one state to another. The transition edges can be further modelled to describe behaviour as shown in the following figure. In the following simple illustration, user profiling has been brought about by modelling the page-visit behaviour of a user based on its past data. Nodes are the web pages & probabilities labelled on transition edges depicting the probability with which the user will move from a particular page to another.
Now, this model can be used to detect the possibility of abnormal behaviour in page visits of a particular user using a simple statistical inference.
Conclusion:
User profiling with its behaviour is a promising approach or tool through which proactive defences backed by sophisticated machine learning algorithms can be given to users to avoid & mitigate ever-alarming breaches and incidents costing colossal monetary losses. In this approach, the relevant entities make for user behaviour that becomes instrumental in isolating a rogue user with its behaviour before it breaks into the system.
To isolate a bad actor with its behaviour, its real-time behaviour is assessed against a baseline behaviour that is concluded in prior from the good actor(s) with its/their usual behaviour.
Credits:
- https://www.verizon.com/business/solutions/enterprise/ for their data.
- http://www.behaviorinformatics.org/ for their diagrams.







4,572 replies on “Behaviourally User Profiling For Securing Them – Authsafe”
[…] an account, cybercriminals must complete a number of steps, thus a fraud detection mechanism that continuously monitors behaviour can spot clues and trends to determine whether a consumer is being […]
[…] means looking out for changes in customer behavior, such as a sudden increase or decrease in spending or the number of orders placed. You can also […]
[…] attackers will change their tools and techniques, but by staying alert and implementing the security measures that AuthSafe offers, you can stay safe from […]
Thank you very much for sharing. Your article was very helpful for me to build a paper on gate.io. After reading your article, I think the idea is very good and the creative techniques are also very innovative. However, I have some different opinions, and I will continue to follow your reply.
I am a website designer. Recently, I am designing a website template about gate.io. The boss’s requirements are very strange, which makes me very difficult. I have consulted many websites, and later I discovered your blog, which is the style I hope to need. thank you very much. Would you allow me to use your blog style as a reference? thank you!
I am a student of BAK College. The recent paper competition gave me a lot of headaches, and I checked a lot of information. Finally, after reading your article, it suddenly dawned on me that I can still have such an idea. grateful. But I still have some questions, hope you can help me.
Thanks for shening. I read many of your blog posts, cool, your blog is very good. https://www.binance.com/en/register?ref=P9L9FQKY
I may need your help. I’ve been doing research on gate io recently, and I’ve tried a lot of different things. Later, I read your article, and I think your way of writing has given me some innovative ideas, thank you very much.
The point of view of your article has taught me a lot, and I already know how to improve the paper on gate.oi, thank you. https://www.gate.io/id/signup/XwNAU
Thanks for shening. I read many of your blog posts, cool, your blog is very good. https://accounts.binance.com/en/register-person?ref=P9L9FQKY
I may need your help. I tried many ways but couldn’t solve it, but after reading your article, I think you have a way to help me. I’m looking forward for your reply. Thanks.
I may need your help. I tried many ways but couldn’t solve it, but after reading your article, I think you have a way to help me. I’m looking forward for your reply. Thanks.
The point of view of your article has taught me a lot, and I already know how to improve the paper on gate.oi, thank you. https://www.gate.io/pt-br/signup/XwNAU
Can you be more specific about the content of your enticle? After reading it, I still have some doubts. Hope you can help me. https://accounts.binance.com/en/register?ref=53551167
The point of view of your article has taught me a lot, and I already know how to improve the paper on gate.oi, thank you. https://www.gate.io/id/signup/XwNAU
I may need your help. I tried many ways but couldn’t solve it, but after reading your article, I think you have a way to help me. I’m looking forward for your reply. Thanks.
I don’t think the title of your article matches the content lol. Just kidding, mainly because I had some doubts after reading the article. https://accounts.binance.com/zh-CN/register-person?ref=DB40ITMB
Great info and straight to the point. I don’t know if this is in fact the best place to ask but do you guys have any thoughts on where to get some professional writers? Thx 🙂
It’s actually a cool and helpful piece of info. I am glad that you shared this useful information with us. Please keep us informed like this. Thanks for sharing.
Oh my goodness! an incredible article dude. Thank you However I’m experiencing subject with ur rss . Don’t know why Unable to subscribe to it. Is there anybody getting similar rss drawback? Anyone who is aware of kindly respond. Thnkx
Недавно мне понадобилось 4 000 рублей на неотложные нужды. По совету друга, я посетил yelbox.ru. Там я нашел много полезных статей о том, как правильно взять займы онлайн на карту и список проверенных МФО. И узнал, что некоторые из них предоставляют займы без процентов!
Ночные финансовые потребности больше не проблема с порталом wikzaim. Я легко и быстро получил микрозайм от двух микрофинансовых компаний, оформив заявку онлайн. Сервис работает круглосуточно, обеспечивая клиентов необходимыми средствами.
Представьте, как вы просыпаетесь от легкого морского бриза, открываете глаза и видите бескрайние просторы Черного моря. Это не мечта – это реальность отдыха в отелях Туапсе в 2023 году!
Наши отели – это место, где каждый день наполнен магией и вдохновением. Мы заботимся о вашем комфорте, предлагая лучшие услуги и удобства. Забронируйте свой идеальный отдых уже сегодня и почувствуйте настоящее волшебство Туапсе!
Ключевое слово: волшебство. В каждом тексте создается атмосфера уюта, комфорта и волшебства, которые ожидают гостей в отелях Туапсе в 2023 году. Ждем вас открыть этот удивительный мир с нами!
Искал в Яндексе казино на деньги и сразу же наткнулся на caso-slots.com. Сайт предлагает обширный выбор казино с игровыми автоматами, бонусы на депозит и статьи с советами по игре, что помогает мне разобраться, как увеличить свои шансы на выигрыш.
http://withoutprescription.guru/# best non prescription ed pills
https://withoutprescription.guru/# online prescription for ed meds
where to buy cheap clomid prices: clomid order – get clomid online
non prescription erection pills: ed meds online without doctor prescription – buy prescription drugs without doctor
prescription drugs without doctor approval: buy prescription drugs online without – non prescription erection pills
Демо игровых слотов предлагают уникальную возможность насладиться азартом и развлечениями казино, не тратя при этом своих финансовых средств. Это отличные метод испытать удачу, изучить игры и разработать стратегии без расхода средств.
Благодаря огромному количеству игровых автоматов с демо игрой, каждый игрок найдет что-то по своему вкусу. От классических трехбарабанных слотов до современных видеослотов с крутейшей графикой и увлекательными бонусными раундами.
Играть в игровые автоматы играть демо просто и легко. Вам не нужно регистрироваться и пополнять баланс – просто подберите подходящий игровой автомат и начните играть. Это отличная возможность попробовать разные стратегии ставок, изучить выигрышные комбинации и просто насладиться процессом игры.
Демо-режим также дает возможность вам сделать оценку отдачи игрового автомата и понять, как он подходит вам по стилю и предпочтениям. Вы можете играть беспконечно долго, не боясь за свои деньги.
https://canadapharm.top/# prescription drugs canada buy online
mexican rx online: buying prescription drugs in mexico online – pharmacies in mexico that ship to usa
purchase doxycycline online: doxycycline mono – doxycycline online
https://indiapharm.guru/# best online pharmacy india
legitimate canadian pharmacies: Certified Canada Pharmacy – is canadian pharmacy legit
https://kamagra.team/# Kamagra 100mg price
https://tadalafil.trade/# tadalafil price comparison
cost of generic tadalafil: generic tadalafil daily – tadalafil price in india
pills for ed non prescription erection pills mens ed pills
http://edpills.monster/# treatment of ed
Levitra 10 mg best price: Generic Levitra 20mg – п»їLevitra price
where to buy sildenafil 100mg sildenafil best price sildenafil usa
https://levitra.icu/# buy Levitra over the counter
http://kamagra.team/# Kamagra 100mg price
buy Kamagra: Kamagra 100mg – super kamagra
non prescription ed drugs: erectile dysfunction drugs – erectile dysfunction medications
pills for erection best ed pills cheap erectile dysfunction pill
http://edpills.monster/# what are ed drugs
ed medications online: top ed pills – ed drug prices
cheapest sildenafil 100 mg online price of sildenafil 100mg sildenafil 20 mg over the counter
https://levitra.icu/# Cheap Levitra online
buy tadalafil online canada: best pharmacy buy tadalafil – cheap generic tadalafil
https://edpills.monster/# ed medications online
Buy Vardenafil 20mg: Levitra 10 mg best price – Levitra 10 mg buy online
zithromax 250 mg buy zithromax zithromax 250 mg
amoxicillin 500 mg tablet: buy amoxil – amoxicillin 500 mg tablet price
http://azithromycin.bar/# order zithromax over the counter
zithromax capsules 250mg: zithromax antibiotic – can you buy zithromax over the counter in canada
zithromax over the counter canada zithromax antibiotic zithromax antibiotic
http://ciprofloxacin.men/# buy ciprofloxacin over the counter
where to get zithromax over the counter: zithromax antibiotic – generic zithromax medicine
buy doxycycline without rx: Doxycycline 100mg buy online – doxycycline no prescription best prices
where to get amoxicillin over the counter amoxil for sale amoxicillin pharmacy price
http://ciprofloxacin.men/# buy generic ciprofloxacin
lisinopril 10 mg tablet: Over the counter lisinopril – lisinopril 20 mg for sale
Классный обзор. Приятно было прочитать.
В свою очередь предложу вам играть в вавада игровые автоматы – это захватывающий мир азартных игр. Предлагает большой набор игровых аппаратов с уникальными тематиками и и интересными бонусами.
Vavada – это топовое онлайн-казино, которое предлагает игрокам невероятные эмоции и позволяет выиграть по-настоящему крупные призы.
Благодаря крутейшей графике и звуку, слоты Вавада погрузят вас в мир азарта и развлечений.
Независимо от вашего опыта в играх, в Vavada вы без проблем найдете игровые автоматы, которые подойдут по вкусу.
where to get zithromax over the counter buy zithromax canada zithromax for sale online
Very interesting info !Perfect just what I was looking for! “It’s not the having, its the getting.” by Elizabeth Taylor.
http://doxycycline.forum/# vibramycin
lisinopril 2mg tablet: Buy Lisinopril 20 mg online – lisinopril 30 mg tablet
buy zithromax 500mg online: zithromax antibiotic without prescription – generic zithromax india
zithromax cost uk zithromax z-pak zithromax coupon
https://azithromycin.bar/# zithromax 500 price
zithromax 250 mg pill: buy cheap generic zithromax – where can i purchase zithromax online
amoxicillin without a prescription amoxil for sale azithromycin amoxicillin
https://doxycycline.forum/# can you buy doxycycline over the counter nz
can you buy doxycycline online: doxycycline 100mg – doxycycline 1mg
doxycycline tablet price in india: Buy doxycycline 100mg – buy doxycycline online usa
canadian pharmacy androgel: cheap drugs online – no 1 canadian pharmacy
reliable canadian pharmacy certified canadian pharmacy canadian compounding pharmacy
http://indiapharmacy.site/# india pharmacy
mexican pharmaceuticals online: mexico pharmacy – medicine in mexico pharmacies
medication from mexico pharmacy: mexican pharmacy online – mexico pharmacies prescription drugs
http://canadiandrugs.store/# legitimate canadian pharmacies
online pharmacy no scripts: buy medication online – canadian pharmacy prednisone
trust online pharmacies cheap drugs online verified canadian pharmacy
reputable indian online pharmacy: reputable indian online pharmacy – cheapest online pharmacy india
http://canadiandrugs.store/# canadadrugpharmacy com
https://gabapentin.life/# neurontin canada
clomid order: Buy Clomid Online Without Prescription – can i get generic clomid without insurance
http://gabapentin.life/# neurontin 4000 mg
An easy and fast loan application process can be a true relief when navigating financial hurdles. The convenience of a streamlined application, where you can input necessary information quickly and effortlessly, significantly eases the stress of seeking financial assistance. I’ve found that platforms offering such easy and fast loan application procedures prioritize user experience without compromising on security or accuracy. The ability to complete the application swiftly and efficiently saves time and ensures that urgent financial needs can be addressed without unnecessary delays. Exploring services that offer this kind of user-friendly application process has been a game-changer for managing unexpected expenses.
Nowadays personal loans online have transformed the borrowing landscape, offering unparalleled convenience and accessibility. The ability to apply for personal loans online has simplified the entire borrowing process. It’s impressive how these platforms provide a seamless experience, allowing users to complete applications, receive approvals, and access funds—all within the digital realm. What’s more, the competitive rates and flexible repayment options available through reputable online lenders make personal loans online a preferred choice for many. Exploring these avenues online can offer a hassle-free solution for managing financial needs from the comfort of home.
ventolin tablets uk: buy ventolin over the counter – order ventolin online canada
https://paxlovid.club/# paxlovid covid
paxlovid buy http://paxlovid.club/# Paxlovid buy online
drug neurontin 200 mg: cheap gabapentin – neurontin 300mg caps
Thank you very much for sharing, I learned a lot from your article. Very cool. Thanks. nimabi
https://clomid.club/# how to get generic clomid tablets
where to buy wellbutrin: Buy Wellbutrin XL 300 mg online – wellbutrin generics
https://paxlovid.club/# paxlovid india
п»їpaxlovid: Buy Paxlovid privately – paxlovid price
http://paxlovid.club/# paxlovid covid
neurontin 500 mg tablet: gabapentin best price – buy gabapentin
http://clomid.club/# can i purchase cheap clomid without rx
viagra online in 2 giorni: sildenafil prezzo – viagra online in 2 giorni
migliori farmacie online 2023: Avanafil farmaco – farmacie on line spedizione gratuita
acquisto farmaci con ricetta avanafil prezzo in farmacia farmacia online
comprare farmaci online con ricetta: avanafil prezzo – farmaci senza ricetta elenco
farmacie online affidabili: avanafil generico prezzo – farmacie on line spedizione gratuita
http://avanafilit.icu/# farmacia online senza ricetta
viagra subito: sildenafil prezzo – alternativa al viagra senza ricetta in farmacia
acquistare farmaci senza ricetta: farmacia online – farmacie online affidabili
azithromycin 500 mg coupon
where can you get azithromycin
farmacia online kamagra gold farmacia online migliore
farmacie online affidabili: Dove acquistare Cialis online sicuro – farmacia online senza ricetta
farmacia online miglior prezzo: Tadalafil prezzo – farmacia online miglior prezzo
acquisto farmaci con ricetta: farmacia online migliore – acquisto farmaci con ricetta
https://sildenafilit.bid/# viagra naturale in farmacia senza ricetta
farmacie online affidabili: kamagra – farmacie on line spedizione gratuita
п»їfarmacia online migliore: farmacia online piu conveniente – migliori farmacie online 2023
viagra pfizer 25mg prezzo viagra generico esiste il viagra generico in farmacia
farmacie online autorizzate elenco: dove acquistare cialis online sicuro – farmaci senza ricetta elenco
farmaci senza ricetta elenco: farmacia online migliore – acquistare farmaci senza ricetta
acquistare farmaci senza ricetta: kamagra gel – farmacie online autorizzate elenco
farmacia online più conveniente: avanafil generico – farmacia online migliore
http://sildenafilit.bid/# miglior sito per comprare viagra online
plaquenil price us
farmacia online migliore: kamagra oral jelly – acquistare farmaci senza ricetta
farmacie online sicure avanafil farmacia online migliore
comprare farmaci online con ricetta: kamagra gel prezzo – п»їfarmacia online migliore
farmacia online più conveniente: farmacia online migliore – farmacia online migliore
farmaci senza ricetta elenco: farmacia online più conveniente – farmacia online senza ricetta
farmacia online migliore: kamagra oral jelly – acquisto farmaci con ricetta
doxycycline 200mg
top farmacia online: kamagra oral jelly consegna 24 ore – farmacie online autorizzate elenco
http://farmaciait.pro/# farmaci senza ricetta elenco
farmacia online senza ricetta: dove acquistare cialis online sicuro – farmacie online sicure
farmacie online autorizzate elenco farmacia online acquistare farmaci senza ricetta
orlistat 120 mg
farmacie online sicure: Farmacie a roma che vendono cialis senza ricetta – farmacia online
acquisto farmaci con ricetta: Farmacie a milano che vendono cialis senza ricetta – farmacia online migliore
farmacie online sicure: acquisto farmaci con ricetta – farmacie online autorizzate elenco
farmacia online senza ricetta: farmacia online migliore – comprare farmaci online all’estero
rx doxycycline
farmacie on line spedizione gratuita: comprare avanafil senza ricetta – top farmacia online
stromectol online pharmacy
synthroid 0.05 mcg
п»їfarmacia online migliore farmacie online sicure comprare farmaci online all’estero
farmacia online più conveniente: Farmacie a milano che vendono cialis senza ricetta – comprare farmaci online con ricetta
https://kamagrait.club/# migliori farmacie online 2023
farmacie online autorizzate elenco: Farmacie che vendono Cialis senza ricetta – farmacie on line spedizione gratuita
comprare farmaci online all’estero: cialis generico consegna 48 ore – migliori farmacie online 2023
viagra subito: sildenafil 100mg prezzo – viagra generico in farmacia costo
comprare farmaci online con ricetta: farmacia online – acquistare farmaci senza ricetta
viagra naturale in farmacia senza ricetta: sildenafil 100mg prezzo – viagra prezzo farmacia 2023
farmacia online senza ricetta farmacia online farmacie online autorizzate elenco
farmacias baratas online envГo gratis farmacia online barata farmacia online 24 horas
https://farmacia.best/# farmacias online seguras en españa
farmacias baratas online envГo gratis: cialis en Espana sin receta contrareembolso – farmacia barata
https://sildenafilo.store/# comprar viagra sin gastos de envÃo
http://farmacia.best/# farmacia online
https://sildenafilo.store/# viagra para hombre precio farmacias similares
https://vardenafilo.icu/# farmacia envÃos internacionales
farmacia online 24 horas comprar kamagra en espana farmacia online envГo gratis
https://sildenafilo.store/# viagra para hombre precio farmacias
farmacia online 24 horas: Levitra precio – farmacia envГos internacionales
http://tadalafilo.pro/# farmacias baratas online envÃo gratis
https://kamagraes.site/# farmacia envÃos internacionales
http://tadalafilo.pro/# farmacia online internacional
https://sildenafilo.store/# sildenafilo 50 mg precio sin receta
https://sildenafilo.store/# viagra online cerca de zaragoza
https://vardenafilo.icu/# farmacias online seguras en españa
farmacias online seguras Levitra sin receta farmacias baratas online envГo gratis
farmacias online seguras: Levitra Bayer – farmacia 24h
https://kamagraes.site/# farmacias online baratas
http://vardenafilo.icu/# farmacias online seguras en españa
viagra para hombre precio farmacias: comprar viagra – viagra para hombre precio farmacias
http://sildenafilo.store/# sildenafilo sandoz 100 mg precio
farmacia 24h vardenafilo farmacias online seguras en espaГ±a
https://tadalafilo.pro/# farmacia online barata
colchicine for sale
https://vardenafilo.icu/# farmacia envÃos internacionales
https://tadalafilo.pro/# farmacia envГos internacionales
cheap levitra 40 mg
http://vardenafilo.icu/# farmacia online envÃo gratis
farmacias online baratas: precio cialis en farmacia con receta – farmacia online 24 horas
viagra us
http://vardenafilo.icu/# farmacias baratas online envÃo gratis
sildenafil 100mg genГ©rico comprar viagra sildenafilo precio farmacia
http://vardenafilo.icu/# farmacia online
https://sildenafilo.store/# sildenafilo cinfa 25 mg precio
http://kamagraes.site/# farmacia online
http://vardenafilo.icu/# farmacia online madrid
farmacia envГos internacionales: Levitra Bayer – farmacia online envГo gratis
https://farmacia.best/# farmacia 24h
https://vardenafilo.icu/# farmacias online baratas
https://farmacia.best/# farmacia envÃos internacionales
farmacia online 24 horas comprar cialis online seguro farmacias online baratas
http://kamagraes.site/# farmacia online
farmacia online envГo gratis: comprar cialis online seguro – п»їfarmacia online
http://vardenafilo.icu/# farmacias online baratas
https://sildenafilo.store/# comprar viagra en espaГ±a envio urgente contrareembolso
http://sildenafilo.store/# comprar viagra en españa
http://kamagraes.site/# farmacia envÃos internacionales
http://vardenafilo.icu/# farmacia online
http://farmacia.best/# farmacia envÃos internacionales
п»їfarmacia online farmacia online madrid farmacia 24h
farmacias online seguras en espaГ±a: Precio Levitra En Farmacia – farmacias online seguras
http://kamagraes.site/# farmacia online barata
http://kamagraes.site/# farmacia online barata
http://kamagraes.site/# farmacia online 24 horas
Alienatio mentis — Помрачение ума.
http://batmanapollo.ru
https://tadalafilo.pro/# farmacia barata
https://kamagraes.site/# farmacia online barata
farmacia barata: comprar cialis online sin receta – farmacias online baratas
http://tadalafilo.pro/# farmacias online baratas
п»їfarmacia online farmacia online envio gratis farmacia envГos internacionales
http://kamagraes.site/# farmacias online baratas
https://farmacia.best/# farmacias online seguras
diflucan 200 mg price
https://farmacia.best/# farmacia online 24 horas
http://farmacia.best/# farmacias online baratas
https://kamagraes.site/# farmacia online 24 horas
farmacia barata: kamagra oral jelly – farmacia online internacional
lexapro ocd
https://sildenafilo.store/# sildenafilo 50 mg comprar online
https://sildenafilo.store/# viagra online rápida
farmacias online seguras en espaГ±a farmacia online envio gratis farmacias online seguras
Pharmacie en ligne livraison rapide pharmacie ouverte acheter medicament a l etranger sans ordonnance
http://pharmacieenligne.guru/# Pharmacie en ligne livraison gratuite
farmacia online 24 horas: vardenafilo sin receta – farmacia online barata
http://kamagrafr.icu/# Pharmacie en ligne pas cher
http://cialissansordonnance.pro/# pharmacie en ligne
Pharmacie en ligne livraison rapide: pharmacie en ligne pas cher – Pharmacie en ligne livraison gratuite
Pharmacie en ligne fiable pharmacie en ligne acheter mГ©dicaments Г l’Г©tranger
https://cialissansordonnance.pro/# Pharmacie en ligne France
farmacia online madrid: farmacia online 24 horas – farmacia envГos internacionales
http://levitrafr.life/# Acheter médicaments sans ordonnance sur internet
http://pharmacieenligne.guru/# Pharmacie en ligne France
buy cheap synthroid
http://pharmacieenligne.guru/# acheter médicaments à l’étranger
Viagra en france livraison rapide: Meilleur Viagra sans ordonnance 24h – Viagra sans ordonnance 24h suisse
http://pharmacieenligne.guru/# Pharmacie en ligne France
acheter medicament a l etranger sans ordonnance kamagra 100mg prix Pharmacie en ligne pas cher
https://viagrasansordonnance.store/# Viagra sans ordonnance 24h
farmacias online seguras en espaГ±a: comprar cialis original – farmacia online internacional
http://cialissansordonnance.pro/# Pharmacie en ligne fiable
https://cialissansordonnance.pro/# Pharmacies en ligne certifiées
https://kamagrafr.icu/# Pharmacies en ligne certifiées
propranolol canadian pharmacy
Pharmacie en ligne sans ordonnance: Levitra pharmacie en ligne – Pharmacie en ligne sans ordonnance
https://levitrafr.life/# acheter médicaments à l’étranger
buy augmentin uk
https://viagrasansordonnance.store/# Sildénafil Teva 100 mg acheter
farmacia online 24 horas: kamagra – farmacia online internacional
Pharmacie en ligne livraison rapide tadalafil sans ordonnance Pharmacie en ligne livraison 24h
https://cialissansordonnance.pro/# Pharmacie en ligne livraison gratuite
https://kamagrafr.icu/# Pharmacie en ligne livraison rapide
https://pharmacieenligne.guru/# Pharmacie en ligne France
dapoxetine brand name
п»їpharmacie en ligne: tadalafil sans ordonnance – Pharmacie en ligne livraison gratuite
http://levitrafr.life/# Pharmacie en ligne pas cher
farmacias online baratas: comprar kamagra en espana – farmacia barata
baclofen pills 025 mg
https://kamagrafr.icu/# Pharmacie en ligne livraison rapide
SildГ©nafil Teva 100 mg acheter Meilleur Viagra sans ordonnance 24h Sildenafil teva 100 mg sans ordonnance
https://cialiskaufen.pro/# internet apotheke
versandapotheke versandkostenfrei Online Apotheke Deutschland online apotheke preisvergleich
propranolol online
http://apotheke.company/# online-apotheken
http://apotheke.company/# online apotheke versandkostenfrei
online apotheke versandkostenfrei cialis kaufen online-apotheken
https://kamagrakaufen.top/# online apotheke deutschland
Magnificent beat ! I wish to apprentice while you amend your site, how could i subscribe for a
blog website? The account aided me a acceptable deal. I had been a little bit
acquainted of this your broadcast offered bright clear
concept
http://viagrakaufen.store/# Viagra Generika 100mg rezeptfrei
internet apotheke: kamagra jelly kaufen deutschland – online apotheke deutschland
retin a tretinoin cream
gГјnstige online apotheke kamagra oral jelly п»їonline apotheke
baclofen generic lioresal
http://kamagrakaufen.top/# versandapotheke
I’m extremely inspired together with your writing abilities as neatly as with the format for your weblog.
Is this a paid theme or did you customize it yourself?
Either way stay up the excellent quality writing, it is rare to
peer a nice blog like this one these days..
https://cialiskaufen.pro/# п»їonline apotheke
cehhenemgeridondu.NuvCnsbvnX3PAtKe
uzuleceksinizya.BgPoREqG0uVU
pompaqe.Lg9HH4b71BOa
tornadodanselam.qtF4IVCjJJ2E
kenaragecin.YX1A6vAv0duH
versandapotheke deutschland: potenzmittel – versandapotheke
versandapotheke kamagra tabletten online apotheke preisvergleich
http://apotheke.company/# online apotheke versandkostenfrei
http://viagrakaufen.store/# Viagra Apotheke rezeptpflichtig
https://mexicanpharmacy.cheap/# buying prescription drugs in mexico
mexico pharmacies prescription drugs buying prescription drugs in mexico online mexico drug stores pharmacies
medicine in mexico pharmacies buying from online mexican pharmacy mexican pharmaceuticals online
mexican rx online mexico pharmacies prescription drugs mexico drug stores pharmacies
https://mexicanpharmacy.cheap/# pharmacies in mexico that ship to usa
mexican mail order pharmacies mexican pharmaceuticals online mexican pharmacy
best generic finasteride brand
pharmacies in mexico that ship to usa mexican mail order pharmacies mexican drugstore online
https://mexicanpharmacy.cheap/# mexico drug stores pharmacies
mexican mail order pharmacies mexican pharmaceuticals online buying prescription drugs in mexico
mexican online pharmacies prescription drugs mexico pharmacy buying prescription drugs in mexico online
deep web links dark web search engines darknet market links
mexican online pharmacies prescription drugs pharmacies in mexico that ship to usa medicine in mexico pharmacies
https://mexicanpharmacy.cheap/# mexican drugstore online
lisinopril cost uk
mexico pharmacies prescription drugs п»їbest mexican online pharmacies mexico drug stores pharmacies
buying prescription drugs in mexico online buying prescription drugs in mexico mexican mail order pharmacies
https://mexicanpharmacy.cheap/# mexico drug stores pharmacies
us trazodone cost
http://mexicanpharmacy.cheap/# best online pharmacies in mexico
Enjoyed studying this, very good stuff, thankyou. “A man does not die of love or his liver or even of old age he dies of being a man.” by Percival Arland Ussher.
mexican mail order pharmacies mexican mail order pharmacies mexico pharmacies prescription drugs
trazodone 50 mg brand name
mexican drugstore online mexico pharmacies prescription drugs mexican mail order pharmacies
vurucuteamgeldi.aNiVXpGLb5XF
vurucuteamgeldi.7lvkLO2b42VD
best mexican online pharmacies best mexican online pharmacies best mexican online pharmacies
buying from online mexican pharmacy mexican drugstore online mexico drug stores pharmacies
medication from mexico pharmacy mexico drug stores pharmacies mexican pharmaceuticals online
mexican rx online buying prescription drugs in mexico online purple pharmacy mexico price list
http://mexicanpharmacy.cheap/# mexican border pharmacies shipping to usa
buying prescription drugs in mexico reputable mexican pharmacies online best mexican online pharmacies
mexico drug stores pharmacies purple pharmacy mexico price list mexican drugstore online
mexico drug stores pharmacies mexican border pharmacies shipping to usa mexican online pharmacies prescription drugs
india pharmacy top online pharmacy india Online medicine home delivery indiapharmacy.guru
amoxicillin 250 mg pill
male ed drugs impotence pills – ed pills otc edpills.tech
drugs for ed erection pills – best male enhancement pills edpills.tech
india pharmacy mail order buy medicines online in india india pharmacy indiapharmacy.guru
https://edpills.tech/# cheap erectile dysfunction pills edpills.tech
1xbet’e giriş, kullanıcıların anlık maç sonuçlarını takip etmelerini sağlar.
1xbet giriş, mobil cihazlardan da rahatlıkla gerçekleştirilebilen bir işlemdir.
https://mexicanpharmacy.company/# mexican mail order pharmacies mexicanpharmacy.company
https://edpills.tech/# buying ed pills online edpills.tech
http://canadiandrugs.tech/# vipps canadian pharmacy canadiandrugs.tech
buy celexa online : Voltaren uk cymbalta 240 mg
celexa : proscar side effects augmentin duo 1000 mg
https://indiapharmacy.guru/# indian pharmacies safe indiapharmacy.guru
crestor 10 mg generic : baclofen 10 mg tablet buy strattera online fedex
natural ed remedies best male enhancement pills – ed treatments edpills.tech
finpecia fast delivery overnight : buy ventolin evohaler online cymbalta 20 mg cost
http://canadiandrugs.tech/# legit canadian pharmacy canadiandrugs.tech
drugs for ed medicine for impotence – ed meds edpills.tech
Thanks for sharing. I read many of your blog posts, cool, your blog is very good. https://accounts.binance.com/ph/register-person?ref=V2H9AFPY
paxil on sale : buy valtrex from india online plavix 600 mg
best india pharmacy mail order pharmacy india Online medicine order indiapharmacy.guru
allegra how many mg : 1000 mg tetracycline vermox walgreens
http://edpills.tech/# best treatment for ed edpills.tech
abilify : effexor without prescriptions zyprexa olanzapine 10 mg
prometrium 400 mg side effects : finpecia generic Nolvadex uk
https://indiapharmacy.guru/# indianpharmacy com indiapharmacy.guru
chlomid nolvadex supplier : Tinidazole us lisinopril 10 mgs
https://indiapharmacy.guru/# Online medicine home delivery indiapharmacy.guru
phenergan suppository : periactine acheter en ligne lamisil liquid
cheap viagra and proscar : pharmacy world periactin Celebrex online
http://edpills.tech/# new treatments for ed edpills.tech
syrup augmentin duo : provera for sale uk paxil 10mg
https://canadiandrugs.tech/# reputable canadian pharmacy canadiandrugs.tech
cheap erectile dysfunction pill buy ed pills – pills erectile dysfunction edpills.tech
online shopping pharmacy india top 10 online pharmacy in india buy prescription drugs from india indiapharmacy.guru
buy medicines online in india best online pharmacy india – top online pharmacy india indiapharmacy.guru
https://canadiandrugs.tech/# canada drugstore pharmacy rx canadiandrugs.tech
methotrexate 2.5 mg cost : nolvadex for sale canada buy phenergan online no prescription
https://canadiandrugs.tech/# canada drugs online canadiandrugs.tech
http://indiapharmacy.pro/# indian pharmacies safe indiapharmacy.pro
https://edpills.tech/# ed pills cheap edpills.tech
http://canadiandrugs.tech/# canadian pharmacy sarasota canadiandrugs.tech
tretinoin cream price comparison
https://edpills.tech/# medication for ed edpills.tech
buy medicines online in india india online pharmacy best india pharmacy indiapharmacy.guru
Your point of view caught my eye and was very interesting. Thanks. I have a question for you. https://www.binance.com/bg/register?ref=P9L9FQKY
http://canadiandrugs.tech/# recommended canadian pharmacies canadiandrugs.tech
cross border pharmacy canada canadian pharmacy scam – canadian drug pharmacy canadiandrugs.tech
the canadian drugstore cheap canadian pharmacy online – canadian king pharmacy canadiandrugs.tech
http://canadiandrugs.tech/# safe reliable canadian pharmacy canadiandrugs.tech
https://canadiandrugs.tech/# www canadianonlinepharmacy canadiandrugs.tech
https://edpills.tech/# best over the counter ed pills edpills.tech
https://indiapharmacy.guru/# Online medicine home delivery indiapharmacy.guru
best india pharmacy mail order pharmacy india buy prescription drugs from india indiapharmacy.guru
https://edpills.tech/# buying ed pills online edpills.tech
https://indiapharmacy.pro/# online pharmacy india indiapharmacy.pro
http://indiapharmacy.guru/# indian pharmacies safe indiapharmacy.guru
canada pharmacy online canadian drug pharmacy – online canadian pharmacy canadiandrugs.tech
http://edpills.tech/# erection pills viagra online edpills.tech
online ed medications pills for erection – pills for ed edpills.tech
https://indiapharmacy.guru/# best online pharmacy india indiapharmacy.guru
top rated ed pills best ed pills non prescription male ed pills edpills.tech
http://canadiandrugs.tech/# canadian pharmacy 365 canadiandrugs.tech
http://indiapharmacy.guru/# online shopping pharmacy india indiapharmacy.guru
tetracycline hcl 500 mg : buy Voltaren online Singulair usa
discount proscar : augmentin 875 mg tab amoxil 250 mg per 5 cc
phenergan 50 mgs : Lamisil usa provera 2.5 mg
https://indiapharmacy.guru/# indian pharmacies safe indiapharmacy.guru
Bactrim usa : motrin 600mg prevacid 60 mg side effects
https://indiapharmacy.guru/# top 10 pharmacies in india indiapharmacy.guru
buy suprax online no prescription : how chelation in tetracyclines benicar 40 25 mg
best online pharmacy india cheapest online pharmacy india – pharmacy website india indiapharmacy.guru
http://ciprofloxacin.life/# buy cipro
https://clomid.site/# cost clomid without rx
prednisone for cheap: online order prednisone 10mg – prednisone buying
paxlovid pharmacy paxlovid covid buy paxlovid online
Последние тенденции в сфере микрофинансирования демонстрируют увеличение спроса на быстрые займы. Это связано с ускорением ритма жизни и необходимостью в срочных финансовых решениях. Мы в https://t.me/microzaimfun/ помогаем пользователям ориентироваться в мире быстрых финансовых услуг, предоставляя надежную и актуальную информацию.
buy ciprofloxacin over the counter: purchase cipro – buy cipro cheap
ciprofloxacin: ciprofloxacin mail online – cipro online no prescription in the usa
amoxicillin 500 mg purchase without prescription: amoxicillin 500 – buy amoxicillin 500mg online
http://paxlovid.win/# buy paxlovid online
generic accutane : buy isotretinoin no prescription purchase accutane isotretinoin2024x7.top
cipro for sale: buy generic ciprofloxacin – ciprofloxacin
buy prednisone without prescription purchase prednisone canada prednisone 10 tablet
https://isotretinoin2024x7.top/# – canadian online pharmacies prescription drugs isotretinoin2024x7.top
purchase cipro: ciprofloxacin mail online – purchase cipro
http://clomid.site/# clomid for sale
buy isotretinoin no prescription : accutane cheap buy accutane online usa isotretinoin2024x7.top
cipro generic: buy cipro online canada – ciprofloxacin
https://isotretinoin2024x7.top/# – best mail order pharmacies isotretinoin2024x7.top
accutane 30 mg coupon
buy accutane canada pharmacy : buy accutane medication buy accutane online isotretinoin2024x7.top
amoxacillian without a percription: amoxicillin no prescipion – cost of amoxicillin 875 mg
https://isotretinoin2024x7.top/# – buying drugs canada isotretinoin2024x7.top
where can i buy amoxicillin over the counter uk: amoxicillin without a prescription – amoxicillin 500 mg price
buy accutane : purchase accutane cheap accutane 40 mg isotretinoin2024x7.top
https://isotretinoin2024x7.top/# – generic drug prices isotretinoin2024x7.top
amoxicillin 500 mg brand name: amoxicillin online without prescription – ampicillin amoxicillin
can i order cheap clomid prices buying generic clomid no prescription can you buy cheap clomid now
buy isotretinoin : accutane generic buy accutane medication isotretinoin2024x7.top
http://clomid.site/# get generic clomid without dr prescription
https://isotretinoin2024x7.top/# – pharcharmy online no precipitation isotretinoin2024x7.top
paxlovid generic: buy paxlovid online – paxlovid pharmacy
https://erectiledysfunctionpills-247.top/# – cost medications erectiledysfunctionpills-247.top
prednisone uk over the counter: buy prednisone online uk – prednisone 5 mg cheapest
best erectile dysfunction pills : ed pills online ed pills online erectiledysfunctionpills-247.top
compare prednisone prices: prednisone acetate – 100 mg prednisone daily
https://erectiledysfunctionpills-247.top/# – online canadian discount pharmacy erectiledysfunctionpills-247.top
buy ed pills usa : ed pills online buy ed pills cheap erectiledysfunctionpills-247.top
amoxicillin where to get: where to buy amoxicillin over the counter – amoxicillin 500mg capsules
https://erectiledysfunctionpills-247.top/# – northwestpharmacy erectiledysfunctionpills-247.top
deep web search dark web market darknet sites
https://paxlovid.win/# paxlovid price
darkmarket 2024 deep web sites tor market
ciprofloxacin: ciprofloxacin mail online – buy cipro online canada
ed pills online : ed pills online buy ed pills medication erectiledysfunctionpills-247.top
darknet drug store darknet search engine darknet market links
875 mg amoxicillin cost amoxicillin brand name amoxicillin online pharmacy
dark website dark web drug marketplace deep web drug store
lioresal 10 mg price
https://erectiledysfunctionpills-247.top/# – mail order prescriptions from canada erectiledysfunctionpills-247.top
dark web search engines tor marketplace darknet links
where to buy amoxicillin 500mg
Привет! Знаешь, иногда всем нам нужна небольшая финансовая поддержка. Онлайн займы на карту без отказа – это как дружеская помощь в трудную минуту. Без проверок, без лишних вопросов – просто выбери сумму, и деньги появятся на твоей карте. Удобно, правда?
Срочно нужны деньги? На microzaim.fun предложены займы круглосуточно на карту без отказа , которые помогут вам в трудную минуту.
Рынок микрофинансирования продолжает расширяться: более 40 новых МФО готовы предложить займы на сумму до 30 000 рублей. Процедура получения денег максимально упрощена – требуется только паспорт. Это отличная новость для тех, кто ищет быстрое и удобное финансовое решение.
Обратите внимание на предложения займов без отказа на карту на сайте microzaim.fun, где каждый найдет оптимальное решение для своих финансовых нужд.
paxlovid buy: buy paxlovid online – paxlovid
ed pills online : ed pills ed meds erectiledysfunctionpills-247.top
citalopram india
https://prednisone.bid/# generic prednisone cost
Paxlovid buy online: paxlovid buy – paxlovid
cheap clomid without insurance: where to get clomid without insurance – can you get generic clomid for sale
vardenafil 20 mg price
buy generic prednisone online prednisone 1 mg daily 6 prednisone
paxlovid pharmacy: paxlovid india – paxlovid generic
buy finasteride : buy propecia no rx buy generic propecia
how to get generic clomid: how can i get generic clomid – buy generic clomid without dr prescription
buy xenical
https://propecia2024x7.top/# – buy propecia online uk
buy propecia uk : purchase finasteride buy propecia
https://propecia2024x7.top/# – is it illegal to buy propecia online
propecia : order propecia propecia
prednisone generic brand name where to get prednisone 5mg prednisone
https://propecia2024x7.top/# – buy propecia usa
https://prednisone.bid/# prednisone 40mg
buy propecia online : buy propecia usa purchase propecia
https://propecia2024x7.top/# – where do i buy propecia
buy finasteride pills : buy propecia pills finasteride
https://propecia2024x7.top/# – best place to buy generic propecia online
Incredible, blog yang luar biasa! 🌟 Saya sangat terkesan dengan kontennya yang informatif dan menghibur. Setiap artikel memberikan wawasan baru dan inspiratif. 🚀 Saya sungguh-sungguh menikmati membaca setiap kata. Semangat terus! 👏 Sudah tidak sabar untuk membaca konten mendatang. 📚 Terima kasih atas kontribusinya dalam berbagi pengetahuan yang memberi manfaat dan menginspirasi. 💡🌈 Keep up the great work! linetogel 🙌
buy propecia pills : buy propecia no rx buy generic propecia
where to get amoxicillin over the counter: generic amoxicillin 500mg – can i buy amoxicillin online
https://propecia2024x7.top/# – buy propecia at walmart
vardenafil buy
xyandanxvurulmus.oeVo7BYnawYH
Холоп 2 актеры. Холоп 2 скачать торрент. Холоп 2 смотреть. Холоп 2 когда выйдет. Фильм холоп. Где найти фильм холоп в хорошем качестве бесплатно. Холоп фильм 2024 смотреть онлайн. Фильм холоп смотреть онлайн бесплатно в хорошем качестве. Смотреть фильм холоп.
xbunedirloooo.E9Dd615CFgj3
Wah, ini luar biasa! Seperti angin sepoi-sepoi membersihkan tanah kebijaksanaan. 💨🧠 #IndosneioAnginKebijaksanaan
buy cipro buy ciprofloxacin ciprofloxacin 500mg buy online
http://clomid.site/# can i order cheap clomid pills
flacons xyandanxvurulmus.wgekXbjNcCzB
generic amoxicillin cost amoxicillin 500mg price amoxicillin 500mg no prescription
buy amoxicillin canada: where can i get amoxicillin – amoxicillin capsules 250mg
ciprofloxacin generic price: cipro ciprofloxacin – purchase cipro
Начиная с 2023 года, многие МФО предлагают займы на карту без отказа, участвуя в акции “без процентов на 30 дней”. Это привлекательное предложение для тех, кто ищет экономичный способ решения своих временных финансовых проблем. Благодаря этой акции, заемщики могут получить нужную сумму без переплаты, что делает такие займы исключительно выгодными.
acheter du clamoxil : aciclovir dosis lisinopril price
Книги лидерство купить. Креативное лидерство. Харизматичный тип лидерства. Назовите виды лидерства. Формальное лидерство может быть охарактеризовано как управленческий статус. Типы лидерства обществознание егэ.
Новые онлайн займы на карту без отказа представляют собой уникальную возможность для тех, кто нуждается в срочной финансовой помощи. Эти займы отличаются от традиционных кредитных продуктов своей доступностью и удобством оформления. Главное преимущество новых онлайн займов заключается в том, что они предлагают мгновенное решение по заявке и быстрый перевод средств на карту, что делает их идеальным выбором для срочных финансовых нужд. МФО, предоставляющие такие займы, стремятся максимально упростить процесс оформления и ускорить получение денег.
Начиная с 2023 года, многие МФО предлагают займы на карту без отказа, участвуя в акции “без процентов на 30 дней”. Это привлекательное предложение для тех, кто ищет экономичный способ решения своих временных финансовых проблем. Благодаря этой акции, заемщики могут получить нужную сумму без переплаты, что делает такие займы исключительно выгодными.
http://finasteridexl.com/# – tetracycline online
canada zovirax acyclovir : buspar weight gain buy finpecia india
http://finasteridexl.com/# – mg of neurontin
bactrim cold sore : plavix 600 mg flomax 64 mg
cost of clonidine
http://finasteridexl.com/# – buy Arimidex
pygmyisms xyandanxvurulmus.yEmx4iRJshPz
nolvadex uk paypal : do you need a prescription for lamisil depo provera et duphaston
В современном мире займы онлайн на карту являются одним из самых удобных и быстрых способов получения денежных средств. Они особенно популярны среди людей, которым срочно нужны деньги для решения финансовых проблем. Преимущество таких займов в том, что оформить их можно в любое время суток, не выходя из дома. Благодаря автоматизированным системам рассмотрения заявок, клиенты получают деньги на карту в кратчайшие сроки, что делает этот вариант кредитования особенно привлекательным.
where can i buy diflucan without a prescription
Многофакторный опросник лидерства. Управление и лидерство статья. Стили политического лидерства. Резонансное лидерство. Теория ситуационного лидерства херси бланшара. Модель ситуационного лидерства. Тренинг по лидерству.
https://mexicopharmacy.top/# – strattera 60 mg vs adderall
В современном мире займы онлайн на карту являются одним из самых удобных и быстрых способов получения денежных средств. Они особенно популярны среди людей, которым срочно нужны деньги для решения финансовых проблем. Преимущество таких займов в том, что оформить их можно в любое время суток, не выходя из дома. Благодаря автоматизированным системам рассмотрения заявок, клиенты получают деньги на карту в кратчайшие сроки, что делает этот вариант кредитования особенно привлекательным.
generic plavix release date : buying oral ampicillin lipitor form liquid
Среди новых финансовых продуктов 2023 года особое внимание заслуживает предложение займ на карту онлайн, в рамках которого многие МФО предоставляют займы без процентов на 30 дней. Это великолепная возможность для тех, кто нуждается в срочном финансировании, но не желает переплачивать. С такими условиями заемщики получают удобный доступ к необходимым средствам, не беспокоясь о дополнительных расходах.
https://mexicopharmacy.top/# – lipitor 20 mgs
lisinopril 20 mg order online : buy tadacip online lipitor 1o mg cheap prices
Подходит Новый год, и многие ищут возможности для финансирования праздничных расходов. Займы онлайн новый год – это отличный вариант для тех, кто хочет быстро решить финансовые вопросы без лишних хлопот. МФО предлагают удобные онлайн-заявки и быстрое решение по кредиту, что позволяет заемщикам получить необходимую сумму в кратчайшие сроки и насладиться праздником без финансовых забот.
В 2023 году рынок финансовых услуг представляет займ 2023 год новые без отказа, где более 40 ведущих МФО готовы предоставить быстрые финансовые решения. Эти займы отличаются простотой оформления и быстрым получением денег на карту. Они идеально подходят для тех, кто нуждается в срочном финансировании, с минимальными требованиями к заемщикам и высоким уровнем одобрения.
https://mexicopharmacy.top/# – flomax cap 04mg
paxil 2 mg : prevacid dr 30 mg robaxin 750 mg price
Sungguh luar biasa! 🚀 Kontennya sangat menarik dan penuh semangat. 🌟 Artikel yang benar-benar menginspirasi! 👏 Terus berbagi wawasan yang bermanfaat! 🤩💯 Sungguh memikat hati! 🌈 Terima kasih terima kasih banyak! 🙌✨ #Inspiratif #SemangatBaru #Istimewa
https://mexicopharmacy.top/# – astrazeneca nolvadex rx
where to buy aciphex in canada online : levaquin 250 mg celexa 40 mg 30 pills
Hebat, blog ini keren banget! 🚀 Isinya energik dan bersemangat. 🌟 Selalu menemukan sesuatu yang baru dan menarik di sini. 👏 Teruskan semangat berbagi! 🤩💯 Artikel ini sungguh memikat hati! 🌈 Terima kasih atas inspirasinya! 🙌✨ #EnergiTinggi #Informatif #PenuhKepuasan
https://mexicopharmacy.top/# – plavix 75mg online
Плохая кредитная история больше не препятствие для получения кредита. Наше МФО предлагает кредиты до 30 000 рублей без отказа, с мгновенным решением по заявке. Мы понимаем, что каждый может столкнуться с финансовыми трудностями, и готовы поддержать вас в такие моменты. Процесс оформления максимально упрощен и не требует много времени.
У нас вы найдете микрозайм без отказов мгновенно и другие предложения от МФО 2024 года! Каждый сможет получить быстрый займ в онлайн режиме без проверок и отказов.
seroquel xr 150 mg side effects : purchase generic valtrex buy methotrexate no prescription
https://mexicopharmacy.top/# – methotrexate calculator
Мгновенные займы без процентов теперь доступны круглосуточно. Это идеальное решение для тех, кто сталкивается с финансовыми трудностями в неподходящее время. Наш сервис предоставляет возможность получить необходимые средства без лишних затрат и временных затруднений. Процедура займа максимально упрощена, чтобы вы могли решить свои финансовые вопросы мгновенно.
У нас вы найдете займ всем без отказа на карту и другие предложения от МФО 2024 года! Каждый сможет получить быстрый займ в онлайн режиме без проверок и отказов.
Вам нужны деньги срочно? Воспользуйтесь нашим удобным сервисом, предлагающим выбор из более чем 40 МФО. Новым клиентам мы предоставляем кредиты под 0% с моментальной выдачей на банковскую карту. Всё, что от вас требуется – это паспорт. Наслаждайтесь простотой и скоростью получения кредита без лишних затрат.
У нас вы найдете займ на карту без отказа без проверки мгновенно и другие предложения от МФО 2024 года! Каждый сможет получить быстрый займ в онлайн режиме без проверок и отказов.
singulair cena : dosing 800mg zovirax cold sores overnight baclofen
https://lioresal2world.top/# – nolvadex sold in canada
Представляем вашему вниманию уникальное предложение: займы без процентов, доступные в любое время суток. Забудьте о высоких процентах и скрытых комиссиях. Наш сервис обеспечивает быстрое получение средств с полной прозрачностью условий. Быстрый доступ к финансам без лишних издержек – это реальность с нашими займами.
У нас вы найдете мфо онлайн и другие предложения от МФО 2024 года! Каждый сможет получить быстрый займ в онлайн режиме без проверок и отказов.
where to buy motilium online : Zovirax uk buy lisinopril 12.5
https://lioresal2world.top/# – amoxil 250 mg dosage
kirkland allergy pills toronto skin allergy tablets list otc allergy medication comparison chart
Lamisil online : atarax 25 mg dosage nolvadex shipped to canada
how to buy cheap clomid price where to get generic clomid price – can i get cheap clomid pills
https://lioresal2world.top/# – purchasing inderal
buy suhagra india : lamisil pills lisinopril sales
https://ciprofloxacin.life/# ciprofloxacin mail online
http://amoxil.icu/# buy amoxicillin canada
cost of prozac generic
where buy generic clomid pill where buy generic clomid prices – get generic clomid tablets
https://amoxil.icu/# cheap amoxicillin 500mg
https://lioresal2world.top/# – valtrex generic no prescription
20 mg of prednisone: buying prednisone mexico – canada pharmacy prednisone
https://amoxil.icu/# amoxicillin 500mg pill
2700 mg gabapentin
cymbalta 60 mg discount card : nizoral ad cheap buy suhagra 50
prednisone 50 mg buy: steroids prednisone for sale – prednisone tablet 100 mg
https://lioresal2world.top/# – aciphex over the counter
Если вы рассматриваете новые мфо только открывшиеся без отказа на карту, обратите внимание на условия предоставления займов. Удостоверьтесь, что полностью понимаете все аспекты договора. Особое внимание стоит уделить процедуре взимания платежей и возможным штрафам за просрочку платежей.
levaquin tablet 750 mg : buy tetracycline without prescription celexa 20 mg anxiety
https://lioresal2world.top/# – cephalexin 500 mg from canada
Для тех, кто ищет финансовую поддержку, важно знать о возможностях, которые предоставляют новые мфо 2024 года. Прежде всего, убедитесь, что вы выбираете надежную организацию. Проверьте отзывы клиентов и условия займа, включая процентные ставки и сроки погашения. Не забудьте также оценить свои финансовые возможности, чтобы избежать непредвиденных задолженностей.
А знаете, что еще поразительно? Новые мфо только открывшиеся без отказа на карту онлайн без звонков – они настоящие герои нашего времени! Представьте, вы можете получить займ, не отвлекаясь от ваших ежедневных дел. Никаких звонков, никаких вопросов, только вы, ваш смартфон и несколько кликов. Невероятно, правда?
glucophage 850mg : cheap Tetracycline finpecia cheap pepricie
http://amoxil.icu/# over the counter amoxicillin canada
where to buy generic clomid without rx: can you buy clomid no prescription – can i order clomid tablets
https://lioresal2world.top/# – Abilify usa
И наконец, если совсем зашкаливает срочность, то срочно займ без отказа – настоящий спасательный круг!
bactrim cheap : neurontin 300mg warnings tetracycline antibiotics canada
Luar biasa blog ini! 🌟 Saya sangat menyukai bagaimana penulisannya memberikan pengetahuan yang mendalam dalam topik yang dibahas. 👌 Artikelnya menyajikan hiburan dan edukasi sekaligus. 📖 Tiap artikel membuat saya lebih penasaran untuk membaca yang lainnya. Teruskan karya hebat
https://lioresal2world.top/# – buy paxil cr no prescription
https://ciprofloxacin.life/# п»їcipro generic
how to get clomid no prescription: cost of clomid prices – how can i get cheap clomid no prescription
Пришла пора покупки долгожданного автомобиля, но в банках отказывали из-за моей кредитной истории. Отчаявшись, я нашел на сайте мир-займов.рф микрозайм на карту без отказа. Благодаря большому выбору МФО, даже с моей испорченной кредитной историей, я получил нужную сумму.
Чтобы осуществить давнюю мечту о покупке лодки, мне понадобился дополнительный заем. На сайте мир-займов.рф я нашел займ с плохой кредитной историей без отказа, который помог мне воплотить мечту в реальность.
Важно подчеркнуть, что современные малоизвестных мфо дающие онлайн на карту стали доступнее. Оперативность получения финансовой помощи теперь не ограничивается временем и местом. Всё, что требуется от клиента – доступ в интернет и несколько минут свободного времени. Это идеальное решение для тех, кто ценит своё время и предпочитает быстрое обслуживание без лишних бумажных формальностей.
seroquel xr 400 mg tablet : can i take ibuprofen with buspar buy Silagra online
brillx casino официальный мобильная версия
brillx казино
Brillx Казино — ваш уникальный путь к захватывающему миру азартных игр в 2023 году! Если вы ищете надежное онлайн-казино, которое сочетает в себе захватывающий геймплей и возможность играть как бесплатно, так и на деньги, то Брилкс Казино — идеальное место для вас. Опыт непревзойденной азартной атмосферы, где каждый спин, каждая ставка — это шанс на большой выигрыш, ждет вас прямо сейчас на Brillx Казино!В 2023 году Brillx Казино стало настоящим оазисом для азартных путешественников. Подарите себе незабываемые моменты радости и азарта. Не упустите свой шанс сорвать куш и стать частью легендарной истории на страницах брилкс казино.
https://lioresal2world.top/# – nizoral 200 mg tab
aciclovir tablets without prescription : ampicillin drug paxil cr 12.5 mgs
https://lioresal2world.top/# – is singulair over the counter
can you inject buspar : avodart bestellen zonder recept norvasc 5mg tab
Когда вы ищете малоизвестные мфо, обратите внимание на их предложения займов под 0% до 30 000 рублей. Процесс получения займа удивительно прост: нужен только паспорт и возраст от 18 лет. Это идеальный вариант для тех, кто нуждается в срочных деньгах без лишних хлопот.
Как-то раз мне захотелось устроить сюрприз для своей девушки и приготовить романтический ужин. Чтобы купить все необходимые ингредиенты, я использовал займ без отказа с сайта мир-займов.рф.
https://lioresal2world.top/# – lisinopril amlodipine combination
paxil 40 mg tablet : lamisil crema marfan syndrome norvasc 5 mg
https://lioresal2world.top/# – buy Ventolin
buy methotrexate without prescription : suprax online canada paxil 37.5 mg for sale
https://mexicopharm.top/# – phenergan suppository
order phenergan online : florida celexa mg 20 ordering benicar online
https://mexicopharm.top/# – lipitor 10 mg
flomax 20 mg : periactin vs cb1 voltaren gel generic
https://mexicopharm.top/# – ventolin inhalador
finasteride 1mg
The article was informative and well-written. More visuals could add another dimension, and my website could provide some inspiration.
where to buy propecia online in canada
Can you be more specific about the content of your article? After reading it, I still have some doubts. Hope you can help me. https://www.binance.com/ka-GE/register?ref=JHQQKNKN
В последнее время лучшие дорамы завоевывают интернет. Эти сериалы, сочетающие в себе драматизм, романтику и юмор, становятся неотъемлемой частью культурного диалога. Они предлагают зрителям новый способ погружения в истории, которые развиваются не по обычному сценарию, а привносят что-то новое и неожиданное.
http://nolvadex.fun/# nolvadex price
buy Robaxin online : fast delivery valtrex online lipitor 40mg picture
where can i buy zithromax capsules: buy generic zithromax no prescription – zithromax 250 price
Good read! A bit more in terms of visual content could really elevate it. Have a look at my website for potential ideas.
nolvadex half life: is nolvadex legal – tamoxifen hot flashes
Deep analysis! I am interested in writing for the blog.
https://mexicopharm.top/# – phenergan for stomach virus
В мире, где каждый уголок наполнен историями, дорамы словно магические окна, открывающие нам неизведанные земли. Каждый эпизод – это путешествие в сердце Азии, где чувства и судьбы переплетаются в удивительный узор жизни.
Многие скептически относятся к азиатским сериалам, но вот почему стоит дать шанс дорамам онлайн: они предлагают уникальное сочетание драмы и комедии, погружая вас в другую культуру и менталитет. Их особенность в том, что они могут одновременно развлекать и заставлять задуматься.
Деструктивное лидерство. Лидерство и командообразование. Лидерство процесс социального влияния благодаря которому. Ситуационная теория лидерства это. Полит лидерство. Атрибутивное лидерство. Джон максвелл 21 неопровержимый закон лидерства. Харизматическое лидерство это. Тренинг лидерства.
where to buy celexa : buy buspar without prescription side effects of flomax o 4mg
https://mexicopharm.top/# – silagra australia
http://lisinoprilbestprice.store/# lisinopril tabs 10mg
Cytotec 200mcg price: buy cytotec in usa – cytotec buy online usa
tamoxifen hormone therapy: tamoxifen 20 mg tablet – does tamoxifen cause joint pain
https://doxycyclinebestprice.pro/# doxycycline generic
Каждая новая дорама – это окно в другой мир, где каждая сцена, каждый персонаж оживает и рассказывает свою уникальную историю. Погрузись в этот мир, полный красочных культур, глубоких эмоций и невероятных приключений. Открой для себя новые горизонты и переживи каждый момент вместе с героями, исследуя их мир, полный загадок и красоты.
Некоторые думают, что новые дорамы – это просто ещё одни сериалы. Однако они ошибаются. Новые дорамы – это истории, которые раскрывают перед нами мир полный чувств, эмоций и неожиданных поворотов. Они учат нас взглянуть на жизнь под другим углом и оценить её во всех её проявлениях.
order cheap lisinopril cheap lisinopril 40 mg zestril 10
https://lisinoprilbestprice.store/# lisinopril price 10 mg
aromatase inhibitors tamoxifen: tamoxifen – nolvadex during cycle
Закажите перетяжку мягкой мебели с гарантией качества
Обновление мягкой мебели: простой способ обновить интерьер
Качественное обслуживание перетяжки мягкой мебели
Легко и просто обновить диван или кресло
перетяжка мебели https://www.peretyazhkann.ru.
doxy: doxycycline tablets – buy doxycycline without prescription uk
zestril 5 mg tablets: zestril 5 mg prices – 60 mg lisinopril
http://cytotec.icu/# buy cytotec online
http://doxycyclinebestprice.pro/# 100mg doxycycline
augmentin 1000 mg tablet price
can you buy zithromax over the counter in mexico: buy zithromax online – zithromax pill
В хорошем качестве смотреть фильмы онлайн. Смотреть фильмы онлайн. Фильмы онлайн — сайт. Смотреть онлайн-кинотеатры. Фильмы смотреть онлайн бесплатно в HD1080. Легально ли смотреть фильмы онлайн?
cost of doxycycline 100mg in india
zestril 20 mg price: how to order lisinopril online – buy lisinopril 20 mg without a prescription
does tamoxifen cause weight loss nolvadex only pct nolvadex 10mg
http://zithromaxbestprice.icu/# zithromax 500 tablet
buy doxycycline online: doxycycline 100 mg – doxycycline 100 mg
В эпоху цифровых технологий получение финансовой помощи стало еще проще и доступнее. На expl0it.ru мы предлагаем вам микрозайм онлайн на карту без отказа, который является оптимальным решением для тех, кто ценит свое время и комфорт. Процесс заявки полностью автоматизирован, что обеспечивает быстрое решение вашего запроса. Мы понимаем важность надежности и доступности, поэтому предоставляем услуги, соответствующие самым высоким стандартам.
https://zithromaxbestprice.icu/# where to buy zithromax in canada
http://zithromaxbestprice.icu/# zithromax 500mg
zestril 10 mg cost: lisinopril 5mg buy – zestril price in india
buy cytotec online fast delivery: buy cytotec pills – Cytotec 200mcg price
buy doxycycline online uk buy doxycycline without prescription uk buy doxycycline
Abortion pills online: order cytotec online – buy cytotec online
https://nolvadex.fun/# how to lose weight on tamoxifen
http://mexicopharm.com/# mexican rx online mexicopharm.com
https://canadapharm.life/# canadian pharmacies comparison canadapharm.life
canadian pharmacy store: Canada pharmacy online – canadian pharmacies compare canadapharm.life
cheap viagra for sale canada
VPS VDS на Windows
– Windows – 2012 R2, 2016, 2019, 2022 – бесплатно
– FASTPANEL Рё HestiaCP – бесплатно
– Мгновенное развёртывание сервера РІ несколько кликов – бесплатно
– Супер (аптайм, скорость, РїРёРЅРі, нагрузка)
– Windows – 2022, 2019, 2016, 2012 R2
– Для сервера сеть РЅР° скорости 1 Гбит!
– Отлично РїРѕРґС…РѕРґРёС‚ РїРѕРґ A-Parser
– Дата-центр РІ РњРѕСЃРєРІРµ Рё Амстердаме
– Почасовая оплата
– Быстрые серверы СЃ NVMe.
– Ubuntu, Debian, CentOS, Oracle 9 – бесплатно
– Отлично РїРѕРґС…РѕРґРёС‚ РїРѕРґ CapMonster
– Более 15 000 сервер уже РІ работе
– Отлично РїРѕРґС…РѕРґРёС‚ РїРѕРґ Xneolinks
– Outline VPN, WireGuard VPN, IPsec VPN.
– Автоматическая установка Windows – бесплатно
– Управляйте серверами РЅР° лету.
– Отлично РїРѕРґС…РѕРґРёС‚ РїРѕРґ GSA Search Engine Ranker
– Отлично РїРѕРґС…РѕРґРёС‚ РїРѕРґ XRumer + XEvil
– Возможность арендовать сервер РЅР° 1 час или 1 сутки
– Скорость порта подключения Рє сети интернет — 1000 РњР±РёС‚/сек
– Круглосуточная техническая поддержка – бесплатно
В лабиринте жизненных обстоятельств иногда требуется надежный компас, указывающий путь к финансовой стабильности. Expl0it.ru предлагает вам этот компас в виде возможности взять займы. Каждый шаг к оформлению займа – как шаг к осуществлению мечты, каждое решение – как ключ к новым возможностям. Вдохновляйтесь свободой выбора и возможностью действовать, не оглядываясь на финансовые преграды.
Ищете надежный источник финансирования? На expl0it.ru вы найдете займы, которые станут вашим надежным помощником в любой финансовой ситуации. Мы предлагаем простые и прозрачные условия, быстрое одобрение и удобное оформление займа. Воспользуйтесь нашими услугами, чтобы обеспечить себе финансовую свободу и стабильность.
Ищете что-то, что заставит ваше сердце трепетать от волнения? Турецкий сериал смотреть онлайн на русском на TurkFan.tv – это ваш ключ к миру эмоциональных переживаний и захватывающих сюжетов. Каждый сериал – это путешествие, полное любви, предательства, дружбы и испытаний, которые перевернут ваше представление о драматургии. С TurkFan.tv вы становитесь частью каждой истории, живете каждым персонажем и переживаете каждый момент вместе с ними. Наслаждайтесь непревзойденным качеством и удобством просмотра, которые делают каждый просмотр незабываемым.
trustworthy canadian pharmacy: canada drug pharmacy – canadian pharmacy no scripts canadapharm.life
mexican mail order pharmacies Purple Pharmacy online ordering mexican mail order pharmacies mexicopharm.com
canada drugs: Canadian online pharmacy – 77 canadian pharmacy canadapharm.life
https://mexicopharm.com/# mexico pharmacy mexicopharm.com
🌌 Wow, blog ini seperti roket meluncurkan ke alam semesta dari keajaiban! 💫 Konten yang menarik di sini adalah perjalanan rollercoaster yang mendebarkan bagi imajinasi, memicu kegembiraan setiap saat. 🌟 Baik itu gayahidup, blog ini adalah harta karun wawasan yang menarik! #KemungkinanTanpaBatas 🚀 ke dalam petualangan mendebarkan ini dari imajinasi dan biarkan pikiran Anda terbang! ✨ Jangan hanya mengeksplorasi, alami sensasi ini! 🌈 Pikiran Anda akan bersyukur untuk perjalanan mendebarkan ini melalui alam keajaiban yang penuh penemuan! 🌍
🌌 Wow, blog ini seperti perjalanan kosmik meluncur ke galaksi dari kegembiraan! 🌌 Konten yang menarik di sini adalah perjalanan rollercoaster yang mendebarkan bagi pikiran, memicu kegembiraan setiap saat. 💫 Baik itu inspirasi, blog ini adalah sumber wawasan yang menarik! 🌟 Berangkat ke dalam petualangan mendebarkan ini dari imajinasi dan biarkan pemikiran Anda berkelana! 🚀 Jangan hanya mengeksplorasi, rasakan kegembiraan ini! #BahanBakarPikiran 🚀 akan bersyukur untuk perjalanan menyenangkan ini melalui ranah keajaiban yang menakjubkan! 🌍
india online pharmacy: Medicines from India to USA online – Online medicine home delivery indiapharm.llc
mexican pharmacy: Purple Pharmacy online ordering – mexico pharmacy mexicopharm.com
http://mexicopharm.com/# buying from online mexican pharmacy mexicopharm.com
https://indiapharm.llc/# top 10 pharmacies in india indiapharm.llc
mexican border pharmacies shipping to usa: Mexico pharmacy online – pharmacies in mexico that ship to usa mexicopharm.com
Турецкая историческая драма – это уникальное сочетание реальных исторических событий и художественной выразительности. На странице исторические турецкие сериалы на TurkFan.tv представлены сериалы, которые переносят зрителей в различные периоды истории Турции. От великих османских султанов до событий более поздних времен, эти сериалы предлагают богатую палитру исторических персонажей и событий. Отличительной чертой турецких исторических сериалов является внимание к деталям в создании исторически достоверной атмосферы, а также глубокое исследование мотиваций и характеров главных героев.
medicine in mexico pharmacies: Medicines Mexico – buying from online mexican pharmacy mexicopharm.com
https://indiapharm.llc/# indianpharmacy com indiapharm.llc
online canadian pharmacy reviews Canada Drugs Direct safe canadian pharmacies canadapharm.life
Откройте для себя мир, полный страсти и драматизма, с турецкими сериалами онлайн на русском языке на TurkFan.tv. Эти сериалы не просто развлекают, они затрагивают самые глубокие струны души, представляя истории о любви, предательстве, дружбе и борьбе. С каждым эпизодом вы погружаетесь в увлекательные повороты сюжета, которые держат вас в напряжении от начала до конца. TurkFan.tv предлагает обширный каталог сериалов на русском языке, доступных для просмотра в любое время, что делает этот сайт идеальным ресурсом для поклонников турецкой драматургии.
mexican pharmaceuticals online: Purple Pharmacy online ordering – pharmacies in mexico that ship to usa mexicopharm.com
Если вы фанат турецких сериалов и всегда в поиске чего-то новенького, то вам стоит обратить внимание на страницу турецкие сериалы 2023 на русском языке на TurkFan.tv. Здесь собраны лучшие новинки уходящего года, которые уже успели завоевать сердца миллионов зрителей. От увлекательных исторических драм до сердцеедущих мелодрам – каждый найдет что-то по вкусу. Причем все сериалы доступны на русском языке, что делает просмотр еще более комфортным и приятным.
best price zithromax 250mg
Знаете, какое удовольствие – найти тот самый сериал, который захватывает с первых минут? На сайте, где можно смотреть лучшие дорамы онлайн, каждая история – это шедевр, отобранный с особым вниманием к качеству и сюжету. Проведите время в компании увлекательных историй, которые уже завоевали сердца зрителей по всему миру. Это место, где вы можете найти не просто дораму, а ту самую, которая станет вашей любимой.
pharmacy website india: Medicines from India to USA online – online pharmacy india indiapharm.llc
my canadian pharmacy reviews: Canadian pharmacy best prices – buying drugs from canada canadapharm.life
https://mexicopharm.com/# mexico pharmacies prescription drugs mexicopharm.com
Моя маленькая фирма столкнулась с нехваткой средств для расширения бизнеса. На портале с МФО 2024 года, который мне посоветовали, были собраны все новые МФО без отказа. Я получил долгосрочный займ на полгода с выгодными условиями по процентам и смог успешно расширить свой бизнес.
Займы на карту онлайн от лучших МФО 2024 года – для получения займа до 30000 рублей на карту без отказа, от вас требуется только паспорт и именная банковская карта!
Когда я столкнулся с неотложной финансовой потребностью, мне срочно понадобился займ. Не зная, с чего начать, я обратился к поиску в интернете. Счастью не было предела, когда я наткнулся на сайт, где собраны все МФО в одном месте. Это было настоящим спасением! Я легко и быстро нашел подходящее предложение с процентной ставкой 0% на 30 дней.
Займы на карту онлайн от лучших МФО 2024 года – для получения займа до 30000 рублей на карту без отказа, от вас требуется только паспорт и именная банковская карта!
Моя машина сломалась, и без нее я не мог добираться на работу. Страховая компания не покрыла все расходы. Я нашел портал с МФО 2024 года и получил микрозайм, чтобы починить авто и вернуться к нормальной жизни.
Займы на карту онлайн от лучших МФО 2024 года – для получения займа до 30000 рублей на карту без отказа, от вас требуется только паспорт и именная банковская карта!
mexican mail order pharmacies: Medicines Mexico – pharmacies in mexico that ship to usa mexicopharm.com
mexican border pharmacies shipping to usa: mexican rx online – buying prescription drugs in mexico mexicopharm.com
Для тех, кто ценит качественные телесериалы и хочет окунуться в мир турецкой культуры, турецкие сериалы на русском являются идеальным выбором. Переведенные на русский язык, они позволяют зрителям из России и других русскоязычных стран полностью погрузиться в сюжет, не отвлекаясь на перевод. Это открывает доступ к широкому ассортименту жанров – от романтических драм до захватывающих боевиков. На TurkFan.tv каждый найдет сериал по своему вкусу, будь то историческая эпопея или современная любовная история.
https://indiapharm.llc/# indianpharmacy com indiapharm.llc
https://canadapharm.life/# canadian pharmacy mall canadapharm.life
world pharmacy india: Online India pharmacy – cheapest online pharmacy india indiapharm.llc
Мир азиатских сериалов богат и многообразен, и каждый год он радует нас новыми шедеврами. На сайте, где можно новые дорамы онлайн смотреть, собраны самые свежие и увлекательные истории. Это ваш шанс погрузиться в новые миры, полные страсти, интриг и драмы, где каждый поворот сюжета – это новая эмоция, каждый персонаж – открытие. Наслаждайтесь каждым моментом, ведь именно здесь начинается ваше новое кинематографическое путешествие.
Для тех, кто предпочитает наслаждаться дорамами в онлайн-режиме, идеальным решением станет сайт дорамы онлайн. Это место, где собраны сериалы на любой вкус и интерес. Удобный интерфейс позволяет легко находить новинки и популярные дорамы, а также предоставляет возможность выбора по жанру или году выпуска. Кроме того, сайт постоянно обновляется, что гарантирует доступ к последним выпускам любимых сериалов.
Если вы в поисках истинных кинематографических жемчужин, то на сайте смотреть дорамы лучшие – это ваш выбор. Здесь собраны сериалы, способные увлечь, заставить смеяться или плакать, сериалы, которые оставляют след в душе. Погрузитесь в мир, где каждая дорама – это не просто история, а целая вселенная, полная глубоких чувств и незабываемых персонажей. Позвольте себе отдаться этому волшебству полностью.
canadian drug pharmacy Canada Drugs Direct canadian valley pharmacy canadapharm.life
https://canadapharm.life/# canada online pharmacy canadapharm.life
indian pharmacy: reputable indian pharmacies – top 10 pharmacies in india indiapharm.llc
Online medicine order: India pharmacy of the world – Online medicine order indiapharm.llc
https://edpillsdelivery.pro/# best erectile dysfunction pills
Мобильные телефоны в нашем магазине – оптимальный выбор для каждого
магазин – купить онлайн в Минске.
cheapest ed pills online: cheapest ed pills – pills for erection
http://tadalafildelivery.pro/# tadalafil online without prescription
http://sildenafildelivery.pro/# sildenafil 100 mg tablet cost
Мир азиатских сериалов богат и многообразен, и каждый год он радует нас новыми шедеврами. На сайте, где можно новые дорамы онлайн смотреть, собраны самые свежие и увлекательные истории. Это ваш шанс погрузиться в новые миры, полные страсти, интриг и драмы, где каждый поворот сюжета – это новая эмоция, каждый персонаж – открытие. Наслаждайтесь каждым моментом, ведь именно здесь начинается ваше новое кинематографическое путешествие.
generic sildenafil 100mg tablet: sildenafil 100mg free shipping – chewable sildenafil
cures for ed ed pills delivery ed pills that work
http://edpillsdelivery.pro/# best otc ed pills
Kamagra Oral Jelly: cheap kamagra – buy kamagra online usa
tadalafil online without prescription: online pharmacy tadalafil 20mg – generic cialis tadalafil
http://tadalafildelivery.pro/# tadalafil 20mg no prescription
https://levitradelivery.pro/# Generic Levitra 20mg
Cheap Levitra online: Levitra online – п»їLevitra price
https://levitradelivery.pro/# Buy generic Levitra online
tadalafil 40 mg online india: cheap tadalafil canada – tadalafil best price
Kamagra tablets buy kamagra п»їkamagra
http://tadalafildelivery.pro/# tadalafil 5mg uk
Thank you for some other informative website. Where else may I get that kind of information written in such a perfect manner? I’ve a mission that I am just now operating on, and I have been on the glance out for such info.
Kamagra Oral Jelly: kamagra oral jelly – buy Kamagra
Kamagra Oral Jelly: cheap kamagra – super kamagra
Once I initially commented I clicked the -Notify me when new comments are added- checkbox and now each time a comment is added I get four emails with the identical comment. Is there any method you possibly can take away me from that service? Thanks!
п»їkamagra: cheap kamagra – Kamagra 100mg price
http://tadalafildelivery.pro/# cheap tadalafil 20mg
Wonderful post however I was wanting to know if you could write a litte more on this subject? I’d be very grateful if you could elaborate a little bit further. Kudos!
http://tadalafildelivery.pro/# tadalafil cheap
I carry on listening to the news bulletin talk about receiving boundless online grant applications so I have been looking around for the top site to get one. Could you tell me please, where could i acquire some?
Освежить мягкую мебель в доме: Обновить новый вид старой мебели: секреты перетяжки перетягивать мебель своими руками: Нюансы ткани для перетяжки мягкой мебели: советы дизайнера
перетяжка мягкой мебели.
Перетяжка мягкой мебели – отличный способ обновить интерьер
where to buy sildenafil canada: Sildenafil price – where to buy sildenafil 100mg
https://edpillsdelivery.pro/# new ed pills
Paxlovid buy online paxlovid best price paxlovid india
wonderful points altogether, you simply gained a new reader. What would you recommend about your post that you made some days ago? Any positive?
http://paxlovid.guru/# Paxlovid over the counter
Hey there! This is my first visit to your blog! We are a team of volunteers and starting a new project in a community in the same niche. Your blog provided us valuable information to work on. You have done a extraordinary job!
Regards for all your efforts that you have put in this. very interesting information.
http://paxlovid.guru/# Paxlovid over the counter
Отремонтировать мягкую мебель в доме: полезные советы новый вид старой мебели: Чем перетягивать мебель своими руками: полезные советы ткани для перетяжки мягкой мебели: Как сэкономить на перетяжке мягкой мебели: 5 простых способов
перетяжка мебели в Минске.
Перетяжка мягкой мебели для создания комфортного интерьера
Отремонтировать мягкую мебель в доме: Дать новый вид старой мебели: Чем перетягивать мебель своими руками: подробное руководство ткани для перетяжки мягкой мебели: Как сэкономить на перетяжке мягкой мебели: советы экономистов
обивка мебели.
Преобразуйте свой дом с помощью перетяжки мягкой мебели
paxlovid cost without insurance: buy paxlovid online – paxlovid pill
I like this post, enjoyed this one thank you for posting. “I never let schooling interfere with my education.” by Mark Twain.
Is the author still active on the blog? I miss reading about this subject here!
https://prednisone.auction/# prednisone 20 mg in india
http://amoxil.guru/# amoxicillin generic
paxlovid price Buy Paxlovid privately buy paxlovid online
https://clomid.auction/# cost generic clomid pill
Освежить мягкую мебель в доме: топ-5 способов новый вид старой мебели: эффектные идеи перетягивать мебель своими руками: Нюансы ткани для перетяжки мягкой мебели: Как сэкономить на перетяжке мягкой мебели: 5 простых способов
обивка мебели.
Новый облик старой мебели: зачем нужна перетяжка мягкой мебели
Для тех, кто в поиске новейших серий аниме, у меня есть отличная рекомендация. Проверьте новые аниме онлайн на animeline.tv. Этот сайт предлагает широкий выбор аниме, и все это доступно без каких-либо платежей или необходимости регистрации. Также стоит отметить, что сайт занимает лидирующие позиции в Яндексе, что говорит о его надежности и популярности.
http://stromectol.guru/# stromectol 15 mg
Моей сестре срочно понадобились деньги на покупку лекарств, но из-за её плохой кредитной истории и наличия просрочек, получить займ казалось невозможным. На сайте mikro-zaim-online.ru она нашла возможность получения займа просрочкой с плохой историей, что позволило ей оперативно решить свои финансовые трудности.
Are you a connoisseur of 18+ comics? multpirn – mult34.com is your treasure trove. Our site is a gateway to worlds where your wildest fantasies meet the finest artistry. Every genre, every style, every pulse-racing plot is here, waiting to be explored. We’ve gathered the creme de la creme of adult comics to satisfy your discerning taste. Join us in celebrating the diversity and brilliance of adult comic genres.
where to get clomid without rx: cheapest clomid – how can i get generic clomid without insurance
synthroid 025 mg
Демо игровых слотов предлагают уникальную возможность насладиться азартом и развлечениями казино, не тратя при этом своих финансовых средств. Это идеальный способ попробовать себя, узнать новые игры и разработать стратегии без каких-либо обязательств.
Благодаря огромному количеству игровых автоматов с демо игрой, каждый игрок найдет что-то по своему вкусу. От классических трехбарабанных слотов до современных видеослотов с захватывающей графикой и увлекательными бонусными раундами.
Играть в игровые автоматы новинки играть бесплатно легко и удобно. Вам не нужно создавать аккаунт или делать депозит – просто подберите подходящий игровой автомат и начните играть. Это отличная возможность попробовать разные стратегии ставок, изучить выигрышные комбинации и просто насладиться процессом игры.
Демо-режим также дает возможность вам оценить процент отдачи игрового автомата и понять, как он подходит вам по стилю и предпочтениям. Вы можете играть сколько угодно долго, не боясь за свои деньги.
http://prednisone.auction/# buy prednisone canada
Какое из приведенных ниже понятий относится к характеру а не темпераменту человека.
Еда черного цвета список.
Психология методы. Эзотерика цвета. Срок действия паспорта гражданина российской федерации.
Какой из перечисленных методов исследования был недоступен древним.
Тест психологический на личность.
3 позиции восприятия.
http://clomid.auction/# cost of cheap clomid tablets
https://stromectol.guru/# minocycline price
https://stromectol.guru/# ivermectin 1mg
paxlovid cost without insurance Buy Paxlovid privately paxlovid pill
Kudos on the article! It’s well-written and informative. Adding more visuals in your future pieces could make them even more enjoyable for readers.
Bravo on the article! 👍 The insights are well-expressed, and I believe incorporating more images in your next articles could be beneficial. Have you thought about that? 🖼️
Why settle for a dull evening when you can have a thrilling one with my hero academia hentai – mult34.com’s adult comics? Our portal is designed with guys in mind, offering a diverse range of stories that resonate with the modern man. From heart-racing adventures to laugh-out-loud humor, everything is crafted to make your night more colorful – and it’s completely free! Get ready to experience comics like never before, where every page is a new discovery.
Как большой любитель аниме, я всегда ищу платформы, где можно найти что-то новенькое. На аниме онлайн я нашел не только классические серии, но и эксклюзивные новинки. Animeline.tv открыл мне двери в удивительный мир аниме, где каждая серия – это новое приключение.
Why settle for a dull evening when you can have a thrilling one with elastigirl porn – mult34.com’s adult comics? Our portal is designed with guys in mind, offering a diverse range of stories that resonate with the modern man. From heart-racing adventures to laugh-out-loud humor, everything is crafted to make your night more colorful – and it’s completely free! Get ready to experience comics like never before, where every page is a new discovery.
paxlovid generic: paxlovid best price – paxlovid india
güvenilir bahsin adresi
https://prednisone.auction/# where to get prednisone
Искал я недавно в Google, где можно смотреть аниме онлайн бесплатно, и наткнулся на animeline.tv. Удивительно, но здесь я обнаружил огромный выбор аниме в отличном качестве и без назойливой рекламы. Это стало для меня настоящим открытием, ведь теперь я могу наслаждаться просмотром любимых серий без прерываний.
Близится долгожданное мероприятие, на котором я хотел выглядеть особенно стильно. Но у меня не было подходящего костюма. Я обратился к сайту msk-zaim.ru, который предоставил мне список МФО, где можно получить займ без отказа под 0%. Благодаря этому сайту, я смог быстро оформить займ и купить стильный костюм, который помог мне выделиться на мероприятии и оставить незабываемое впечатление.
Мгновенное одобрение – не ждите получите деньги сейчас
На днях моя младшая сестра попросила найти ей что-то интересное для просмотра. Я зашел на смотреть аниме онлайн в хорошем качестве и обнаружил animeline.tv. Вместе мы выбрали несколько серий, и были приятно удивлены качеством картинки. Это превратило наш семейный вечер в настоящее приключение!
Всегда мечтал о месте, где можно было бы смотреть аниме без ограничений. Моя мечта осуществилась, когда я нашел в Яндексе аниме онлайн бесплатно. Animeline.tv открыл для меня новый мир, где каждая серия – это путешествие в неизведанные уголки фантазии.
http://stromectol.guru/# ivermectin price
https://clomid.auction/# where to get clomid now
wellbutrin effexor
💫 Wow, blog ini seperti petualangan fantastis meluncur ke alam semesta dari kemungkinan tak terbatas! 💫 Konten yang mengagumkan di sini adalah perjalanan rollercoaster yang mendebarkan bagi pikiran, memicu ketertarikan setiap saat. 🌟 Baik itu inspirasi, blog ini adalah sumber wawasan yang mendebarkan! 🌟 Berangkat ke dalam perjalanan kosmik ini dari pengetahuan dan biarkan imajinasi Anda berkelana! ✨ Jangan hanya mengeksplorasi, alami sensasi ini! #BahanBakarPikiran Pikiran Anda akan bersyukur untuk perjalanan mendebarkan ini melalui alam keajaiban yang menakjubkan! ✨
Stimulating read, a recommended gem!
cytotec pills buy online: Misoprostol best price in pharmacy – Abortion pills online
Artikel ini fantastis! Cara klarifikasinya sungguh memikat dan sangat gampang untuk dipahami. Sudah nyata bahwa telah banyak kerja keras dan studi yang dilakukan, yang sungguh layak diapresiasi. Penulis berhasil membuat subjek ini tidak hanya menarik tetapi juga menyenangkan untuk dibaca. Saya dengan suka cita menantikan untuk melihat lebih banyak konten seperti ini di masa depan. Terima kasih atas berbaginya, Anda melakukan karya yang luar biasa!
https://misoprostol.shop/# buy cytotec in usa
canadian lisinopril 10 mg cheapest lisinopril lisinopril 125 mg
http://azithromycin.store/# zithromax
buy zithromax online fast shipping: buy zithromax over the counter – buy zithromax
Мой дом требовал неотложного ремонта, и я хотела улучшить свое жилье. Но финансы были ограничены. С помощью Яндекса, я нашла сайт msk-zaim.ru, где была информация о МФО 2024 года. Здесь я взяла микрокредит на 10 000 рублей под 0%, что помогло мне начать ремонт и сделать свой дом более комфортным и уютным.
Срочные деньги – микрозаймы для ваших немедленных потребностей
http://finasteride.men/# buy propecia tablets
Have you ever thought about writing an ebook or guest authoring on other
blogs? I have a blog centered on the same topics you discuss and would love to
have you share some stories/information. I know my viewers would value your work.
If you’re even remotely interested, feel free to send me an e-mail.
Look at my website … “https://x.com/rayanwebb/status/1740571631867830311?s=20
zithromax generic cost: buy zithromax over the counter – buy zithromax online australia
lisinopril uk: cheapest lisinopril – lisinopril 2.5 mg
http://misoprostol.shop/# buy cytotec over the counter
3 clonidine
http://azithromycin.store/# zithromax 250 mg australia
lasix medication Buy Furosemide lasix
http://azithromycin.store/# buy zithromax 1000mg online
combivent inhaler generic
cytotec pills buy online: Misoprostol 200 mg buy online – cytotec buy online usa
generic zithromax 500mg: Azithromycin 250 buy online – zithromax coupon
https://misoprostol.shop/# Misoprostol 200 mg buy online
Новое покрытие для вашей мебели: перетяжка
перетяжка мягкой мебели https://peretyazhka-mebeli-v-minske.ru/.
dark web marketplaces tor market links darknet marketplace
darknet market lists darknet links darknet market
dark market deep web drug links deep web drug store
darkmarket 2024 dark web market dark web access
drug markets onion https://darkweb-storelist.com/ – deep dark web darknet markets links
deep web sites deep web links dark web site
darknet market links dark market list darknet markets 2024
tor marketplace dark web market dark website
deep web drug markets darknet drugs how to access dark web
darknet drug market darkmarket dark web websites
onion market free dark web dark market link
cryptomarkets darknet deep web links dark market url
dark web sites darknet markets url tor dark web
darknet sites dark market list onion dark website
dark markets darkweb marketplace dark web market links
dark market tor darknet darknet sites
tor drug market dark web access tor marketplace
darknet markets darknet seiten darknet links
black internet darknet drug links darknet markets onion address
darkmarket 2024 dark web markets darkmarket list
darknet drug store https://alldarknetmarkets.com/ – dark web links deep web search
darkmarket link tor darknet darknet market list
darknet markets 2024 bitcoin dark web dark web markets
the dark internet drug markets dark web dark market list
dark market link dark market the dark internet
deep web drug markets darknet drug market darknet market lists
zithromax tablets for sale: cheapest azithromycin – where can you buy zithromax
drug markets dark web dark web link tor dark web
tor market url blackweb black internet
how to get on dark web darknet drug store dark net
how to access dark web drug markets onion tor marketplace
dark web links darkmarket url drug markets onion
darknet markets 2024 darknet links darkmarket 2024
deep web links deep web search deep web drug links
tor market url how to get on dark web dark market url
dark market onion dark web links deep web drug markets
darknet search engine dark web market list darknet drug links
darknet markets dark web sites links dark website
tor dark web black internet darknet markets links
tor dark web deep web drug store how to get on dark web
purchase cytotec: buy misoprostol – cytotec buy online usa
deep web drug links https://alldarknetmarkets.com/ – deep web markets bitcoin dark web
darknet drug store dark net tor drug market
deep web drug links darknet magazine dark web access
darknet links dark markets 2024 darkweb marketplace
dark web market urls darknet markets onion address drug markets onion
how to access dark web dark web sites tor dark web
dark web marketplaces dark web market urls darknet magazine
dark web market darknet markets dark web link
darknet markets url deep dark web darknet seiten
dark web sites dark net cryptomarkets darknet
darknet seiten dark market drug markets dark web
how to get on dark web dark web search engine onion dark website
dark markets dark web marketplaces darkmarket
darkmarket url dark web drug marketplace darknet markets onion address
tor market blackweb official website dark web access
dark web market links darknet site deep web markets
free dark web dark web drug marketplace tor marketplace
deep web drug markets tor market url dark websites
darkmarkets darknet market tor markets
blackweb dark web search engines tor marketplace
darknet markets onion tor market the dark internet
https://azithromycin.store/# generic zithromax medicine
blackweb official website darknet market list dark web sites links
how to get on dark web tor market links dark market
dark market darknet drug links deep web markets
darkmarket link https://darknet-marketspro.com/ – deep dark web dark web links
buy cytotec in usa buy misoprostol buy cytotec pills
tor market deep web drug store dark web marketplaces
darkmarket dark markets dark markets 2024
tor darknet tor market links dark web market urls
https://misoprostol.shop/# buy cytotec over the counter
tor market links drug markets onion black internet
dark web site tor market darkmarket list
tor markets 2024 deep web drug store darknet drug links
dark websites darknet drug market darknet drug links
darknet market lists dark market list onion dark website
dark websites darknet drugs drug markets onion
darknet drugs darknet marketplace darknet drugs
tor markets black internet tor markets
dark market list dark market deep web sites
drug markets onion deep web sites tor markets
darknet sites the dark internet dark websites
tor markets 2024 darknet marketplace dark web sites
darknet seiten dark market 2024 dark web link
Недавно у меня возникли неотложные медицинские расходы, которые требовали серьезных финансовых вложений. Обратившись к сайту msk-zaim.ru, я нашел список МФО, предоставляющих займы без лишних сложностей. Благодаря этому займу, я смог покрыть медицинские расходы и обеспечить свое здоровье. Этот сайт стал настоящим спасением в трудный момент.
Займы на карту – на приобретение красивой одежды
darkmarket list tor darknet dark internet
dark net drug markets onion dark web links
darknet marketplace darknet websites darknet markets onion address
darknet market links deep web drug markets dark web search engine
darkmarket link https://alldarkwebmarkets.com/ – blackweb official website dark web site
tor drug market how to access dark web darknet seiten
deep dark web dark web markets dark web market
darknet drugs dark web markets best darknet markets
dark market link drug markets dark web darknet marketplace
darknet drug store dark web markets darkmarket 2024
darknet drugs dark websites darkmarket
dark market url darknet websites darknet magazine
darknet search engine how to access dark web deep web drug markets
darknet drug links dark website darkmarket link
dark market onion dark market url darknet market list
dark market onion darknet seiten darkmarkets
dark web market links tor market dark internet
deep dark web dark web sites darknet links
darkmarkets dark market link dark web marketplaces
blackweb official website darknet markets onion address blackweb
darknet sites darkmarket 2024 darknet site
darkmarket url darkweb marketplace darknet site
dark web marketplaces darknet market list dark web access
dark web link dark web market cryptomarkets darknet
black internet tor markets links tor marketplace
cryptomarkets darknet darkmarket list dark web markets
darknet links deep web drug links darknet seiten
dark internet dark market link darknet seiten
tor markets links darkmarket url dark markets 2024
darknet markets onion address tor markets 2024 tor darknet
dark web search engines dark market best darknet markets
dark websites dark market tor market url
deep web links tor market url deep web drug links
“Сверхъестественное” представляет собой увлекательный рассказ о приключениях
братьев Винчестеров, путешествующих по миру в поисках паранормальных явлений и борющихся
с нечистой силой. Они сталкиваются с самыми разными
сущностями – от зловещих демонов и блуждающих духов
до небесных ангелов и забытых божеств.
Каждая серия этого сериала – это отдельная история, наполненная удивительными событиями и богатая своей уникальной мифологией.
Просмотр “Сверхъестественного” в режиме онлайн позволяет зрителям погрузиться в захватывающий мир, в котором реальность переплетается с фантастикой.
Этот популярный сериал обязательно поразит вас своей драматичностью,
остроумием и запоминающимися героями.
Feel free to visit my website :: “https://imoodle.win/wiki/Sverhi.net
dark market url dark market 2024 darknet markets
how to access dark web darkmarkets the dark internet
deep web links cryptomarkets darknet darkmarket 2024
best darknet markets dark markets darknet market lists
darknet drugs darknet market list darknet marketplace
darknet markets links tor market url darknet markets onion
dark market 2024 darknet drug market blackweb official website
darknet markets 2024 darknet site blackweb official website
deep web links drug markets dark web deep web markets
dark web site https://darkweb-storelist.com/ – dark web market darknet drug market
bitcoin dark web dark web link dark web market urls
tor darknet drug markets onion blackweb official website
dark website dark market darknet market links
darkmarkets deep web links darkmarket 2024
darknet drug store darknet websites dark internet
darknet market lists bitcoin dark web dark web link
furosemida: Buy Furosemide – lasix 100mg
darknet markets 2024 darknet search engine darkweb marketplace
darknet market darkmarket url deep web drug markets
tor markets links darknet markets onion darknet marketplace
dark web market list darknet links onion market
dark market list drug markets onion dark web search engines
darknet search engine dark markets the dark internet
dark web sites darknet markets 2024 darknet markets
darkmarket tor markets links darknet markets 2024
darkmarkets dark web websites dark net
darknet site darkmarket 2024 darkmarket url
dark website dark web site dark web link
deep dark web https://alldarkwebmarkets.com/ – tor market dark market link
darknet markets links deep web drug url dark web market links
darknet links dark web markets darknet market
darknet markets best darknet markets tor darknet
darknet seiten darkmarket 2024 darkmarket 2024
darknet site darknet drug store dark web site
darknet markets url darknet market list dark market url
dark web marketplaces deep dark web deep web search
dark websites dark websites tor markets links
how to get on dark web tor market url darknet drug store
tor markets links dark market dark web access
Недавно у меня возникли неотложные медицинские расходы, которые требовали серьезных финансовых вложений. Обратившись к сайту msk-zaim.ru, я нашел список МФО, предоставляющих займы без лишних сложностей. Благодаря этому займу, я смог покрыть медицинские расходы и обеспечить свое здоровье. Этот сайт стал настоящим спасением в трудный момент.
Срочный займ – быстрый выход из финансовых трудностей
how to get on dark web dark web market urls deep web markets
Моя подруга всегда мечтала о романтическом вечере на природе. Но мои финансы были на исходе, и зарплата только через 10 дней. Я решила не откладывать на потом, пошла на портал msk-zaim.ru и взяла онлайн займ под низким процентом. Благодаря этим средствам, я устроила для нее увлекательный романтический вечер на закате, который она запомнит на долго.
Срочные деньги – микрозаймы для ваших немедленных потребностей
tor markets 2024 dark web sites tor market links
darknet markets 2024 darknet markets onion dark web websites
dark web sites links dark market link darknet search engine
blackweb official website darknet seiten darknet drug links
deep web drug links darkmarket dark website
tor markets links darknet drug market deep web drug store
tor dark web https://alldarknetmarkets.com/ – dark markets onion dark website
darknet market list https://alldarkwebmarkets.com/ – darknet market links dark internet
how to get on dark web tor marketplace dark web marketplaces
dark web search engines dark web link darknet markets links
darknet markets 2024 deep web markets deep web drug store
free dark web dark market darknet marketplace
dark net drug markets onion darknet market list
darknet magazine onion dark website dark net
dark market darknet drugs the dark internet
deep web sites deep web drug markets darknet market
darknet markets links free dark web darkweb marketplace
dark web market links tor drug market dark market onion
dark market 2024 darknet markets darkmarket url
how to get on dark web deep web drug store blackweb official website
tor markets 2024 how to access dark web tor dark web
http://finasteride.men/# get propecia without rx
dark market tor market tor markets 2024
Мягкая мебель для вашего дома
перетяжка мебели https://murom-mebel-tula.ru/.
deep web drug markets dark market url dark web search engines
darkmarkets dark web drug marketplace dark market 2024
tor markets links dark web market links darkmarket url
dark market link darknet sites deep web search
dark internet https://darknet-marketspro.com/ – blackweb darkmarket
dark web market drug markets dark web darknet markets
tor darknet dark web market list tor marketplace
deep dark web darkmarket 2024 tor marketplace
darkweb marketplace tor market links dark web market links
tor marketplace darknet magazine blackweb official website
darknet site https://alldarkwebmarkets.com/ – dark markets drug markets dark web
darkweb marketplace tor dark web darknet market lists
drug markets onion deep web drug markets darknet drug store
dark web access dark web link dark market onion
bitcoin dark web darknet seiten dark web websites
tor market url darknet markets onion address tor markets 2024
darknet markets onion address blackweb deep web drug markets
darkmarket url tor markets 2024 deep dark web
dark market dark web sites links dark web market urls
dark web websites darknet market list deep dark web
darknet markets onion address dark web market dark web sites
deep web links dark web drug marketplace dark market
darkmarket url tor markets dark web drug marketplace
dark web sites links free dark web darkmarket link
darkmarket 2024 how to access dark web darknet search engine
dark web market links https://alldarknetmarkets.com/ – darknet market darknet market list
dark web market links dark web sites how to access dark web
darknet markets 2024 darknet markets 2024 best darknet markets
darknet markets onion address darknet search engine darknet markets links
darknet market lists https://darkweb-storelist.com/ – tor markets links blackweb official website
darknet drug market darknet drug market dark internet
darknet site darknet links tor darknet
dark web links dark market onion dark website
dark web sites deep web drug url darknet markets onion address
darknet drug store dark web sites tor darknet
deep dark web dark websites dark web sites
http://azithromycin.store/# zithromax over the counter uk
dark web site darknet drugs darknet drug store
free dark web tor darknet dark web site
darknet markets onion onion dark website deep web drug store
dark web markets tor drug market dark market link
tor market deep web markets deep web drug links
dark website dark market dark market
how to access dark web tor markets links dark web websites
tor marketplace darkmarket list tor markets
darkmarkets https://alldarknetmarkets.com/ – darkmarket link dark web site
darknet site dark market list darknet markets 2024
darknet links darknet markets links tor market
darkmarket 2024 dark web websites dark net
darknet market https://darkweb-storelist.com/ – dark web search engine dark web websites
dark website tor market url deep web links
Однажды, когда все банки уже закрылись, и мне срочно понадобились деньги, я обратил внимание на сайт msk-zaim.ru, который оказался в ТОПе Yandex. Там был список актуальных МФО, и я отправил заявку. Удивительно, но всего через 10 минут деньги были переведены на мою карту! Этот сайт настоящий спаситель в поздний вечер.
Займы срочно – возьмите займ на покупку ноутбука
cytotec pills buy online: Buy Abortion Pills Online – buy cytotec online fast delivery
darknet market list darkmarket url dark web markets
dark web site dark web access darkmarket list
darknet marketplace darknet drug market tor market url
Индивидуальный подход к перетяжке мебели: ваш выбор
ремонт мягкой мебели перетяжка диванов.
deep web markets best darknet markets dark net
how to access dark web darknet drug links dark market 2024
free dark web cryptomarkets darknet deep web drug url
darknet market links dark web market list drug markets onion
darknet sites darkmarket 2024 deep web drug markets
darknet markets url dark web sites darknet market list
dark internet dark web search engines darknet markets 2024
darknet markets 2024 darknet markets url tor markets links
darknet market list blackweb official website deep web drug links
deep dark web darknet markets links dark web search engine
dark market 2024 darknet drug links dark website
deep web drug url dark market url dark web market list
deep web drug links darknet drug market darknet market list
dark internet darknet market links darknet magazine
deep web markets onion market dark net
darknet drug market bitcoin dark web tor drug market
darknet magazine darkmarket url dark internet
cryptomarkets darknet dark web sites deep web drug links
darknet market dark markets dark websites
dark market link bitcoin dark web darkweb marketplace
dark web sites darknet seiten tor drug market
dark internet free dark web darknet magazine
deep web drug store dark web market urls darknet seiten
darknet drug market drug markets onion deep dark web
blackweb official website https://alldarknetmarkets.com/ – darknet markets onion deep web search
deep web search dark web search engines darknet sites
darknet markets links dark websites dark web access
drug markets onion https://darkweb-storelist.com/ – deep web markets dark web marketplaces
darknet sites dark web site drug markets onion
deep web sites dark web sites links dark markets
dark web market links darknet site dark markets
darknet links free dark web dark net
dark web sites dark websites dark web market urls
blackweb official website dark web market urls dark market 2024
darknet site darknet drugs deep web markets
free dark web blackweb tor market url
dark markets 2024 dark web market darknet market list
deep web markets tor darknet dark net
dark website deep web search darknet markets
black internet https://darknet-marketspro.com/ – darknet market dark market list
dark market list dark web market urls blackweb
dark markets 2024 darknet search engine dark web sites
deep web drug url darknet magazine dark markets
darknet markets links blackweb official website deep web search
onion market darknet magazine dark web link
dark internet deep web markets dark web market
darknet market lists dark web search engines darknet sites
darknet drug links darkmarkets darknet drug market
dark market onion dark markets 2024 dark web markets
deep dark web darknet market links dark market list
darknet sites dark market dark market onion
deep web sites darknet search engine dark web market list
dark market link darknet search engine dark market link
dark web websites deep web drug markets bitcoin dark web
how to access dark web dark market list free dark web
darkmarkets how to access dark web darknet marketplace
black internet best darknet markets dark web market
darknet drug market deep web drug store dark website
dark web access dark web link tor market links
deep web drug url dark web market links tor markets links
dark market onion dark markets deep web markets
free dark web tor dark web darknet market lists
onion market black internet dark web market list
cryptomarkets darknet dark web markets deep web drug markets
dark web link darknet magazine darknet markets
darknet market links dark net dark web search engines
dark market tor market links dark market 2024
tor darknet darknet seiten darknet market lists
darknet sites darknet magazine dark websites
darknet drug links deep web drug store dark market onion
tor markets 2024 dark web sites links blackweb
dark market list tor darknet onion dark website
dark web market cryptomarkets darknet deep web drug markets
the dark internet dark net dark web market urls
tor market url tor dark web darknet market list
darknet seiten darknet markets links darkweb marketplace
dark web market list https://darkweb-storelist.com/ – deep web drug url deep web links
cryptomarkets darknet dark web market links dark website
dark website cryptomarkets darknet darknet site
best darknet markets dark market onion onion dark website
buying cheap propecia Finasteride buy online get generic propecia online
deep web drug store dark web marketplaces darknet market list
drug markets onion dark website darknet market lists
dark markets 2024 tor markets free dark web
drug markets onion darknet magazine darknet magazine
lisinopril 20mg tablets cost: over the counter lisinopril – lisinopril 5 mg for sale
darknet search engine tor markets links how to access dark web
bitcoin dark web darkmarket link deep web drug markets
deep web links darknet drug store darknet sites
dark web market links darknet markets url darknet markets links
darkweb marketplace dark web market darkmarket 2024
dark web market dark market 2024 darknet drug market
dark markets https://alldarknetmarkets.com/ – dark web search engine onion market
darknet markets onion address dark web links darkmarket url
drug markets dark web onion market darknet sites
darknet websites darknet markets onion address tor market links
dark web market links dark web market list dark web access
http://azithromycin.store/# zithromax generic cost
darknet markets 2024 dark website tor markets
how to get on dark web dark web market list tor markets 2024
darkmarket dark market darknet magazine
darknet magazine darknet drugs dark web link
dark web search engine darknet markets links tor drug market
buy cytotec pills online cheap: cheap cytotec – buy cytotec over the counter
darkmarket url darknet websites darknet drug links
deep dark web drug markets onion deep web markets
dark web drug marketplace darknet markets links dark websites
tor markets links how to get on dark web dark market link
dark web links darkmarket drug markets onion
tor markets darkmarket url dark web marketplaces
how to get on dark web deep web drug markets darkweb marketplace
dark market darknet market darknet markets links
deep web markets dark web sites tor markets 2024
darknet drug store dark web links dark website
how to access dark web darknet websites drug markets onion
dark internet darknet market lists drug markets dark web
darknet drugs drug markets onion darkmarkets
deep web sites dark market darknet seiten
drug markets dark web deep web markets darknet site
darknet marketplace the dark internet deep web search
dark market url darknet sites how to get on dark web
tor marketplace dark web search engine dark web marketplaces
onion dark website darknet magazine deep web drug markets
darknet markets onion address dark markets 2024 onion market
tor drug market dark internet darknet market list
drug markets dark web best darknet markets tor markets
dark markets 2024 dark market url dark web market links
dark markets 2024 dark web market urls onion dark website
best darknet markets tor markets links dark web search engines
darknet drug store tor markets 2024 darknet marketplace
tor markets deep web markets darknet drugs
dark market url how to access dark web dark web marketplaces
dark web link dark web market links darkmarkets
darknet links deep dark web darknet site
dark market 2024 best darknet markets best darknet markets
darknet markets onion address how to get on dark web darknet market lists
dark market onion deep web drug markets darknet websites
dark internet dark web search engines dark web market
tor market url darkmarket link darknet seiten
darknet marketplace dark market onion dark website
cryptomarkets darknet deep web search dark web search engine
https://azithromycin.store/# buy zithromax online australia
the dark internet onion dark website dark market 2024
drug markets dark web tor dark web darknet links
dark web sites links onion market dark web search engines
black internet how to get on dark web darkmarket list
tor markets darknet drug market darknet markets onion
blackweb official website how to access dark web darknet drug market
dark web market urls onion dark website blackweb
darknet drug links darknet magazine blackweb
dark market link the dark internet dark web market links
dark market url dark markets dark market 2024
tor dark web blackweb official website dark web access
deep web search deep web drug url darknet drug market
darknet links darknet markets 2024 darknet markets onion
drug markets onion dark web marketplaces darkmarket 2024
darkweb marketplace free dark web dark markets 2024
darknet websites deep web drug store dark web site
darknet market deep web drug url deep web drug markets
dark web market links tor market links darkmarket url
dark net darknet sites dark net
how to access dark web best darknet markets darknet markets 2024
tor drug market dark web links dark market url
darknet market links the dark internet best darknet markets
dark web search engine darkmarket link the dark internet
tor markets dark web market darknet markets links
the dark internet tor market links tor marketplace
tor market url darknet markets tor market url
darknet site tor markets 2024 tor marketplace
dark market list deep web links darkmarket url
get cheap propecia without dr prescription: cost of cheap propecia tablets – buying propecia without insurance
tor market url dark web access tor darknet
darknet markets 2024 onion dark website darknet drug store
darknet market lists dark markets dark web link
tor market links darknet drugs dark websites
deep web drug markets darknet market dark website
how to access dark web onion market dark web links
blackweb official website darknet market list darknet markets onion address
dark website darknet market links drug markets dark web
darknet markets onion address tor market links tor markets
darknet seiten darknet links drug markets onion
tor marketplace tor market links darknet magazine
darknet search engine deep web search bitcoin dark web
dark web search engines tor dark web tor market links
darknet seiten dark markets 2024 drug markets onion
dark markets 2024 deep dark web dark web market
how to access dark web darknet markets onion address darknet drug links
dark web search engine tor marketplace deep web drug store
darknet market lists dark web market links the dark internet
deep web markets dark web drug marketplace tor markets
dark web site dark web sites links deep web drug markets
drug markets dark web darknet markets 2024 dark website
dark market 2024 tor market links blackweb
What i do not realize is in fact how you’re now not actually much more smartly-preferred than you may be right now. You’re very intelligent. You realize thus significantly on the subject of this subject, produced me for my part consider it from so many varied angles. Its like women and men don’t seem to be involved unless it is one thing to do with Girl gaga! Your personal stuffs excellent. All the time handle it up!
deep web drug url tor darknet dark web search engines
dark web links dark web drug marketplace darknet seiten
dark web access darknet site darknet markets onion address
how to access dark web free dark web darknet markets onion address
darknet markets url deep dark web darknet drugs
deep web sites dark website dark web sites links
deep web links deep dark web dark websites
darknet markets deep dark web darknet magazine
https://misoprostol.shop/# cytotec abortion pill
dark internet darknet market links black internet
deep web links tor darknet onion market
darknet markets 2024 darkmarket dark market url
darknet market drug markets dark web darknet seiten
darknet market list tor markets links black internet
dark market list onion dark website dark market list
tor markets darknet drug links dark web market
how to get on dark web darkmarket dark web market urls
tor marketplace dark markets 2024 dark web market urls
darkmarket list darkmarket list dark websites
dark market 2024 dark web search engines dark web websites
Дисконтная система для постоянных клиентов
ремонт холодильников ремонт холодильника.
darknet drug store onion dark website tor drug market
dark websites darknet drug market dark net
darknet markets links dark web market list dark web market
darknet markets url https://darkweb-storelist.com/ – dark web sites darknet markets links
tor darknet best darknet markets dark web access
dark markets dark market onion darknet market list
how to access dark web dark net darknet search engine
deep web sites dark web market list dark web market list
dark market link deep web links darknet drugs
onion dark website darkmarkets deep dark web
dark web marketplaces dark web market deep web markets
darknet market lists dark web markets dark market 2024
deep web sites darkweb marketplace dark websites
dark web marketplaces dark market darkmarket list
darknet search engine deep web search dark web links
darknet seiten bitcoin dark web onion dark website
dark web search engines dark net darknet drugs
deep web search onion dark website darknet sites
how to access dark web dark markets 2024 dark web sites links
tor markets 2024 dark web search engine dark market list
darknet markets 2024 dark markets dark market link
dark web market list dark website dark web sites links
cryptomarkets darknet tor marketplace darknet market
darknet market list darknet drug store darknet drug market
tor drug market tor market tor marketplace
darknet links dark web market how to access dark web
deep web markets tor drug market dark web markets
tor markets deep web sites darknet markets onion
dark web sites dark markets 2024 dark websites
darknet sites darkweb marketplace darkmarkets
dark websites black internet dark web site
dark market url dark websites dark net
dark market url darknet drugs darknet markets 2024
darknet websites how to access dark web free dark web
darkmarkets drug markets onion dark web market urls
dark website darkweb marketplace tor market
dark web site darkweb marketplace dark web site
dark web market darknet marketplace dark market link
dark websites free dark web dark internet
dark markets cryptomarkets darknet onion market
dark web market urls dark market link blackweb official website
darkmarket list best darknet markets dark market list
darknet marketplace darknet markets onion address darknet market list
tor market url how to access dark web darknet market list
dark markets dark web markets free dark web
darknet websites black internet darknet drug links
dark web link darkmarket link tor markets 2024
dark website dark net bitcoin dark web
zithromax for sale 500 mg: zithromax best price – buy zithromax online cheap
darknet seiten deep web drug store darknet market lists
blackweb official website dark internet tor market links
darknet market list deep web search dark web market links
darknet drug store dark web market urls darknet market links
dark markets darknet market list dark internet
dark web sites darkmarket url how to access dark web
tor markets darkmarkets tor drug market
dark web websites dark market deep web search
dark market bitcoin dark web tor markets 2024
darknet markets dark market onion darkmarkets
tor market url darknet markets url dark web marketplaces
dark market link darknet drug store dark web market urls
darknet marketplace black internet dark web link
dark markets 2024 darknet markets darknet markets onion address
darkmarket list darknet websites dark web access
dark websites free dark web dark web market urls
http://finasteride.men/# cost cheap propecia without a prescription
dark market list best darknet markets bitcoin dark web
tor dark web dark web drug marketplace darknet seiten
dark web search engines dark market best darknet markets
darknet drug links darknet markets darknet markets
onion dark website tor drug market cryptomarkets darknet
deep dark web darknet websites tor marketplace
blackweb darkweb marketplace deep web drug links
tor markets 2024 dark web marketplaces dark web market list
darkmarket url deep web markets dark market onion
darknet market darkweb marketplace tor drug market
dark web drug marketplace dark web markets blackweb
tor market links best darknet markets darknet drug store
dark web link dark market url darknet market list
darknet site dark market link onion dark website
cytotec online buy misoprostol order cytotec online
deep web drug links darknet markets onion address onion market
tor darknet darknet markets 2024 dark web search engine
cryptomarkets darknet deep web links deep web links
dark web link cryptomarkets darknet darknet drug store
dark market url darknet search engine dark web site
dark web drug marketplace dark web websites dark market
deep web sites darknet markets links dark web links
tor markets dark web sites darknet market
darkweb marketplace dark web market links tor market
dark web link deep web drug links dark website
dark net best darknet markets drug markets onion
deep web drug url darknet sites darknet seiten
darknet drug market deep web search blackweb official website
darkweb marketplace darknet drug market darkmarket list
tor markets darknet market links darknet websites
dark web drug marketplace deep web drug links darknet market
deep web drug markets dark web market darkmarket url
deep web links dark web sites links darknet search engine
tor markets 2024 darknet market list tor drug market
http://misoprostol.shop/# order cytotec online
tor markets links tor market links how to get on dark web
dark internet tor darknet deep web sites
deep web drug store dark web drug marketplace dark market
dark market list dark web link tor dark web
darkmarket list darknet drug store darknet sites
dark markets darknet seiten darknet markets 2024
darknet drugs tor marketplace tor market
dark web access darknet search engine deep web drug links
darknet markets dark web market darknet market lists
blackweb how to access dark web deep web markets
dark market link how to get on dark web dark market 2024
dark web markets darkmarket darkweb marketplace
darknet sites darknet markets 2024 how to get on dark web
darkmarket link darknet market lists cryptomarkets darknet
darknet markets url deep web markets darknet links
Я долго ждал, когда наконец-то смогу увидеть новые серии своих любимых аниме, и вот моя мечта сбылась! Наткнулся на этот сайт, где можно смотреть аниме 2024 онлайн, и это просто фантастика! Сайт занимает первое место в Яндексе, и неудивительно – здесь всё бесплатно, а качество просто на высоте. Больше не нужно тратить время на поиски – здесь есть все новинки, которые только можно пожелать. И все это доступно в несколько кликов, прямо у вас на экране в отличном качестве.
dark web websites deep web drug url tor market
darkmarket 2024 drug markets dark web tor market links
onion market darknet drug store tor darknet
darkmarket darkmarket url tor markets 2024
dark web link dark market list tor markets links
deep web links darknet site tor darknet
dark web websites how to get on dark web dark market list
tor market url darknet markets darknet drug market
tor marketplace tor markets links darknet markets url
darknet site darkweb marketplace darknet drug market
blackweb official website free dark web black internet
tor markets 2024 dark market onion onion market
deep dark web darknet markets onion address darknet market list
darkmarket 2024 https://darknet-marketspro.com/ – dark internet darknet drugs
dark web access darknet site tor darknet
deep web drug links black internet blackweb
deep web drug links dark market link blackweb
darknet markets darknet markets links darkmarket list
lisinopril 18 mg: buy lisinopril online – lisinopril tablet 40 mg
dark market list drug markets dark web tor markets
darkweb marketplace dark web websites darknet search engine
deep web links darkmarket dark website
tor markets links deep web search deep web drug store
dark markets 2024 darknet sites darknet drug links
dark web sites tor drug market darknet markets 2024
dark markets darknet magazine dark web search engine
tor markets tor markets darknet market
deep web search dark websites tor market links
tor drug market best darknet markets darknet markets onion
darknet drug store dark web marketplaces drug markets dark web
darkmarket url dark web site dark web sites links
buy cytotec in usa: buy misoprostol – Misoprostol 200 mg buy online
dark web market tor market url darkmarket 2024
tor darknet darkmarket link dark market url
dark market onion tor market url tor markets 2024
dark market link darknet market links onion market
dark web search engines dark market 2024 tor dark web
dark web link darknet market lists how to get on dark web
darkmarket link deep web drug markets deep dark web
darknet drugs blackweb official website darknet market
where can i get diflucan
tor darknet dark market 2024 tor marketplace
dark websites darkmarket url darknet markets url
tor markets deep web drug links dark web link
darknet markets onion tor market dark web links
deep web drug links darknet sites darknet drug links
darkmarket 2024 darknet drug store darkweb marketplace
darknet market lists tor markets 2024 deep web markets
dark market darkmarket drug markets onion
dark market darkmarket url darknet search engine
dark web link dark web links deep web markets
dark web drug marketplace deep web markets darknet markets onion
tor markets dark web market links darkmarkets
deep web drug url dark web market links tor darknet
dark web link darkweb marketplace deep dark web
dark web sites darknet sites free dark web
dark markets 2024 darknet drug store darknet drug links
tor marketplace dark market list darkmarket link
dark market list dark internet dark web market
dark market link darknet markets black internet
dark web search engine darknet market lists dark web search engines
dark web markets dark internet tor markets links
tor markets links tor market url dark market url
darknet links dark market list best darknet markets
darknet links deep web drug url dark website
darknet drugs darknet markets links dark web market links
deep web drug links tor dark web darkweb marketplace
tor marketplace deep web sites drug markets dark web
dark web links dark markets darknet websites
dark markets dark market darknet markets onion
darknet markets onion tor dark web darknet market lists
darknet websites dark net darkmarket url
bitcoin dark web darknet market tor markets links
darknet markets onion dark web sites darknet drug market
tor market url cryptomarkets darknet dark web markets
deep web links dark internet dark net
dark market url dark web sites darknet drug links
free dark web tor market dark web markets
darkmarket link bitcoin dark web dark market url
darknet markets darkweb marketplace darknet marketplace
deep web search darkmarket url blackweb official website
darkmarkets tor marketplace darkmarket
tor darknet darknet drug links darknet market list
http://azithromycin.store/# zithromax 250
darknet seiten dark internet black internet
darknet markets 2024 dark web market darknet links
dark market darknet links deep web search
drug markets onion tor dark web cryptomarkets darknet
deep web sites dark markets 2024 dark market onion
darknet markets onion darknet links darkmarket url
darknet markets url tor markets 2024 deep web drug url
darknet markets onion address how to access dark web darknet market list
deep web drug markets https://darkweb-storelist.com/ – darknet seiten dark web market list
how to get on dark web deep web search darknet markets links
onion market dark web search engines dark web links
darknet market list dark market list dark web market list
dark web search engine darkmarket tor markets
furosemide 100mg: buy furosemide online – furosemide 40 mg
darknet search engine deep web drug links drug markets onion
onion dark website darknet markets 2024 dark web marketplaces
http://finasteride.men/# cost propecia price
darknet markets 2024 deep web sites tor markets
dark web sites darknet markets url tor drug market
darknet seiten dark web market tor market url
dark market list dark web websites tor market
darknet drug store darknet market list the dark internet
darknet market lists dark market 2024 dark web market urls
mexican pharmacy online
dark web link blackweb drug markets onion
darkmarket tor drug market free dark web
dark market onion darknet market links dark market link
dark net https://alldarknetmarkets.com/ – darknet market lists dark market onion
onion dark website dark markets dark web drug marketplace
dark internet blackweb darknet magazine
deep web drug links tor dark web tor market links
the dark internet darknet seiten dark market url
tor markets 2024 dark web search engines darknet site
dark web market how to get on dark web dark market 2024
dark web market onion dark website dark web links
deep web markets deep web drug links darknet marketplace
deep web drug store darknet market lists darknet drug store
dark web sites links dark web drug marketplace dark websites
dark web market links darkmarket link blackweb
deep web markets cryptomarkets darknet dark websites
dark web markets tor markets dark market onion
tor market links dark web site tor market url
darknet markets links dark market darknet markets onion address
darknet magazine darknet sites the dark internet
dark market 2024 dark web market darknet seiten
onion dark website dark market url dark market link
dark web access darknet markets onion address dark web drug marketplace
deep web markets tor marketplace how to access dark web
darknet markets darknet markets onion darknet site
dark web markets tor markets how to get on dark web
tor market darknet websites darknet market lists
darknet drug market dark web search engines darknet market list
dark web markets darknet market darknet markets links
best darknet markets cryptomarkets darknet darkmarket link
darknet drug links dark web site tor market url
dark web markets darknet marketplace tor darknet
tor markets 2024 darkmarket 2024 darkmarkets
darknet market darknet sites blackweb
best darknet markets darknet markets url free dark web
onion market darknet market lists darknet drug links
dark net https://darkweb-storelist.com/ – darknet drugs dark market link
deep web drug store dark market 2024 dark web marketplaces
deep web drug url deep web drug store onion dark website
dark market onion dark market onion darknet drug market
darkmarket 2024 darknet drug market dark net
onion market darknet market drug markets dark web
deep web drug url darkmarket 2024 drug markets onion
deep web drug links tor market links how to get on dark web
dark net blackweb dark web drug marketplace
deep web sites tor markets links darknet markets url
darknet site dark web markets deep web drug url
deep web markets darkmarket list deep web links
black internet dark web marketplaces best darknet markets
blackweb official website darknet market list dark web websites
darknet drug store darkweb marketplace darknet drugs
best darknet markets deep dark web free dark web
black internet onion market black internet
darkmarket 2024 https://alldarknetmarkets.com/ – darknet markets url darknet magazine
darkmarket 2024 dark market onion darknet market links
cryptomarkets darknet tor market the dark internet
darknet search engine dark market link cryptomarkets darknet
deep web drug markets dark market url dark web markets
the dark internet tor market links dark markets
buy cytotec pills online cheap п»їcytotec pills online Misoprostol 200 mg buy online
dark web sites links deep web drug markets how to access dark web
dark market list dark web site tor darknet
tor dark web how to get on dark web darknet drug market
onion market cryptomarkets darknet darknet drug store
darkmarket list deep web drug url darknet seiten
dark market link dark markets deep web links
deep web drug markets dark websites tor markets 2024
Indispensable content, essential reading.
best darknet markets darkmarket link darknet magazine
darkmarket 2024 darkweb marketplace dark web market list
dark internet dark website dark web search engines
darknet links dark web links dark web marketplaces
deep web drug markets darknet markets darknet drug store
onion market dark net blackweb official website
darknet drug store darkmarket 2024 dark web marketplaces
dark web link tor market darknet seiten
darknet links darknet links tor dark web
darknet sites deep web drug links darkmarket 2024
cheap lisinopril no prescription: over the counter lisinopril – how much is lisinopril 5 mg
dark web search engines darknet markets links darknet marketplace
deep web links dark web search engines darknet search engine
best darknet markets darknet market links blackweb official website
dark web link dark web sites links deep dark web
https://misoprostol.shop/# buy cytotec online
black internet deep web drug links dark market url
best darknet markets darknet drug links darknet market list
dark market 2024 darknet market links best darknet markets
the dark internet dark web websites darknet drug store
darknet markets links deep web sites free dark web
tor markets links dark web access dark web marketplaces
darknet market links deep web links dark web market urls
tor markets links darknet links onion dark website
best darknet markets darknet marketplace dark web sites
tor marketplace darknet market tor marketplace
free dark web https://darknet-marketspro.com/ – darknet drugs deep web drug markets
tor markets 2024 deep web links the dark internet
darknet market darkmarket link tor markets 2024
darkmarket link onion market dark internet
dark web sites dark web links tor drug market
darknet market list darknet market lists darknet market
tor markets links dark web markets tor market url
darknet drug links darknet search engine tor dark web
dark market link dark internet dark web market links
bitcoin dark web dark markets deep web drug url
tor darknet cryptomarkets darknet how to get on dark web
the dark internet cryptomarkets darknet tor market
dark market list dark web market list tor marketplace
darknet websites deep web drug markets black internet
black internet darkmarket url how to access dark web
blackweb https://darkweb-storelist.com/ – black internet cryptomarkets darknet
dark web access dark web market links dark website
dark market url dark web market list dark net
dark web links darknet sites dark web marketplaces
tor drug market darknet market links darknet drug market
tor darknet darkmarket darkmarket
dark web search engines tor darknet tor darknet
darkmarket deep web drug markets dark web market list
tor drug market darknet markets url cryptomarkets darknet
deep web drug links darknet websites dark websites
dark web websites dark web link dark web links
tor market darknet magazine tor market
tor market bitcoin dark web dark web search engines
darknet search engine how to access dark web darknet market
blackweb https://alldarkwebmarkets.com/ – tor drug market darknet links
darknet markets 2024 dark market onion darknet drug links
tor dark web darknet market links dark market url
dark web access drug markets dark web dark market url
darknet drug store dark web market urls deep web drug markets
dark web market links darknet markets links dark market url
deep dark web dark web access darknet market links
darknet seiten dark web market links darknet market lists
darkmarket url cryptomarkets darknet the dark internet
tor dark web dark markets darknet site
dark web websites darknet marketplace darknet links
hi! Микрозаймы на Tinkoff
https://zaimy-na-kartu-tinkoff.ru/
drug markets dark web darknet seiten deep web drug store
dark market onion dark web market urls dark market link
deep web drug markets darknet seiten dark web market list
dark web market links tor markets 2024 darknet markets 2024
darknet market cryptomarkets darknet dark web marketplaces
dark market list dark market onion darknet magazine
tor drug market dark website onion dark website
dark web site tor dark web darkmarket url
dark web markets tor darknet deep web sites
tor markets 2024 dark net blackweb
dark web market https://darkweb-storelist.com/ – bitcoin dark web darknet markets url
darknet links darknet sites dark website
darknet market deep web markets darknet drug store
dark markets 2024 dark market url the dark internet
dark web site deep web search dark web websites
tor markets links tor markets links drug markets dark web
dark market link dark web market urls darknet drug store
buy xenical online usa
tor dark web dark web markets dark internet
tor markets links dark web websites darknet market
darknet markets how to get on dark web dark market
dark markets dark web access tor market url
farmacia online senza ricetta: kamagra gold – top farmacia online
tor markets 2024 cryptomarkets darknet deep web drug links
dark market url dark internet tor markets links
darknet markets url dark web site dark market link
tor drug market darknet seiten darknet seiten
darknet magazine tor marketplace dark web market urls
dark markets deep web search drug markets onion
dark websites darknet drugs dark market url
dark markets bitcoin dark web dark market
best darknet markets darknet markets url tor market url
https://tadalafilitalia.pro/# comprare farmaci online con ricetta
dark net how to access dark web deep dark web
dark web search engines blackweb official website cryptomarkets darknet
http://farmaciaitalia.store/# comprare farmaci online all’estero
darknet sites darknet magazine best darknet markets
deep web drug markets deep dark web drug markets onion
darknet markets darknet drug links tor market links
tor markets cryptomarkets darknet darknet drug links
darkmarket 2024 dark market list dark internet
the dark internet dark market 2024 dark internet
Моему другу, который недавно увлёкся японской культурой, было трудно найти сайт, где он мог бы смотреть аниме онлайн в хорошем качестве. Большинство платформ предлагали контент среднего качества или с ограниченным выбором. Посоветовав ему этот сайт, я был рад увидеть его восторг, когда он обнаружил коллекцию аниме с высоким разрешением изображения. Теперь он проводит вечера, изучая различные жанры и серии, наслаждаясь чёткостью и качеством картинки, что делает его погружение в мир аниме по-настоящему полным.
dark websites darknet markets url darknet market lists
tor darknet how to access dark web dark web marketplaces
darkmarket 2024 darknet site tor drug market
deep web links dark market onion blackweb
darknet markets onion address dark web market dark web search engines
blackweb blackweb official website dark web market urls
tor markets black internet darknet markets
darkmarket tor marketplace darknet markets
darknet websites how to get on dark web darknet site
tor markets tor markets links blackweb official website
tor darknet dark web websites dark web links
dark web links dark web access dark markets
dark markets 2024 how to access dark web onion market
deep web links dark web site darkmarket link
dark web drug marketplace blackweb official website dark internet
deep web search darknet market lists darknet links
dark websites dark web market tor dark web
dark market url dark market url darknet websites
darkweb marketplace darknet markets dark web site
dark web markets deep web drug url dark web sites
tor market dark markets dark internet
how to get on dark web darkmarkets dark market link
tor market dark market blackweb
darknet market list deep web markets darkmarket link
drug markets dark web https://darkweb-storelist.com/ – darknet drugs deep web links
tor market url deep web markets how to get on dark web
dark web access dark web marketplaces dark market link
tor markets links darknet markets 2024 darkmarket list
darknet market dark web sites links darkmarket url
the dark internet dark web marketplaces darknet site
free dark web dark net dark market url
darkmarket 2024 best darknet markets darknet search engine
dark web market darkmarket list blackweb official website
dark web market blackweb official website dark market 2024
darknet sites the dark internet darknet sites
darkmarket darknet markets 2024 darkmarket list
dark web sites links dark web drug marketplace darknet markets url
dark web marketplaces tor darknet dark web websites
darknet market list https://darkweb-storelist.com/ – dark web search engine tor market url
farmacia online miglior prezzo: Farmacie a roma che vendono cialis senza ricetta – farmaci senza ricetta elenco
dark web search engine dark web sites links darknet marketplace
farmacie online affidabili farmacia online miglior prezzo farmacia online senza ricetta
Берите Микрозаймы онлайн на Tinkoff
https://zaimy-na-kartu-tinkoff.ru/
п»їfarmacia online migliore: Tadalafil generico – farmacie on line spedizione gratuita
blackweb darknet magazine darknet markets onion
deep web drug store free dark web deep web sites
darknet markets url darknet drug store darkweb marketplace
bitcoin dark web darknet search engine dark web site
bitcoin dark web darknet search engine dark markets 2024
Представьте моё удивление, когда я обнаружил, что мой кот – тайный фанат новых аниме! Каждый раз, как только я включаю новую серию, он занимает самое удобное место перед экраном и начинает смотреть с таким вниманием, будто пытается понять сюжет. Может, ему нравится яркая анимация? – думал я, но нет, кажется, он просто выбирает своего любимого героя. Как-то раз он даже начал мяукать в унисон с персонажами! Теперь у нас с котом есть совместное увлечение – мы вместе ищем самые интересные новинки аниме и проводим вечера за просмотром. Хотя, конечно, его комментарии оставляют желать лучшего!
blackweb official website dark web site tor markets 2024
darknet markets url darknet links darknet drug links
dark market 2024 deep web drug store dark market
darkmarket list darkmarket 2024 best darknet markets
dark market 2024 dark web access deep web drug store
dark web marketplaces darkmarkets dark web marketplaces
darkmarket list drug markets onion darknet markets onion address
dark web markets https://darkweb-storelist.com/ – darkmarket link deep web links
tor dark web darknet markets 2024 dark internet
https://farmaciaitalia.store/# top farmacia online
dark web market list black internet dark web marketplaces
dark web sites dark web links deep web drug url
darknet drug store dark web site darknet drugs
dark markets 2024 dark web sites dark web site
deep web drug links tor markets 2024 dark website
darknet markets dark web market tor market links
dark web market list deep web search deep web drug markets
drug markets onion darknet market lists free dark web
drug markets dark web https://alldarkwebmarkets.com/ – deep web links dark web links
darknet market lists blackweb deep web links
tor drug market tor market url dark market
darkmarket darknet drug links darknet market
https://sildenafilitalia.men/# cerco viagra a buon prezzo
darknet markets dark web markets darknet sites
deep web drug store darknet drug store darkmarkets
blackweb dark web access dark web websites
darknet drugs blackweb official website darkmarkets
dark web market dark net dark web search engine
darkmarket deep dark web darknet search engine
dark market onion darkmarkets blackweb
tor dark web https://darknet-marketspro.com/ – darknet markets onion address darknet drug market
darkmarkets darkmarket 2024 dark web websites
dark websites darkmarket link darknet market list
deep web markets deep dark web how to access dark web
deep web drug store dark web link darknet marketplace
dark market url deep web markets darknet websites
dark web link darknet websites deep web sites
dark web market links darknet links dark market
Представьте моё удивление, когда я обнаружил, что мой кот – тайный фанат новых аниме! Каждый раз, как только я включаю новую серию, он занимает самое удобное место перед экраном и начинает смотреть с таким вниманием, будто пытается понять сюжет. Может, ему нравится яркая анимация? – думал я, но нет, кажется, он просто выбирает своего любимого героя. Как-то раз он даже начал мяукать в унисон с персонажами! Теперь у нас с котом есть совместное увлечение – мы вместе ищем самые интересные новинки аниме и проводим вечера за просмотром. Хотя, конечно, его комментарии оставляют желать лучшего!
darknet sites blackweb official website tor markets links
deep dark web dark market darknet search engine
darknet markets onion dark web websites darknet links
dark web sites links dark web market list onion market
deep web search darknet links darknet websites
Я долго ждал, когда наконец-то смогу увидеть новые серии своих любимых аниме, и вот моя мечта сбылась! Наткнулся на этот сайт, где можно смотреть аниме 2024 онлайн, и это просто фантастика! Сайт занимает первое место в Яндексе, и неудивительно – здесь всё бесплатно, а качество просто на высоте. Больше не нужно тратить время на поиски – здесь есть все новинки, которые только можно пожелать. И все это доступно в несколько кликов, прямо у вас на экране в отличном качестве.
darknet market https://alldarkwebmarkets.com/ – darknet market list dark market link
tor markets links tor market the dark internet
darknet markets dark internet dark web market urls
deep web markets deep dark web darkmarket 2024
darkweb marketplace dark markets 2024 dark market onion
darkmarkets blackweb official website darkmarket url
tor market links dark web marketplaces darknet drug market
darknet site darknet market lists dark market link
dark web links how to get on dark web deep web drug url
drug markets dark web dark web site dark web market list
onion dark website darknet markets onion address darknet drug links
darkweb marketplace tor market url darkmarket link
dark web drug marketplace dark web search engine darknet drug market
farmacia online: farmacia online miglior prezzo – farmacia online migliore
tor drug market dark market url darkmarket
dark market url cryptomarkets darknet deep web drug store
darknet market list deep web markets dark markets 2024
deep web sites darkmarket link deep web sites
dark market darkmarket link darknet marketplace
the dark internet tor market darkmarket url
best darknet markets dark web market links dark web market list
darknet magazine deep web links darknet markets onion address
blackweb darknet drugs darknet seiten
dark markets cryptomarkets darknet darkmarket
dark web market urls dark market 2024 dark web search engine
bactrim ds 800 160
dark internet darknet market deep web drug markets
dark web sites links dark websites dark website
best darknet markets https://darkweb-storelist.com/ – darkmarket list darknet drug market
onion market dark websites dark market list
dark markets dark net darknet seiten
blackweb darknet site tor market links
darknet websites blackweb dark web market links
darknet seiten deep web markets dark web market list
dark market onion darknet websites dark internet
darknet websites darknet drugs free dark web
dark market darknet market lists darknet markets 2024
dark web link dark market link deep web drug url
darknet drug market darknet drug market darknet markets links
http://avanafilitalia.online/# comprare farmaci online all’estero
free dark web deep web markets dark net
deep web links deep web drug markets blackweb official website
darknet magazine dark market onion deep web markets
tor market https://darknet-marketspro.com/ – dark web market urls dark web sites links
dark web drug marketplace dark web marketplaces deep web markets
tor markets 2024 the dark internet drug markets dark web
darknet site deep web drug links dark internet
darknet market list darknet marketplace drug markets dark web
dark markets darknet drug market dark web links
deep web sites tor market url blackweb
cryptomarkets darknet dark market tor markets 2024
darknet drug store darknet marketplace deep web search
deep dark web darkweb marketplace dark web marketplaces
dark web access darknet market links darknet magazine
drug markets onion dark web drug marketplace dark web websites
dark web market urls dark market onion dark market onion
tor market tor market url deep web drug links
tor markets dark web search engines tor dark web
dark web search engines darknet links cryptomarkets darknet
tor markets links https://darkweb-storelist.com/ – black internet bitcoin dark web
deep web search the dark internet dark web market urls
darknet seiten darkweb marketplace tor market url
darknet market list dark market list darknet market
deep web links dark web sites dark web drug marketplace
how to access dark web dark web market list deep web drug links
dark web access dark web marketplaces darknet magazine
darknet markets onion drug markets dark web deep web search
darknet search engine deep web drug markets dark internet
dark web links dark web link deep dark web
darknet drug links darknet marketplace tor market url
dark market list darknet market lists deep web sites
dark web market list dark websites dark web market links
darknet drugs deep web markets dark market 2024
darkmarket 2024 cryptomarkets darknet deep web drug store
deep web links https://darkweb-storelist.com/ – darkmarket list deep web drug url
darknet websites darknet markets links deep web drug links
dark web sites links dark web websites tor markets links
drug markets dark web darkmarket url deep web drug url
pillole per erezione in farmacia senza ricetta: miglior sito per comprare viagra online – viagra generico sandoz
blackweb official website how to access dark web darknet markets links
darkmarket url darknet marketplace darknet markets onion address
drug markets onion deep web drug url deep web drug url
darknet drug market dark web sites links darknet markets onion
darknet markets 2024 dark market dark web marketplaces
tor markets tor market links black internet
darknet magazine deep web drug links tor markets
drug markets dark web dark web market links darknet drug store
http://tadalafilitalia.pro/# comprare farmaci online all’estero
blackweb official website dark web access dark net
darknet markets onion darknet markets deep web search
darknet markets dark market dark web links
tor market darkweb marketplace dark market url
how to get on dark web https://darkweb-storelist.com/ – dark web markets bitcoin dark web
deep web search darknet market lists dark web market urls
tor marketplace tor drug market darknet seiten
dark web sites links tor market url darknet markets links
the dark internet darknet market lists darknet drugs
blackweb dark market 2024 deep web drug url
darknet markets onion dark market onion deep web drug store
dark web sites links deep web drug url dark market onion
darkmarket link deep web search darknet marketplace
darknet markets url dark web search engine drug markets dark web
darkmarket list darknet markets darknet drugs
dark web websites darkmarket url darknet search engine
darknet search engine darknet market dark internet
I don’t think the title of your article matches the content lol. Just kidding, mainly because I had some doubts after reading the article. https://www.binance.info/sl/join?ref=P9L9FQKY
dark web marketplaces darkweb marketplace drug markets dark web
https://tadalafilitalia.pro/# farmacie on line spedizione gratuita
tor markets darknet drug store tor dark web
dark web markets https://alldarkwebmarkets.com/ – deep web drug store tor marketplace
comprare farmaci online con ricetta cialis generico comprare farmaci online all’estero
dark web link the dark internet how to access dark web
dark market 2024 onion dark website deep web drug url
darknet site deep web drug url darknet drug store
dark markets darkmarket url darknet websites
how to access dark web darknet market lists darknet markets url
darknet sites darknet market links darkmarket link
cryptomarkets darknet deep web drug links best darknet markets
darkmarket url darkmarket 2024 darknet market list
dark markets 2024 darknet market darkmarkets
darknet drug market darkmarket 2024 dark website
deep web drug store dark web market list tor market
deep web drug links onion market darknet markets links
darknet drug links bitcoin dark web tor marketplace
darknet drugs deep web search dark market onion
blackweb official website tor markets links dark web marketplaces
darknet drug links dark web markets darkweb marketplace
dark market url dark markets 2024 darknet markets url
darknet market list https://alldarknetmarkets.com/ – best darknet markets dark market link
darknet seiten deep web markets deep web drug url
best darknet markets blackweb darknet websites
darknet magazine how to get on dark web dark web sites links
dark web site tor markets 2024 darknet marketplace
deep web drug url dark market dark market link
cryptomarkets darknet darkmarket 2024 onion market
deep web links darknet websites darkmarket list
deep web drug url deep web drug links darkmarket url
dark web sites links dark market url bitcoin dark web
darknet marketplace darknet markets links deep web drug store
best darknet markets dark internet dark market 2024
darknet drugs darkmarket 2024 dark web markets
darknet drug market deep web drug links dark markets 2024
dark net onion market tor markets links
blackweb official website dark website darknet markets onion
tor market dark market onion blackweb official website
dark web drug marketplace dark market 2024 darkmarket
darknet magazine tor markets dark market
darknet search engine https://darkweb-storelist.com/ – darknet markets links darknet drugs
dark web market urls dark web access darkmarket url
darkmarket deep web sites dark web links
dark websites dark web site dark web search engine
darkmarket link best darknet markets dark market onion
comprare farmaci online all’estero: avanafil prezzo in farmacia – farmacia online miglior prezzo
dark web site dark web search engines tor dark web
darknet drug market darknet markets url deep web drug links
Берите Микрозаймы на тинькофф
https://mikrozaimy-na-tinkoff.ru/
darknet links bitcoin dark web darkmarket list
dark internet dark market darkmarket
darknet markets url dark web search engine tor marketplace
darknet market list tor dark web darknet markets 2024
dark web access dark web market list darknet magazine
deep web sites dark web search engine darknet drugs
tor markets links darknet market lists darknet drug links
deep web drug store darkmarket link darknet drug store
dark market link dark market dark market 2024
deep web search darkweb marketplace dark website
blackweb https://darknet-marketspro.com/ – onion dark website darknet markets
darknet markets onion address darknet markets dark market link
darknet search engine darknet markets 2024 darknet links
tor markets 2024 dark web search engine dark web markets
deep web drug markets dark web sites dark web market
dark website dark web sites links deep web drug url
darknet markets black internet darknet markets links
darknet websites dark internet darkmarket url
darknet search engine darknet markets darknet markets url
deep dark web deep web drug markets tor drug market
tor markets darknet market list darknet market links
blackweb official website darknet market links blackweb
the dark internet darknet markets onion address tor market url
onion dark website dark market onion onion market
gel per erezione in farmacia: viagra senza ricetta – pillole per erezione in farmacia senza ricetta
dark markets dark web links dark web market links
onion dark website onion market darknet markets onion address
dark websites https://darkweb-storelist.com/ – darknet search engine darknet drug market
tor marketplace dark web market drug markets dark web
black internet darkweb marketplace dark web marketplaces
dark market tor drug market dark web market
darknet magazine darknet market dark web market links
dark web market urls darknet links onion market
deep web drug links how to get on dark web tor market url
darkmarkets dark markets darknet market
tor drug market deep dark web darknet markets
darknet markets onion tor markets links tor market links
tor darknet deep web markets darknet market list
deep web drug markets tor dark web darknet sites
darknet drug market cryptomarkets darknet dark websites
dark market list how to access dark web darkmarket
dark website dark website dark web market links
https://tadalafilitalia.pro/# farmacia online senza ricetta
darkmarkets deep web drug url dark web search engines
dark web websites deep web links black internet
darknet drug links https://darknet-marketspro.com/ – tor market links darknet site
tor dark web dark web search engine dark web market list
dark web marketplaces deep web markets deep web links
darkmarket link deep web drug url dark market list
blackweb darkmarket 2024 dark net
dark market link dark web site dark web links
dark market list dark market onion dark web market links
dark web market links free dark web darknet links
how to access dark web darkmarket 2024 onion dark website
darknet search engine darknet market lists darknet marketplace
onion market deep web drug markets tor dark web
deep web drug url drug markets dark web darknet market
darkweb marketplace dark markets dark web access
best darknet markets dark net darknet search engine
darkmarket list darknet drug market dark web websites
black internet onion dark website blackweb
dark web sites bitcoin dark web dark website
dark websites tor darknet darknet marketplace
darknet websites dark web marketplaces deep web drug url
dark web markets darknet markets darkmarket url
darknet market list deep web drug url black internet
comprare farmaci online all’estero: farmacia online miglior prezzo – acquistare farmaci senza ricetta
dark website dark web market list darknet markets url
http://kamagraitalia.shop/# farmacia online
dark web marketplaces darknet site dark net
deep web drug links dark websites darknet market links
tor market url drug markets onion dark web site
dark web link onion market free dark web
darknet links dark market dark market list
tor markets tor market url tor marketplace
dark website darknet sites tor markets links
dark net darknet markets url tor markets
black internet tor markets darkweb marketplace
dark market url bitcoin dark web darknet drug store
BİZİ SİK BİZ BUNU HAK EDİYORUZ vurgunyedim.RkTnIiwvqs8e
dark web access darknet market dark market onion
deep web search darknet markets onion address deep web sites
darkmarket 2024 dark market url darknet market links
the dark internet tor marketplace dark web market urls
tor markets 2024 darkmarket list dark web markets
dark web search engine darkmarkets dark net
tor market url dark web market drug markets dark web
darknet markets dark market list darknet links
darknet sites tor markets onion dark website
tor dark web black internet deep web links
tor marketplace dark web search engine dark markets 2024
darknet markets 2024 black internet deep web drug markets
dark web market links darkmarket 2024 dark market url
darkmarket list darknet sites dark web sites links
dark web access darknet markets links darknet links
darknet market links darknet site dark market 2024
deep web sites dark web search engine darkmarket 2024
darknet markets links https://darkweb-storelist.com/ – darkmarket url dark markets 2024
darknet markets dark web link darknet drug store
darkmarket 2024 dark web websites darkweb marketplace
dark websites free dark web deep web links
Dealing with an Instagram deactivated account requires a nuanced approach. At social-me.co.uk, we specialize in understanding and resolving such issues. Our expertise in Instagram’s policies and procedures enables us to offer tailored solutions that address the specific reasons for your account’s deactivation. We focus on providing a comprehensive service that includes not only reactivation but also advice on maintaining a secure and active Instagram presence, ensuring your digital identity is preserved.
drug markets dark web bitcoin dark web tor markets 2024
tor market url best darknet markets dark market
dark web marketplaces dark web market list drug markets onion
the dark internet tor market tor darknet
dark web search engine black internet dark web market links
darknet drugs darknet search engine deep dark web
deep web drug url tor markets dark internet
darknet markets onion address darknet drug market dark internet
tor markets 2024 dark web search engines onion dark website
dark market onion tor market url darkweb marketplace
Микрозаймы онлайн на карту
https://minizajmy-online.ru/
dark net onion dark website tor market links
dark market 2024 dark markets drug markets onion
darknet drug links tor dark web darkweb marketplace
darknet market tor markets deep web markets
darkmarket url https://alldarknetmarkets.com/ – darknet market list tor market url
tor darknet darknet market lists deep web markets
deep web drug store darknet market darknet market
dark web market list free dark web deep web drug url
drug markets onion blackweb black internet
dark markets 2024 dark market darknet drug store
tor drug market tor markets 2024 deep web drug markets
tor market links deep web drug store dark web link
tor markets darknet markets tor market url
http://sildenafilitalia.men/# viagra online in 2 giorni
dark market 2024 dark web markets tor markets 2024
blackweb darknet market darknet market list
darkmarket deep web links darknet market list
drug markets dark web darknet magazine black internet
deep web sites darknet drug links dark internet
best darknet markets darknet markets onion black internet
dark web market black internet dark web links
dark web site dark web drug marketplace darkmarket
dark web market list the dark internet darknet market lists
darknet site darknet markets onion address drug markets onion
darkmarket link dark web marketplaces tor market links
dark markets 2024 tor market url dark web link
darkmarket 2024 dark web market links the dark internet
tor markets 2024 tor darknet the dark internet
dark markets 2024 dark websites darknet markets url
darknet site onion market darkmarket link
dark web drug marketplace https://darknet-marketspro.com/ – black internet free dark web
Facing the dilemma of a disabled Instagram account can be more than just a minor inconvenience; it’s like losing a part of your digital persona. This is where the experts at social-me.co.uk step in. With their specialized knowledge and experience in resolving such issues, they offer a beacon of hope. They’re not just about solving a problem; they’re about restoring your social media identity. Whether it’s a simple misunderstanding or a complex issue, they handle each case with the utmost care and professionalism, ensuring that your digital presence is reinstated with minimal fuss. Their commitment to legality and ethical practices makes them a reliable choice in a world where digital problems need more than just technical solutions. They understand the importance of every social media account and treat each case with the individual attention it deserves.
deep web drug store darknet search engine best darknet markets
dark websites drug markets dark web deep web drug url
tor dark web dark market black internet
darkmarket url darkweb marketplace darknet magazine
deep web drug store darknet websites darknet websites
dark markets darknet drugs darkmarket link
farmacia online migliore farmacia online senza ricetta farmacie online sicure
black internet dark web sites links darknet market lists
free dark web dark market onion drug markets onion
darknet markets darknet markets links dark net
deep web links dark web market links deep web links
darknet search engine dark web link darknet markets url
farmacie online sicure: kamagra gold – farmacia online miglior prezzo
darknet markets 2024 dark web market links darknet markets onion
dark web link darknet magazine dark web websites
dark web access free dark web darkmarket url
deep web drug markets darknet market lists black internet
darknet websites dark market 2024 darknet search engine
free dark web darknet markets url darknet market lists
the dark internet onion dark website darknet seiten
deep web sites dark web sites links dark market list
dark web websites deep web sites onion dark website
darknet markets url tor market url darknet drug market
how to get on dark web https://alldarknetmarkets.com/ – dark web access dark web search engine
deep web sites dark market url tor darknet
dark web search engines tor darknet tor marketplace
how to access dark web dark web link deep web drug store
darknet markets 2024 darkmarkets dark web links
tor dark web how to get on dark web darknet drug store
dark web market list darknet drug store darknet site
the dark internet dark web market links darknet market links
darkmarket darknet drugs dark internet
tor drug market darknet markets onion dark web websites
darknet drug store tor markets links darknet market lists
darknet websites dark websites darkmarket link
dark web links dark web search engines bitcoin dark web
darknet markets dark web links best darknet markets
blackweb deep web sites cryptomarkets darknet
tor darknet how to get on dark web onion market
darknet markets dark web market onion dark website
tor market links drug markets onion darknet drugs
dark web market urls dark web websites darkmarket link
darknet magazine blackweb official website how to get on dark web
darknet magazine dark web market urls dark net
darknet links dark web marketplaces dark website
darknet markets https://darknet-marketspro.com/ – drug markets onion darknet market lists
dark market 2024 dark web sites links best darknet markets
dark web link dark web websites deep web drug markets
darknet websites deep web sites blackweb official website
darknet markets onion address deep web links darknet websites
tor market links tor marketplace darknet market lists
dark web market links blackweb official website dark web search engine
onion market blackweb dark web link
tor drug market deep web search how to get on dark web
free dark web darknet sites darkmarket url
free dark web darknet magazine tor darknet
amoxicillin azithromycin
dark market deep dark web darknet market links
darknet search engine darknet markets links darkmarket url
https://sildenafilitalia.men/# viagra generico recensioni
blackweb dark websites darknet markets 2024
dark web market list dark websites how to access dark web
dark web sites onion dark website how to access dark web
deep web links darknet marketplace tor markets
dark web search engine dark market link tor market url
how to access dark web dark web marketplaces darkmarket url
dark internet deep web markets free dark web
cryptomarkets darknet https://alldarknetmarkets.com/ – darkmarket link deep web drug store
drug markets dark web onion market dark web search engine
darknet seiten darknet marketplace darknet marketplace
dark web search engine dark market deep web sites
dark web sites darknet marketplace dark market link
darknet drug links blackweb dark web markets
onion dark website dark market deep web drug store
tor market links darknet markets url dark web websites
deep dark web dark web search engines deep web drug markets
darkmarket link darknet markets onion address darknet markets url
dark web market list dark web markets deep dark web
darknet market tor markets 2024 dark market onion
darknet drug store deep dark web dark market onion
dark web search engines tor markets links tor markets links
dark web marketplaces darknet magazine darkmarket 2024
tor markets links darknet markets links deep dark web
tor market url darknet markets onion darknet marketplace
deep web search deep web drug store dark websites
drug markets dark web dark market 2024 darknet markets onion
blackweb official website darknet websites tor market
blackweb official website tor market darkweb marketplace
http://tadalafilitalia.pro/# acquisto farmaci con ricetta
tor market dark market dark web search engines
dark web market urls dark market dark web market links
how to get on dark web dark web site dark web sites links
onion dark website https://alldarknetmarkets.com/ – dark web market darkweb marketplace
darknet drug store free dark web drug markets onion
dark web websites darknet drug links deep web search
dark market link black internet tor drug market
free dark web darknet drug links tor markets
dark web search engines darknet markets url deep web drug store
dark markets 2024 best darknet markets dark web market list
black internet dark markets 2024 darknet markets onion
dark market onion dark web market links darknet websites
darkmarket url how to access dark web darknet market list
dark markets 2024 onion market deep web sites
darknet market lists darkmarket url darknet markets url
dark market 2024 dark market list dark web websites
dark web search engines tor market links tor darknet
dark markets 2024 dark markets 2024 dark markets 2024
darknet drug links tor markets tor markets 2024
dark market 2024 dark web access onion dark website
comprare farmaci online all’estero: kamagra gold – farmacie online sicure
darknet markets cryptomarkets darknet blackweb official website
darkmarket darknet magazine darkmarket list
black internet the dark internet darknet market lists
darkmarket link darknet seiten dark web markets
darkmarket list dark market deep web drug url
darkmarket list deep web search dark net
dark web drug marketplace https://alldarkwebmarkets.com/ – cryptomarkets darknet tor dark web
tor market deep web markets darknet markets url
darknet drug links darknet drug market deep web drug links
deep web search dark web search engines drug markets dark web
dark web link dark web search engine dark website
darknet drug market deep web markets darknet websites
black internet deep web drug store darknet market list
dark market link darknet drug market darkmarket
darknet drugs dark web drug marketplace deep web drug url
darknet drug market free dark web dark web drug marketplace
dark market url darkweb marketplace darknet drug market
blackweb official website darknet markets links dark web sites links
darknet search engine darkmarket url darknet market lists
blackweb official website deep web drug links dark market link
darknet markets onion darkweb marketplace black internet
deep web markets bitcoin dark web bitcoin dark web
darknet marketplace darknet seiten how to access dark web
tor marketplace deep web links black internet
dark market 2024 darknet markets onion address darknet drugs
darkmarket 2024 tor markets dark web access
dark websites tor drug market dark web drug marketplace
dark web link tor darknet darkmarket
darknet markets 2024 darknet drug links dark web search engines
darknet markets url https://alldarkwebmarkets.com/ – dark market list darknet drugs
darknet market lists black internet darknet market
darknet drug links tor darknet darknet markets onion address
darknet market lists dark markets 2024 darknet markets
dark internet how to access dark web darkmarket link
darknet drug links dark web search engine dark market list
dark web sites tor market url dark web market
deep web links darknet drug links darknet markets links
darkmarkets darknet markets url darkmarket 2024
dark net bitcoin dark web the dark internet
darknet market list tor dark web free dark web
tor markets 2024 darknet drugs deep web markets
tor market dark market url how to get on dark web
dark market list dark web search engines tor dark web
darknet drugs darknet drugs dark market link
darknet market lists dark web sites dark market url
darkmarket url dark web access the dark internet
dark web access tor markets links deep web drug markets
drug markets dark web tor markets darknet markets url
dark internet dark market onion cryptomarkets darknet
best darknet markets dark markets dark web market links
darknet magazine dark web links darknet site
darkmarket 2024 darknet markets url dark markets
dark web markets blackweb official website darknet sites
darkmarket link https://darknet-marketspro.com/ – dark web drug marketplace darknet links
darknet seiten the dark internet drug markets onion
blackweb official website dark web markets dark markets
darknet markets url tor markets 2024 dark web link
darknet search engine dark market url dark web marketplaces
free dark web tor marketplace dark web search engines
onion dark website darknet markets darkmarkets
darknet markets 2024 darknet drugs how to get on dark web
dark markets blackweb official website dark web websites
tor market tor darknet dark web markets
darknet markets dark web link darkmarket list
tor drug market darkweb marketplace tor drug market
deep web search tor market url darkweb marketplace
darknet marketplace darknet market links darknet markets url
tor marketplace dark web sites links darknet search engine
dark web market urls darknet markets onion best darknet markets
tor markets links darknet magazine dark websites
https://avanafilitalia.online/# comprare farmaci online con ricetta
tor markets links darknet links darkmarket list
darknet websites https://alldarknetmarkets.com/ – darknet markets onion tor darknet
darkmarkets darkmarket 2024 deep web drug links
dark web markets darknet websites darknet markets onion
dark market link darknet drug market onion dark website
darknet site dark web market urls tor market url
darknet drugs darknet market darknet market links
free dark web tor market tor market url
dark market darknet links dark web links
darkmarket list dark web links tor market url
the dark internet darknet market list tor dark web
dark market darknet market list darknet drug links
deep web links deep web drug url dark market onion
darkmarket url dark web websites darknet market links
darknet drugs darkmarket url dark web link
dark web sites dark web market darkmarket url
Online Bahis Şirketi: İnternet Üzerinden Bahis Yapmanın Avantajları
Online bahis şirketleri, spor bahisleri ve casino oyunları gibi çeşitli şans oyunlarını
internet üzerinden sunan platformlardır. Bu tür şirketler, bahis tutkunlarına dünya genelindeki spor etkinliklerine ve çeşitli casino oyunlarına erişim
sağlar. Online bahis şirketleri, geleneksel bahisçilere
veya kumarhanelere kıyasla bir dizi avantaj
sunar. Bu makalede, online bahis şirketlerinin neden bu kadar popüler olduğunu ve bu platformların avantajlarını ele alacağız.
1. Geniş Bir Bahis Seçeneği: Online bahis şirketleri,
kullanıcılara dünyanın dört bir yanındaki spor etkinliklerine bahis yapma fırsatı sunar.
Futbol, basketbol, tenis, at yarışları ve daha pek
çok spor dalında bahis yapabilirsiniz. Ayrıca, sanal sporlar ve e-spor gibi popüler seçenekler de sunulmaktadır.
2. Kolay Erişim: Online bahis şirketlerine erişim oldukça kolaydır.
Bilgisayarınızdan veya mobil cihazınızdan birkaç tıklamayla bahis yapabilirsiniz.
Bu, bahis tutkunlarının herhangi bir yerden ve herhangi bir zamanda bahis oynamasını sağlar.
3. Yüksek Oranlar ve Bonuslar: Online bahis şirketleri genellikle daha yüksek bahis oranları sunar.
Ayrıca, yeni kullanıcılara hoş geldin bonusları ve sadık müşterilere
çeşitli promosyonlar sunarlar. Bu, oyuncuların daha fazla kazanma şansına sahip olmalarını sağlar.
4. Canlı Bahis Seçeneği: Online bahis şirketleri canlı bahis seçeneği sunar.
Bu, maç veya oyun devam ederken bahis yapma fırsatı
sunar. Canlı bahis, heyecanı artırır ve anlık kararlar almanıza olanak tanır.
5. Çeşitli Ödeme Seçenekleri: Online bahis şirketleri, çeşitli ödeme seçenekleri sunar.
Kredi kartları, banka transferleri, e-cüzdanlar ve hatta kripto paralar gibi farklı ödeme yöntemleri kullanabilirsiniz.
Bu, kullanıcıların tercih ettikleri ödeme seçeneğini kullanmalarını sağlar.
6. Güvenilirlik ve Lisans: Çoğu online bahis şirketi, lisanslı
ve düzenlenmiştir. Bu, oyuncuların güvenli bir ortamda bahis yapmalarını sağlar.
Ayrıca, oyuncuların kazançlarını güvence altına alır.
7. Canlı Destek: Online bahis şirketleri genellikle 7/24 canlı destek sunarlar.
Bu, kullanıcıların herhangi bir sorunları olduğunda hızlıca yardım alabilecekleri anlamına gelir.
Online bahis şirketleri, bahis tutkunları için çeşitli
avantajlar sunar ve bu nedenle popülerliklerini artırıyor.
Ancak, bahis yapmadan önce güvendiğiniz ve lisanslı bir online bahis şirketi
seçmek önemlidir. Bu şekilde, keyifli bir bahis deneyimi
yaşayabilir ve kazançlarınızı güvence altına alabilirsiniz.
Online bahis şirketlerinin sunduğu geniş bahis seçenekleri ve promosyonlarla, bahis dünyasında eğlenceli ve
kazançlı bir deneyim yaşayabilirsiniz.
My web site 1xbet indir
comprare farmaci online con ricetta: farmacia online – farmacia online
deep web drug links dark web site darknet magazine
darknet links free dark web darknet magazine
onion dark website darknet market lists drug markets dark web
dark market url dark web market urls darknet market
dark markets 2024 dark web access tor market url
darknet marketplace dark market dark web market links
darknet drug store how to get on dark web darknet drug store
darknet markets darknet drug links dark market url
dark web links darknet markets url dark web market
dark web search engines onion dark website darknet markets links
anal sikis siteleri yaralandinmieycan.FrSO322DqXTm
blackweb official website https://alldarknetmarkets.com/ – onion dark website tor markets links
darknet drug store dark web search engine free dark web
black internet darknet seiten dark market 2024
tor dark web darknet seiten darknet market list
darknet market links deep web drug markets tor markets
darknet markets deep web markets best darknet markets
dark markets 2024 darknet search engine dark web search engines
deep web sites tor markets darknet drug links
dark market 2024 darknet markets onion darkmarket url
dark web market list darknet sites darknet markets onion address
best darknet markets darknet markets onion bitcoin dark web
best darknet markets dark web marketplaces deep web drug markets
dark market 2024 dark website dark market onion
deep web search darknet market list dark web market list
darknet magazine darknet drug links onion market
tor darknet dark net dark market url
darknet market deep web drug links dark net
dark net darknet drug market darknet site
darknet drug market darkmarket url dark markets
dark market list dark net darknet marketplace
cryptomarkets darknet darknet drug links deep web sites
darknet marketplace blackweb darknet markets
darknet links darknet drugs darkweb marketplace
deep web drug store dark markets dark web websites
darknet drugs https://darkweb-storelist.com/ – dark internet dark web access
tor market cryptomarkets darknet darknet market list
darknet search engine darkmarket link dark web sites
india pharmacy mail order: top 10 online pharmacy in india – Online medicine order
dark web market dark market 2024 dark web websites
dark web access cryptomarkets darknet darknet market links
dark web websites darkmarket dark web site
darknet search engine darknet markets tor market
darknet sites darknet markets deep web drug url
Микрозаймы онлайн на карту
https://mikrozaimy-na-kartu.ru/
dark web sites the dark internet dark market onion
darkweb marketplace tor dark web darkweb marketplace
dark market 2024 cryptomarkets darknet darknet drug store
mail order pharmacy india indian pharmacy Online medicine home delivery
dark web websites dark web drug marketplace darkmarket
deep web search dark web link onion dark website
drug markets dark web deep dark web dark web markets
dark websites darknet market lists dark web access
deep web search dark web markets the dark internet
darknet drugs dark web link cryptomarkets darknet
tor markets links darknet links deep web links
darknet site dark web link darkmarket url
darknet markets onion dark web drug marketplace onion market
darknet seiten dark markets drug markets onion
darknet drug store deep web markets onion market
deep web search darknet markets url how to access dark web
dark net tor market url dark web search engines
darknet links dark market 2024 dark web site
darknet markets 2024 tor markets dark web marketplaces
free dark web https://darknet-marketspro.com/ – darknet magazine darkmarket 2024
tor dark web dark web drug marketplace dark web markets
best darknet markets onion market tor markets links
dark market how to get on dark web best darknet markets
black internet dark websites onion dark website
darknet seiten dark web marketplaces darknet market
https://canadapharm.shop/# canada drugs
tor dark web tor dark web cryptomarkets darknet
deep web drug store tor darknet darkmarkets
tor drug market darknet site tor markets
darknet search engine dark market onion tor market links
deep web drug markets dark web market links deep web search
dark markets drug markets dark web deep web drug markets
deep web drug links dark websites blackweb official website
darknet seiten darknet websites dark websites
darkmarkets tor markets dark market list
free dark web darknet markets url darknet links
darkmarkets tor marketplace darkmarket 2024
indian pharmacy: buy prescription drugs from india – buy medicines online in india
dark internet darknet markets onion darkmarket list
onion dark website dark market 2024 darknet market lists
darkmarket list dark internet dark web sites
darkweb marketplace dark web sites dark market url
darkmarket url dark web market list dark web search engines
canadian pharmacy online ship to usa: onlinecanadianpharmacy 24 – canadian pharmacy ltd
darkweb marketplace blackweb official website onion market
darknet seiten dark web marketplaces drug markets dark web
deep web drug url dark web market links dark markets
dark market 2024 darknet drug store deep web search
tor markets links https://alldarknetmarkets.com/ – deep web drug markets dark market list
darkmarket 2024 bitcoin dark web dark web access
darknet websites tor drug market onion dark website
darknet websites darknet market lists dark market
дверь техническая металлическая https://texnicheskiedveri.ru/.
dark web marketplaces dark markets dark market 2024
dark market link darknet marketplace darknet site
darkmarket link darkmarket 2024 darknet drug market
tor markets links how to get on dark web tor markets
dark web market list dark web market list dark markets 2024
dark web websites dark market darknet seiten
tor markets links dark market dark web market links
darknet site tor market links darkmarket list
dark web market urls darknet drug market tor dark web
dark web drug marketplace tor market dark web sites
darkmarket link cryptomarkets darknet deep dark web
darknet markets 2024 free dark web dark websites
darknet magazine dark markets 2024 darkmarket link
darknet market lists darkweb marketplace darknet drug store
dark web websites darknet markets onion address tor marketplace
deep web drug url darknet market dark websites
darknet search engine darkmarket link darknet drugs
darknet drug store dark web access darknet drug store
deep web drug store dark web sites links dark web search engine
darknet markets url how to get on dark web dark web site
how to access dark web dark internet darknet sites
dark websites how to access dark web darknet site
darknet links dark web market urls darknet market lists
darknet market list https://alldarkwebmarkets.com/ – dark internet darkmarket link
darknet marketplace onion dark website tor markets
dark websites dark web market links bitcoin dark web
how to access dark web darknet markets darknet market lists
dark web market list cryptomarkets darknet tor drug market
dark web links tor markets 2024 darknet markets 2024
deep web drug store dark web websites tor markets
darknet drug links tor market how to access dark web
darknet markets darknet seiten deep web search
darknet market list dark web websites bitcoin dark web
darknet market lists darknet websites dark web drug marketplace
Друг проходил через трудный период. Подарил ему яркий букет от “Цветов.ру”. Цветы стали символом поддержки и дружбы. Рекомендую всем, кто хочет поднять настроение близким. Советую! Вот ссылка https://sweetpix.ru/salavat/ – доставка цветов недорого
dark web sites darknet drugs darknet drug store
dark market onion deep web sites how to get on dark web
dark web search engines tor markets links darknet market list
the dark internet darkmarkets darknet site
darknet drug links darknet drug links dark web link
darknet drug market dark web access darknet markets links
darkweb marketplace dark web access deep dark web
onion market dark web market links darknet markets onion address
onion market dark markets 2024 dark website
darknet market dark web link dark web site
darknet markets onion address darknet markets links darkweb marketplace
darknet drug store tor dark web dark net
darkmarket list darknet websites tor drug market
darknet market lists dark market list dark web sites links
drug markets onion darknet drug store dark web search engines
darkmarket url free dark web dark web search engine
dark web drug marketplace dark websites darknet market lists
dark web link tor market dark market 2024
tor market how to access dark web darknet search engine
deep web drug markets dark web markets deep web drug links
deep web drug store https://darkweb-storelist.com/ – drug markets onion dark website
darknet seiten dark web sites links blackweb official website
tor marketplace cryptomarkets darknet tor marketplace
darkmarket dark web market links darknet market list
dark web drug marketplace dark internet how to access dark web
tor markets 2024 black internet how to access dark web
dark web drug marketplace darknet sites free dark web
darknet search engine dark web market list darknet market
tor markets links darknet markets 2024 darknet links
http://indiapharm.life/# online shopping pharmacy india
dark web site deep web search dark web websites
blackweb official website dark web sites darknet sites
darknet market darknet seiten dark websites
dark market onion tor market url tor drug market
dark web drug marketplace dark market onion the dark internet
tor drug market darkmarket link darknet market lists
dark web links deep web links tor drug market
darknet marketplace darkmarket url darknet markets links
darknet markets onion address dark web marketplaces dark web sites links
dark web market list darknet drugs deep web search
how to get on dark web dark market url tor markets 2024
deep web drug links dark web link darknet markets 2024
darkmarket 2024 how to get on dark web dark market onion
darknet seiten darknet marketplace dark web market
darkmarket url tor market links darknet magazine
dark web sites dark web access deep web drug url
dark web market urls dark websites how to access dark web
dark web sites darknet search engine bitcoin dark web
the dark internet tor market darknet markets 2024
onion dark website dark market link black internet
bitcoin dark web the dark internet darknet search engine
dark market url dark web links onion market
dark markets 2024 https://darknet-marketspro.com/ – darknet market list darknet links
tor market links darknet markets onion address free dark web
dark web sites dark web markets dark website
dark web access darkmarket url tor darknet
darknet markets url darknet markets links tor markets
dark web search engines dark web market list bitcoin dark web
darknet seiten dark market link tor dark web
dark web search engines best darknet markets darknet market links
how to get on dark web onion market best darknet markets
dark web market list darknet markets onion address darknet drug market
drug markets onion dark market url dark web market links
dark web search engine dark market list dark web market list
https://canadapharm.shop/# canadian discount pharmacy
darknet markets links onion market darknet markets onion
tor drug market dark market tor marketplace
darknet marketplace deep web drug store darknet markets url
dark web sites darkmarkets dark web market urls
deep web drug links how to access dark web darknet drugs
darknet sites dark websites dark market 2024
Online medicine order: online pharmacy india – pharmacy website india
dark internet tor markets 2024 darknet markets url
black internet dark website darkmarket 2024
tor market links drug markets onion deep web search
darkmarket darknet marketplace tor market
darknet drugs drug markets dark web dark web links
dark market onion dark markets 2024 tor market url
dark market link cryptomarkets darknet dark websites
tor darknet how to get on dark web darknet seiten
darknet markets dark market dark web access
darknet market list darknet marketplace darknet marketplace
dark web drug marketplace darkweb marketplace dark web market links
dark web search engines dark web marketplaces drug markets dark web
darknet market list darknet site darkmarket url
deep web search deep web drug markets darknet drug store
darknet site onion market dark web sites
best darknet markets dark web link dark market 2024
dark websites https://darknet-marketspro.com/ – darkmarket url deep web sites
cryptomarkets darknet bitcoin dark web deep web drug store
dark web access darkmarket url dark market url
dark web search engine blackweb dark web sites links
darknet market lists darknet drug market tor drug market
darkweb marketplace tor marketplace deep web drug markets
darknet links dark web market urls tor market
dark market list best darknet markets darknet drug market
tor markets links darkmarket list darkmarket url
darkmarket link drug markets onion tor markets links
tor darknet dark web market free dark web
deep web drug links dark web marketplaces dark web access
how to get on dark web deep web links how to get on dark web
dark net tor drug market darknet drug market
bitcoin dark web tor market url dark market url
darknet markets links darknet market links tor markets
dark market url dark market darknet sites
darknet site free dark web darkmarket url
dark web market urls the dark internet darknet markets onion
darknet websites drug markets onion dark web sites
dark market 2024 dark web markets tor market links
tor market links deep web markets tor markets 2024
dark web market urls black internet darknet markets 2024
free dark web best darknet markets tor marketplace
darknet markets onion address tor markets links dark websites
dark internet darknet market list tor markets 2024
deep web drug markets darkmarket 2024 darknet site
blackweb tor drug market darkmarket list
the dark internet free dark web deep web drug links
dark market link darkweb marketplace darknet search engine
tor marketplace darknet websites dark market
dark web market darknet magazine dark web marketplaces
dark web markets deep web search deep web drug store
darknet markets onion darknet market lists cryptomarkets darknet
tor marketplace https://darknet-marketspro.com/ – tor markets links dark markets 2024
tor drug market deep web links darkmarket link
tor market url darknet links dark markets 2024
dark web links dark market dark web links
ремонт диванов https://peretyazhka-bel.ru/.
darkmarket link the dark internet darknet links
bitcoin dark web how to get on dark web dark market 2024
tor market dark market dark market 2024
dark net best darknet markets darkmarket link
dark market darknet websites dark web market
drug markets dark web darknet markets links darknet markets url
tor markets dark market 2024 darknet market lists
dark web marketplaces tor dark web dark markets
deep web drug store dark web links dark websites
tor dark web deep web markets darknet links
tor market darknet markets url tor dark web
deep web drug links dark web market darknet market lists
darkmarket darknet market links drug markets onion
free dark web best darknet markets darknet drug links
dark markets 2024 dark web sites deep web search
deep web drug markets darknet markets links dark internet
dark market list free dark web darkweb marketplace
darknet site tor market dark website
darkmarkets darknet drug links darknet drugs
dark web sites links dark markets 2024 dark market 2024
dark web site darknet market list tor dark web
darknet market lists the dark internet dark web sites links
dark web market links tor market url darknet market links
free dark web darknet market links darknet market
darkmarkets darknet drug store dark web sites links
darknet market lists tor marketplace dark internet
dark web market urls https://alldarknetmarkets.com/ – how to get on dark web darknet sites
dark web site free dark web darkmarket list
darknet markets onion tor markets links drug markets dark web
darknet markets onion tor dark web tor market links
dark internet free dark web dark market list
darknet markets onion address black internet dark web link
dark markets 2024 darknet markets url tor market links
bitcoin dark web tor markets links darkmarket url
dark markets 2024 tor dark web darknet drug market
blackweb tor darknet darknet drug links
darknet site tor markets 2024 dark market url
dark internet darkmarket 2024 darknet seiten
dark websites darknet market links dark market list
dark market 2024 deep web drug markets darkmarket
dark market 2024 deep web links dark market 2024
darkmarket link onion market tor market links
drug markets onion darknet links dark web sites links
deep web drug store dark market tor drug market
deep web sites darkweb marketplace dark markets
black internet dark website dark web websites
deep web markets tor dark web drug markets dark web
onion dark website darknet markets links darknet drug market
darknet drug links best darknet markets dark websites
dark web market dark web market list dark web market urls
dark market 2024 blackweb deep web drug markets
darkmarket list darknet drug market deep web drug links
dark web search engine darknet markets onion darknet market
darknet drug store tor marketplace deep web drug links
deep dark web darknet markets onion dark website
dark web links darkmarket dark web market urls
darknet drugs tor dark web deep web links
darknet markets links https://darknet-marketspro.com/ – dark market list dark web drug marketplace
darknet links tor market dark market url
dark market url deep web links dark web access
cryptomarkets darknet darknet seiten dark markets 2024
darknet drug market darknet markets url darknet markets url
tor marketplace darknet markets url darknet markets onion
india online pharmacy: Online medicine home delivery – best online pharmacy india
darkmarket dark web market list dark web site
darkmarket dark web search engines dark net
http://mexicanpharm.store/# reputable mexican pharmacies online
darknet market list darkmarket link dark web site
darknet markets onion deep dark web darknet markets 2024
darkmarket list darknet site deep web drug markets
tor darknet dark web access darkmarket
dark web drug marketplace deep web search dark market
darknet seiten darknet markets onion dark web marketplaces
darkmarket list deep dark web dark web sites links
deep web drug store tor drug market deep web drug links
dark website deep dark web dark internet
deep dark web tor darknet tor markets 2024
darknet markets links blackweb official website dark websites
how to get on dark web tor market links dark web search engines
dark web markets darknet markets onion address tor darknet
blackweb official website darknet drug store tor market links
tor market dark web market urls dark web sites
how to get on dark web dark web sites links dark websites
drug markets dark web darknet sites deep web search
dark market list deep web drug links darknet websites
blackweb official website the dark internet darkmarket
dark web links darknet markets onion address deep web search
dark markets how to access dark web darknet markets onion address
darknet seiten https://darknet-marketspro.com/ – darkmarket url deep web drug url
darknet search engine darknet market links dark web link
drug markets onion cryptomarkets darknet tor drug market
canadian pharmacy phone number is canadian pharmacy legit pet meds without vet prescription canada
drug markets dark web dark web search engines dark markets
darknet sites darknet links the dark internet
dark web market links tor darknet darknet site
darkmarket link dark web site tor marketplace
dark markets 2024 dark markets darknet site
darkmarkets dark web sites links tor darknet
dark web site darknet magazine bitcoin dark web
dark market 2024 onion market darknet sites
blackweb official website darknet markets blackweb official website
dark web site dark web drug marketplace darkmarkets
dark market onion darknet drugs dark web search engines
darknet markets onion address dark web marketplaces bitcoin dark web
best darknet markets darknet markets onion deep dark web
deep web drug url tor marketplace darknet site
dark web sites darknet market lists dark web access
deep web search darkmarket url tor marketplace
dark net dark market list darknet markets
dark web websites darknet websites darknet drug store
darknet markets url dark web site how to get on dark web
dark web market urls dark market tor markets 2024
darknet drug store tor marketplace dark market list
darknet magazine dark web access darkmarket list
dark websites dark web websites drug markets onion
dark market onion darkweb marketplace darkmarket link
darknet market links deep web drug markets dark web markets
deep web drug links tor markets darkweb marketplace
dark web markets dark market list darkweb marketplace
dark web sites https://darknet-marketspro.com/ – darknet marketplace deep web sites
top 10 pharmacies in india: online shopping pharmacy india – best india pharmacy
dark web search engine darkmarket link darknet markets
darkmarkets darknet seiten deep web drug markets
blackweb official website dark website dark web drug marketplace
dark web market urls darkmarket 2024 dark web market links
tor dark web tor marketplace darknet links
how to access dark web dark website blackweb official website
dark website deep web markets darkweb marketplace
tor markets dark web market urls black internet
dark web drug marketplace deep web sites darknet market lists
dark net dark market onion onion market
deep web markets deep web drug url darknet drug store
dark web market list dark web market urls darknet market links
dark market list tor dark web dark web sites
darknet markets 2024 tor market links dark markets
dark web link dark web link darknet websites
dark web drug marketplace darknet market links dark web market links
darknet markets url dark web search engine deep web drug store
how to access dark web darknet websites tor marketplace
dark website dark web websites darknet market list
darknet sites deep web drug url darknet market lists
dark web site dark web markets dark web search engines
canada drug pharmacy: canadianpharmacymeds – certified canadian pharmacy
darknet markets onion market darkmarket link
darknet links dark web search engine deep web search
darknet sites the dark internet drug markets dark web
darknet drug store bitcoin dark web darknet websites
tor market links https://darknet-marketspro.com/ – dark market list darknet drug market
darkmarket list dark web market list tor market url
darknet markets onion address darkmarket list darknet market
darknet drug market dark net darknet markets
dark website dark market url best darknet markets
darkmarket url black internet onion dark website
deep web drug links tor markets links onion dark website
darknet magazine dark net tor marketplace
deep web drug links dark web sites darkmarket
dark web site dark market 2024 dark websites
dark web links dark website dark web access
tor marketplace dark market tor marketplace
dark websites how to get on dark web darkmarket url
dark website cryptomarkets darknet tor market url
dark market url darknet market dark market 2024
deep web drug store dark market link dark web marketplaces
darknet markets links dark web market dark web websites
darknet sites deep web drug url dark market
deep web drug url tor market darknet market
darknet market links darknet websites dark market url
onion market darknet drug links bitcoin dark web
tor markets links dark website darkmarket 2024
best darknet markets deep web sites darkweb marketplace
buying prescription drugs in mexico: п»їbest mexican online pharmacies – mexican online pharmacies prescription drugs
dark markets tor dark web dark web sites links
best darknet markets dark web links dark market url
darknet drug links darkmarket link darknet drug store
http://mexicanpharm.store/# mexico drug stores pharmacies
dark market link dark market url tor markets
dark web market urls tor drug market dark web markets
dark net darkmarket url onion dark website
tor markets links https://darknet-marketspro.com/ – darkmarket list deep web drug url
dark markets 2024 darknet markets links deep web sites
drug markets dark web dark web link dark web market list
darkmarket 2024 dark web link tor dark web
dark web drug marketplace tor market url darknet marketplace
dark web market darknet market lists deep web links
dark web links darknet seiten tor markets 2024
darknet site drug markets onion deep dark web
dark web sites dark web markets dark web sites links
deep web drug markets darknet search engine deep web markets
dark web access darknet sites darknet market
deep web drug links deep web drug markets darknet markets onion address
darkmarket list deep web links dark web links
deep web drug markets cryptomarkets darknet tor dark web
tor dark web darknet markets url dark web markets
dark markets darknet seiten dark web market
dark web market urls dark market url dark web market
deep web drug url darknet markets onion dark web drug marketplace
darknet links darknet markets darkmarket url
darknet drugs dark market onion drug markets dark web
tor markets links darkmarket 2024 darknet drug store
dark web market list tor marketplace darknet markets links
darknet search engine drug markets dark web tor market links
dark market 2024 dark web link dark internet
tor markets blackweb official website darknet markets onion
darknet marketplace dark net dark web search engines
drug markets onion deep web drug markets dark market url
darknet markets links darknet search engine darknet market
dark web marketplaces dark markets 2024 darkmarket list
tor marketplace how to access dark web dark websites
tor marketplace dark markets darknet markets url
tor marketplace dark web market dark market onion
darknet markets links https://alldarknetmarkets.com/ – deep web sites tor market
darkmarkets deep web drug store tor market links
dark web marketplaces darkweb marketplace darknet magazine
drug markets dark web dark web access dark market onion
dark web links darkmarket 2024 deep web markets
deep web markets dark markets 2024 dark internet
darknet markets onion address tor markets 2024 dark web websites
dark net darkmarket url deep web drug store
darkmarket url deep web drug links dark web market
darknet site darknet market dark web links
deep web search dark internet dark websites
dark web market urls tor market dark web markets
dark web sites links darkmarket darknet seiten
onion market deep web drug url dark web marketplaces
darknet markets onion address dark internet onion market
how to access dark web dark web websites dark market list
dark web marketplaces onion market dark web links
onion market darknet markets darknet markets onion
deep web search dark market list how to get on dark web
dark net dark market 2024 deep web drug url
tor drug market blackweb official website tor markets
dark market list darknet markets dark market link
tor market links dark market list darknet markets 2024
darknet drug links dark web markets dark web sites
dark net dark web search engine darknet magazine
dark web websites how to access dark web onion dark website
darkweb marketplace darknet market lists deep web drug markets
darkmarket url darkmarket url onion market
darknet seiten dark web market list dark markets
https://mexicanpharm.store/# mexico drug stores pharmacies
tor markets the dark internet darkmarket
dark web websites the dark internet dark web websites
deep web markets dark market link dark web marketplaces
dark web market urls https://alldarknetmarkets.com/ – darknet drug store darknet markets url
darkmarkets dark net tor marketplace
darknet seiten dark web drug marketplace dark web sites links
tor darknet dark websites tor drug market
darknet search engine darknet marketplace deep dark web
darknet magazine blackweb dark web markets
dark internet dark market link darknet magazine
tor markets links darkmarket darknet markets onion
darkmarket 2024 dark web marketplaces drug markets dark web
deep web search best darknet markets dark net
onion dark website deep web drug url dark web market
darknet markets dark web websites darknet magazine
cryptomarkets darknet the dark internet dark web market
darknet markets onion deep dark web darknet market links
free dark web darkmarket dark web site
how to get on dark web how to access dark web darkmarket 2024
dark website deep dark web onion market
dark web market links how to access dark web dark web websites
blackweb darknet magazine tor market
dark web market deep dark web dark web search engines
cryptomarkets darknet dark web market darknet drug links
tor darknet dark web market urls darkmarkets
black internet onion dark website darknet market links
tor markets dark markets darknet links
dark web websites dark websites deep web links
darkmarkets dark web search engines darknet sites
dark web markets free dark web darknet markets url
dark web market dark web search engines deep dark web
dark markets 2024 dark web sites links dark web search engine
dark markets dark web link free dark web
darknet markets url deep web drug store dark web market links
dark web market list darknet markets onion address drug markets onion
dark web market links dark web search engine deep web drug links
dark net deep dark web dark internet
reputable canadian pharmacy: canadian drug prices – best canadian pharmacy to order from
dark web drug marketplace dark web sites darknet markets 2024
onion dark website dark web sites links dark websites
darknet sites black internet blackweb
http://canadapharm.shop/# my canadian pharmacy rx
darknet marketplace deep web sites deep dark web
cryptomarkets darknet darknet search engine dark web markets
darknet markets onion dark market onion deep web drug links
darknet magazine darkweb marketplace deep web sites
dark web link darknet magazine darknet drug links
free dark web dark website darknet marketplace
how to get on dark web darknet market darknet websites
dark net dark web search engine deep web links
deep web sites darknet markets url tor drug market
deep web drug store deep web drug markets tor drug market
how to access dark web dark web access darknet magazine
deep web sites drug markets dark web dark web sites links
free dark web darknet site darknet marketplace
cryptomarkets darknet https://alldarknetmarkets.com/ – tor market tor market url
darknet market links dark market onion tor markets 2024
tor markets links deep web sites dark web market urls
darkmarket how to access dark web deep web drug store
darkmarket url dark web market darkmarket url
deep web search deep web drug url dark market 2024
the dark internet drug markets dark web dark website
onion market darkmarket list dark web drug marketplace
darkweb marketplace dark web sites dark net
tor market dark web access how to access dark web
tor market links https://alldarkwebmarkets.com/ – tor darknet dark markets 2024
darknet links darknet market list blackweb official website
dark market link free dark web deep web drug markets
darknet site darknet magazine dark web sites
darkmarket 2024 dark web drug marketplace darknet sites
darkmarket link dark market darknet drugs
dark web markets darknet drugs black internet
darknet links tor markets 2024 dark web search engine
darknet market list onion market dark web market
dark markets 2024 darknet markets links darknet market
darknet drug market darknet search engine deep web markets
dark web site deep web drug links deep web sites
darkweb marketplace darkmarket link tor drug market
darknet search engine tor markets links tor dark web
darknet drug store deep web search darknet seiten
darknet markets links dark web link deep web markets
dark market url tor darknet dark market list
darknet sites dark market list darknet sites
dark websites dark market darkmarket link
darknet markets dark web access tor market links
how to access dark web darkmarket link tor markets links
blackweb tor market url dark market 2024
dark web market links dark web markets dark web sites
dark markets darknet market dark web marketplaces
dark web sites https://darknet-marketspro.com/ – darknet markets onion drug markets onion
deep dark web dark market blackweb
dark market dark market list tor market
onion market dark market list dark web market
darkmarkets darknet markets onion address darknet markets url
darknet site how to access dark web dark market link
bitcoin dark web dark web access darkmarket url
Dealing with an Instagram deactivated account requires a nuanced approach. At social-me.co.uk, we specialize in understanding and resolving such issues. Our expertise in Instagram’s policies and procedures enables us to offer tailored solutions that address the specific reasons for your account’s deactivation. We focus on providing a comprehensive service that includes not only reactivation but also advice on maintaining a secure and active Instagram presence, ensuring your digital identity is preserved.
Contra contrariis curantur — Противное излечивается противным.
http://batmanapollo.ru
dark web links darknet market links drug markets dark web
darknet marketplace https://darkweb-storelist.com/ – dark web access cryptomarkets darknet
Что характеризует высокий уровень
развития личности человека. Мышление образами.
Человек живет в обществе. Шопенгауэр фото в молодости.
Философия человек это. Тест на тип личности мбти
самый точный. Логическое мышление в психологии это.
Цель в жизни это определение 9.3.
the dark internet how to access dark web blackweb official website
bitcoin dark web dark web market urls dark website
dark websites deep web drug links dark web search engines
tor marketplace dark web market darknet markets
dark web drug marketplace deep web drug links dark web marketplaces
dark market url onion market darknet market lists
darkmarket link dark market list darknet market
deep web drug url tor markets deep web markets
darknet links the dark internet darknet markets url
darknet search engine dark market url deep web links
dark web access drug markets onion darknet site
drug markets onion darknet links the dark internet
dark market url tor darknet darknet market lists
darkmarket darkweb marketplace onion market
darkmarket link darkmarkets bitcoin dark web
dark web market urls darkmarket 2024 dark web link
deep web sites dark net dark market url
darkmarket tor market links dark web drug marketplace
deep web drug url dark market list darknet links
tor market url darknet seiten dark web markets
deep web drug url dark web drug marketplace tor markets links
the dark internet deep web sites dark web sites links
darknet magazine https://alldarknetmarkets.com/ – dark market bitcoin dark web
darknet markets onion address dark web marketplaces dark web drug marketplace
darkmarket url blackweb dark web market
dark web market links deep web drug store darkmarkets
dark market onion darkmarket url black internet
darknet drug links https://darkweb-storelist.com/ – darknet markets url darkmarket
dark market link deep web drug url darknet drug links
dark web marketplaces dark web markets how to get on dark web
dark internet dark web link best darknet markets
free dark web bitcoin dark web blackweb
dark web search engine dark web access blackweb official website
free dark web darkweb marketplace deep web links
cryptomarkets darknet darknet markets onion dark market list
deep web sites darknet drugs how to get on dark web
how to access dark web tor darknet darknet site
drug markets dark web darknet markets onion free dark web
deep web drug url dark web market links tor markets
dark web search engine darknet search engine dark market link
best canadian online pharmacy: ed drugs online from canada – canadian pharmacy 24 com
darkmarket url deep web drug markets darknet drug store
darknet market links darknet market list black internet
drug markets onion deep web drug links deep web drug url
deep web sites darknet sites deep web search
dark web sites links darkmarket darkmarket list
deep dark web darkmarket link darkmarket list
darkmarket 2024 deep dark web tor market
best darknet markets darknet drug links tor market links
dark web sites links darknet magazine tor marketplace
best darknet markets deep web links darknet market lists
http://canadapharm.shop/# canada pharmacy online
dark market dark web sites links dark websites
drug markets onion dark market list drug markets dark web
darknet market https://darknet-marketspro.com/ – dark web links onion market
darknet drug links darknet market links darknet links
deep web markets darknet search engine dark web sites
purple pharmacy mexico price list: buying from online mexican pharmacy – purple pharmacy mexico price list
Почему стоит смотреть турецкие сериалы? Ответ прост: они завоевывают сердца миллионов зрителей! Эти сериалы – не просто истории, это целые миры, полные эмоций, интриг и неожиданных поворотов. Вам нравятся истории, которые заставляют задуматься? Или, может быть, вы предпочитаете легкую романтику? На turkbiz.tv есть все. Подумайте об этом: вы сами выбираете, что смотреть и когда. Это ваш шанс окунуться в уникальные истории с комфортом своего дома.
darknet markets 2024 dark market onion dark web market urls
deep web drug links tor drug market tor darknet
deep web search darknet search engine dark market 2024
deep web drug links https://darkweb-storelist.com/ – deep web markets darkmarket link
darknet links darknet market black internet
darknet magazine tor dark web dark web marketplaces
darkmarket link dark web access darknet market links
dark internet darknet sites dark internet
robaxin 750 price south africa
free dark web dark web drug marketplace dark web site
bitcoin dark web tor markets links dark web market list
darknet seiten darknet markets dark web market
darkmarkets darknet links dark web links
darknet sites darknet sites dark market
tor markets links dark web link darknet drug market
tor market url darknet market list tor market url
dark website tor markets how to get on dark web
darknet drug market dark web sites darknet drugs
darknet market list darknet market lists darkmarket list
dark market dark market list tor dark web
tor markets links onion dark website darknet drug store
dark market list tor markets links darknet marketplace
bitcoin dark web darknet links dark website
deep web search darknet seiten darknet magazine
bitcoin dark web dark market onion dark market url
deep web search dark web links dark market 2024
black internet darknet links tor markets 2024
dark web markets dark web search engines darkmarket url
darknet site https://alldarknetmarkets.com/ – cryptomarkets darknet darkmarkets
blackweb deep web drug links darkweb marketplace
dark web websites how to access dark web onion dark website
how to access dark web darknet market links dark market
blackweb official website dark market link tor markets 2024
how to get on dark web darknet market lists how to access dark web
the dark internet best darknet markets darkmarket url
dark web websites https://darkweb-storelist.com/ – deep web drug store dark web market links
how to get on dark web dark internet deep web drug links
darkmarket url dark web market links darknet drug store
blackweb darkweb marketplace dark web market urls
dark web markets darkmarket 2024 tor marketplace
darknet magazine darkmarket list how to get on dark web
tor market darknet site darknet market links
drug markets onion free dark web best darknet markets
deep dark web dark market onion bitcoin dark web
deep web sites darknet drugs darknet drugs
dark web market the dark internet darkmarket url
dark web site dark markets cryptomarkets darknet
onion dark website darkmarket list dark net
darknet markets 2024 deep web drug store darkmarket url
dark web links onion market blackweb official website
darknet market links darkmarkets dark web site
dark internet darknet drug links dark websites
dark web market deep web drug store onion market
how to access dark web darknet drug store dark websites
deep web drug links blackweb official website darknet site
tor markets 2024 dark web link how to access dark web
darknet market links tor drug market best darknet markets
the dark internet blackweb official website darknet markets url
dark web markets tor markets deep web drug links
deep dark web dark web search engine tor drug market
drug markets onion deep web drug links dark internet
dark web market list https://darknet-marketspro.com/ – darkmarket list darknet seiten
tor markets dark market list darkweb marketplace
dark market onion dark web drug marketplace dark market onion
darknet search engine darknet markets onion address dark websites
tor markets links deep dark web dark market 2024
dark market onion darkmarkets tor market links
darknet markets 2024 https://darkweb-storelist.com/ – deep web markets dark market 2024
darknet markets 2024 tor market links how to access dark web
darknet magazine tor market url darknet magazine
deep web drug url darkmarket link tor markets 2024
darkweb marketplace dark markets 2024 bitcoin dark web
darknet markets onion how to get on dark web darkweb marketplace
dark internet dark web search engine dark market list
deep web links dark market url dark markets 2024
tor market darknet site dark web sites links
darknet site dark web market urls darkweb marketplace
onlinecanadianpharmacy 24 canadian online pharmacy canada pharmacy online legit
dark websites tor markets links dark websites
darknet markets links darknet websites tor dark web
how to get on dark web deep web sites tor market
darknet markets url darknet drugs tor dark web
dark web links blackweb dark web market
darknet search engine dark markets 2024 darkweb marketplace
canadian discount pharmacy: best rated canadian pharmacy – pharmacy rx world canada
darknet market lists darknet marketplace darknet websites
dark web market urls tor markets 2024 dark web market
how to access dark web darknet drug store tor market links
darknet sites tor dark web dark web market
drug markets dark web how to access dark web tor marketplace
dark web websites https://darknet-marketspro.com/ – darknet market black internet
tor marketplace dark web market list deep web links
darknet markets darknet markets 2024 blackweb
dark web market links darknet websites tor marketplace
deep web drug markets tor markets deep web drug url
darkmarket 2024 darknet drug links dark web drug marketplace
https://indiapharm.life/# indian pharmacies safe
dark web market dark market url deep web sites
darknet markets onion address how to access dark web darknet markets 2024
dark web site https://darkweb-storelist.com/ – blackweb darknet site
tor market dark market darknet markets onion
dark web markets dark web marketplaces dark web market urls
dark net best darknet markets darknet market links
deep web drug url darknet drug market darkmarkets
dark web drug marketplace the dark internet darkmarket list
free dark web dark market link bitcoin dark web
dark web site darknet websites tor dark web
tor drug market darkmarket link tor darknet
dark markets drug markets onion dark web sites
На сайте turkbiz.tv доступны турецкие сериалы 2023 онлайн. Эти сериалы представляют собой симбиоз традиционных тем и современных визуальных технологий, что открывает новые перспективы для анализа культурных тенденций. Просмотр этих сериалов онлайн дает зрителям доступ к широкому спектру жанров, отражающих современные социальные и культурные реалии Турции.
deep web sites dark market link onion dark website
dark web sites links tor darknet darknet drug store
deep web drug links deep web drug store deep dark web
dark web search engine darkmarket dark market
drug markets onion darknet markets onion darknet markets
dark markets 2024 deep web drug store darkmarkets
free dark web tor market dark web markets
how to access dark web dark web market list darkmarkets
darknet marketplace darknet drug market deep web links
darkmarket list deep web search dark web site
deep web drug store dark web search engine best darknet markets
drug markets onion deep web drug links darkmarket url
dark web links dark web sites deep dark web
darkmarket url cryptomarkets darknet how to get on dark web
darknet market lists how to get on dark web tor drug market
tor markets darkmarket dark web websites
blackweb deep dark web darknet markets 2024
dark web site https://alldarknetmarkets.com/ – darknet markets onion dark market url
darknet websites deep web sites free dark web
dark web market list blackweb official website darknet drug links
dark markets 2024 darkmarket list darknet markets url
onion dark website dark market darknet markets onion address
dark website dark web search engines onion dark website
free dark web darknet markets onion address dark web marketplaces
darknet site darknet markets onion address deep web drug links
dark market link https://alldarkwebmarkets.com/ – dark web websites darknet market
free dark web dark markets darkmarket link
darkmarket list dark net dark market 2024
dark market darknet sites darknet markets links
darknet market links tor markets 2024 darknet market links
tor dark web tor market links dark market link
darknet site deep dark web darknet site
dark web market urls onion dark website black internet
darknet market lists deep web drug links darknet seiten
darknet markets links dark website darkmarket link
darkmarket best darknet markets deep web drug links
dark net blackweb darknet market
deep dark web darknet markets links dark markets
best darknet markets deep web drug url dark website
dark web search engine deep web drug links how to get on dark web
how to get on dark web tor markets links darkmarket url
dark web websites black internet deep web markets
tor dark web dark market darknet drug store
tor market darknet links deep web drug markets
darknet marketplace deep web drug store darkmarket
tor markets links darkmarket dark web sites links
deep web drug url deep web drug links darknet drug links
dark web websites deep web drug links darknet market
dark web sites darknet market list dark web marketplaces
onion dark website blackweb darkmarket url
darknet market https://darknet-marketspro.com/ – deep web markets how to get on dark web
the dark internet dark market 2024 dark web search engines
darknet markets links dark web site tor markets links
tor drug market onion dark website dark web links
darknet market darknet markets darknet links
darknet sites dark web sites darknet drug store
darknet markets onion address dark market 2024 deep dark web
how to get on dark web dark market 2024 darknet market lists
deep web markets https://alldarkwebmarkets.com/ – deep web drug store darknet markets 2024
dark market list tor drug market dark market 2024
tor market darknet site deep web links
dark market onion dark web sites dark market 2024
darknet search engine dark market best darknet markets
drug markets onion dark web sites darknet markets onion
deep web drug store dark websites dark market link
darknet sites darknet drug links deep web drug links
darkmarket 2024 darknet markets url darkmarket link
how to get on dark web darkmarket url darknet sites
tor drug market darknet drugs dark market 2024
darkmarket tor marketplace darknet drugs
darkmarket 2024 dark web drug marketplace black internet
tor darknet darknet drugs dark web search engines
deep web sites deep web drug links tor marketplace
darknet drug links tor market deep web markets
dark internet deep web search dark markets 2024
dark websites dark market link darknet drug market
mexico pharmacies prescription drugs: п»їbest mexican online pharmacies – mexican border pharmacies shipping to usa
darknet websites onion market darknet market lists
dark web search engines blackweb official website cryptomarkets darknet
dark websites darknet links free dark web
onion market darknet drug store deep web drug url
darknet market links dark web market darknet market lists
dark web drug marketplace darknet market lists darkmarket list
darknet drug market https://alldarknetmarkets.com/ – drug markets onion tor market url
drug markets dark web how to get on dark web darknet markets url
drug markets dark web dark markets 2024 darkmarkets
darkmarket link darknet search engine dark web search engines
tor market url darknet magazine dark market list
http://canadapharm.shop/# online canadian drugstore
dark internet darknet markets url blackweb
darknet market list dark market darkmarket url
deep web sites dark web link dark web market links
dark web websites https://darkweb-storelist.com/ – darkmarket url dark market
https://canadapharm.shop/# legitimate canadian online pharmacies
darknet seiten black internet blackweb official website
darknet market lists deep web links dark web search engines
darknet markets deep dark web drug markets onion
dark markets 2024 darkmarket dark web market links
darknet seiten dark web market cryptomarkets darknet
tor markets 2024 dark web links darkmarkets
darkmarkets deep web markets darknet sites
mexican pharmacy: buying from online mexican pharmacy – mexican pharmaceuticals online
deep web drug store tor markets how to access dark web
tor markets links blackweb blackweb
dark web link how to access dark web dark internet
free dark web dark web links dark web marketplaces
bitcoin dark web dark market 2024 dark web market links
darknet drug store deep web links darknet markets url
albuterol without a prescription
deep web sites how to get on dark web deep web search
tor darknet blackweb official website darknet market lists
darknet site onion market the dark internet
deep web search darknet marketplace darknet marketplace
dark market onion cryptomarkets darknet deep dark web
If you need assistance with how to reactivate Facebook, social-me.co.uk is equipped to guide you through the process. Our expertise covers the full spectrum of Facebook’s reactivation policies and procedures. We offer tailored solutions based on the specific reasons for deactivation, ensuring a smooth and efficient reinstatement of your account. Our service is designed to not only reactivate your account but also to provide insights on avoiding future deactivations.
darknet market list darknet market links onion market
deep web search bitcoin dark web tor markets links
darknet drugs the dark internet dark market link
blackweb official website tor markets dark website
dark web markets darknet site tor market links
tor darknet dark web links tor market url
dark markets dark web market deep web drug links
drug markets dark web https://alldarknetmarkets.com/ – dark websites best darknet markets
Отличная статья, благодарю!
В качестве благодарности поделюсь с вами информацией: наличники из дерева на окна в Санкт-Петербурге для для загородных домов являются отличным выбором среди владельцев домов.
Наличник фигурный купить в спб для домов – это превосходный вариант, который сочетает в себе эстетику, прочность и экологию. Если вы хотите придать своему загородному дому особый шарм, рассмотрите деревянные наличники.
В Питере работает много организаций, которые занимаются изготовлением и монтажем деревянных наличников. Одна из них – компания КубЭра. Предлагает большой ассортимент моделей, цветов и отделок.
deep web sites dark net dark markets 2024
darkmarket url dark market list dark market url
darkmarket list dark market 2024 deep web drug url
dark web market the dark internet darknet magazine
deep web sites darknet marketplace dark web sites
dark net deep dark web dark web search engine
darknet markets url darknet site onion market
tor markets deep web markets darkmarkets
tor marketplace https://alldarkwebmarkets.com/ – black internet best darknet markets
dark web market urls darknet market links deep web drug markets
deep web markets darknet markets onion dark market link
darknet markets url darkmarket link drug markets dark web
dark web links dark web link darknet drug market
darknet links blackweb official website darknet magazine
deep web search tor drug market dark web site
dark web link tor market links darkmarket 2024
blackweb tor markets 2024 dark web markets
dark market list darknet markets links tor darknet
darknet magazine dark website darknet links
Ad usum internum — Для внутреннего употребления.
http://batmanapollo.ru
tor market links the dark internet dark web websites
dark web site darkweb marketplace darknet markets 2024
dark market dark web links tor marketplace
dark market dark web links darkmarket
dark market deep web links tor market
darknet drugs darknet drugs best darknet markets
darknet magazine darknet market links darknet search engine
mexican mail order pharmacies: mexican border pharmacies shipping to usa – mexican pharmaceuticals online
В пути на важную встречу мой автомобиль внезапно сломался. Срочно нуждающись в деньгах на ремонт, я обратился на mikro-zaim-online.ru и получил займ без отказа. Благодаря этому я смог быстро починить машину и успеть на встречу.
MIKRO-ZAIM – быстрые займы
Наши контакты: Зеленодольская улица, 36к2, Москва, 109457
dark web market list dark markets 2024 black internet
dark market url darknet seiten blackweb official website
dark web sites links darknet markets the dark internet
dark market url deep web markets dark web websites
dark market link darknet markets url tor markets 2024
darkmarket list dark web market urls tor marketplace
dark web link deep web links dark market 2024
darknet market drug markets onion dark internet
tor markets 2024 tor markets links dark web links
tor drug market deep web drug links cryptomarkets darknet
tor market links https://alldarknetmarkets.com/ – darknet drugs how to access dark web
blackweb drug markets dark web dark web market links
darknet websites deep web search darknet drug market
deep dark web how to access dark web darknet markets onion address
bitcoin dark web tor marketplace cryptomarkets darknet
dark internet deep web drug url tor marketplace
deep web drug url https://alldarkwebmarkets.com/ – drug markets dark web tor markets links
darknet markets url deep web links deep web search
dark web site darknet sites how to get on dark web
darknet seiten tor market dark market link
tor market url darknet markets links tor dark web
В пути на важную встречу мой автомобиль внезапно сломался. Срочно нуждающись в деньгах на ремонт, я обратился на mikro-zaim-online.ru и получил займ без отказа. Благодаря этому я смог быстро починить машину и успеть на встречу.
MIKRO-ZAIM – взять займы на карту онлайн
Наши контакты: Зеленодольская улица, 36к2, Москва, 109457
dark web search engine darknet markets dark web market
darkmarket url best darknet markets darkmarket 2024
darkweb marketplace darknet sites onion dark website
tor dark web darknet links darknet market lists
tor markets 2024 darknet links deep web search
deep web drug links bitcoin dark web tor dark web
canadian king pharmacy: canadian king pharmacy – safe canadian pharmacy
dark markets tor market url free dark web
dark web websites deep web sites how to get on dark web
dark web links tor markets 2024 darknet markets onion address
deep web search darknet drugs onion dark website
darknet magazine drug markets onion dark website
black internet tor markets 2024 dark market 2024
darkmarkets blackweb official website darknet seiten
tor darknet darknet search engine free dark web
dark web websites darknet site dark website
best darknet markets blackweb deep web search
http://indiapharm.life/# mail order pharmacy india
tor market dark web links darknet market list
dark web markets dark market onion darknet drug store
deep web drug url dark markets darknet links
dark markets bitcoin dark web how to access dark web
tor markets 2024 best darknet markets darknet market links
darkweb marketplace tor markets dark web market list
best darknet markets tor market url darknet market list
tor markets 2024 dark web websites dark web site
darkmarket 2024 dark web site dark web market list
tor darknet https://alldarknetmarkets.com/ – darknet markets dark web marketplaces
cryptomarkets darknet dark web markets dark internet
darknet drug market darknet drug store drug markets onion
darknet markets 2024 darknet seiten darkmarket url
how to access dark web https://darkweb-storelist.com/ – deep web sites onion market
dark market 2024 deep web sites how to get on dark web
darknet site darknet market darknet magazine
dark web sites links darknet site darkmarket 2024
darkmarket darknet markets onion address dark web market
darknet market lists darknet marketplace darknet seiten
dark web sites links dark markets 2024 dark web marketplaces
deep web markets deep web markets dark web websites
trazodone hydrochloride
the dark internet blackweb official website black internet
tor marketplace darkmarkets dark web search engine
dark website darknet drug links onion market
dark web link tor market url darknet market links
tor markets 2024 dark web site tor markets links
onion market dark web sites links onion dark website
tor dark web deep web links darknet sites
dark market onion how to get on dark web darknet drug links
onion market darkmarket link blackweb official website
darknet drug market the dark internet dark web access
darknet markets links deep web links darknet marketplace
darknet market dark net dark markets 2024
darknet websites dark web market list tor market url
darkmarket link dark web market list dark market list
onion market dark web links darknet seiten
deep web links darknet markets url deep web links
onion dark website darkmarket url tor markets
black internet tor markets tor markets
dark web marketplaces darknet search engine darknet market list
deep web search darknet search engine darknet markets
dark web sites tor markets 2024 tor market links
dark markets https://alldarknetmarkets.com/ – dark web access darknet market links
darknet drug store darkmarket 2024 black internet
onion market dark web link the dark internet
darknet websites darknet sites how to get on dark web
darknet marketplace the dark internet darknet drug market
dark web search engines deep dark web deep web drug links
tor marketplace https://darkweb-storelist.com/ – dark market url best darknet markets
cryptomarkets darknet dark market 2024 how to access dark web
deep web drug url dark market url drug markets onion
darknet markets darknet markets onion address dark web markets
dark web links dark market list darknet market
best darknet markets darknet markets black internet
deep web links the dark internet dark web drug marketplace
dark web drug marketplace dark web sites dark markets 2024
deep web drug url dark websites deep dark web
dark internet tor marketplace dark web drug marketplace
dark web market urls dark market 2024 dark web market
dark web site darknet market lists best darknet markets
tor dark web deep web search darkmarket list
tor drug market cryptomarkets darknet dark web sites links
tor marketplace onion dark website blackweb
dark web links drug markets dark web dark web marketplaces
dark market link darknet market list dark market onion
darknet markets url dark markets dark web marketplaces
onion dark website darkmarket 2024 blackweb
bitcoin dark web dark net tor marketplace
darknet market links dark markets 2024 dark web site
dark net black internet dark web access
drug markets onion dark web search engine dark web sites
tor markets darkweb marketplace cryptomarkets darknet
tor dark web best darknet markets dark market
darkmarket url deep web drug url best darknet markets
deep web links dark web link dark web markets
darknet seiten the dark internet dark web links
how to get on dark web deep web drug markets tor drug market
darkmarket darknet market list dark market url
blackweb official website https://darknet-marketspro.com/ – darknet seiten dark market 2024
dark web access deep web drug store dark web access
darknet drug store https://alldarkwebmarkets.com/ – tor dark web darkmarket link
dark market link dark web markets onion dark website
darknet links deep web sites dark web link
dark web market urls dark market list deep web drug markets
deep dark web dark web access deep web markets
darknet markets onion tor marketplace cryptomarkets darknet
dark markets 2024 darkmarket dark web sites links
dark net darkmarket 2024 dark web site
dark market 2024 darknet markets onion tor markets links
deep web drug links darknet markets deep web links
deep web links the dark internet dark web drug marketplace
best darknet markets tor market dark web drug marketplace
deep web drug links deep web drug links dark web access
cryptomarkets darknet darkmarket list dark web search engines
tor marketplace tor markets black internet
Online medicine order: best online pharmacy india – buy prescription drugs from india
dark web websites how to access dark web dark internet
dark market 2024 dark web marketplaces drug markets onion
cryptomarkets darknet dark web link darknet markets onion
how to access dark web darkmarket link darknet markets
blackweb official website dark web websites deep web markets
darknet market list dark web search engines dark website
Займы на карту
https://mikrozajmy-na-kartu.ru/
deep web drug store darknet marketplace darknet market links
darkmarket list darkweb marketplace dark web site
tor markets links onion dark website deep dark web
blackweb official website darknet market links darkweb marketplace
tor market url dark market darknet marketplace
http://canadapharm.shop/# ordering drugs from canada
darknet sites dark website dark market url
tor dark web deep web drug url black internet
darknet links https://darknet-marketspro.com/ – darknet drug store deep web markets
deep web drug url tor marketplace free dark web
dark market list tor market dark web market list
dark web market links darkmarket darkweb marketplace
tor marketplace drug markets onion dark market link
dark market list tor market url tor market
darknet drug market https://alldarkwebmarkets.com/ – tor markets 2024 tor market url
dark web marketplaces tor dark web deep web drug markets
dark web link darkweb marketplace tor drug market
darkmarket 2024 dark web drug marketplace dark net
darknet markets onion dark web link tor markets 2024
deep web sites darknet seiten deep web sites
dark market link dark web websites darknet markets onion address
darknet drug market dark web market list deep web search
black internet darknet market list darkmarket
drug markets dark web tor markets 2024 darkmarkets
darknet search engine tor markets dark market link
dark web site how to access dark web dark web market links
drug markets dark web onion market dark web access
dark web market list darknet market lists darknet links
dark web market list deep web markets deep web markets
darknet drug store dark web market urls dark web market urls
darknet marketplace dark market url darknet drug market
dark markets drug markets onion the dark internet
darknet market lists darkmarket url tor darknet
darknet market darknet magazine deep dark web
darknet drugs deep web links blackweb
darkmarkets how to get on dark web deep web drug url
deep web markets dark web link drug markets onion
dark web site tor market url dark market url
dark web marketplaces dark market link tor markets
dark web access darknet sites free dark web
dark web websites darknet markets onion address darknet links
tor market url deep dark web darkweb marketplace
blackweb official website https://darknet-marketspro.com/ – darknet links darknet seiten
darknet drug links tor market dark web sites
dark web sites dark web market links dark web websites
darknet drug links dark web market links deep web sites
darknet marketplace tor dark web free dark web
darknet seiten https://darkweb-storelist.com/ – dark web market dark web marketplaces
darknet sites dark web market dark market onion
darknet marketplace dark web search engine dark web site
deep web links tor market url dark web websites
darkmarket link best darknet markets deep web markets
darknet markets links darknet seiten onion market
dark market link dark market list darknet marketplace
dark web market list darknet markets url dark websites
dark web link dark web search engines tor market links
dark websites darknet drug links bitcoin dark web
tor drug market darknet sites darkmarket link
deep web drug links the dark internet dark market list
deep web sites dark web site dark web sites
dark web links dark web market links darknet market links
darknet markets 2024 dark web link dark internet
the dark internet darkmarket 2024 tor markets links
tor drug market tor market links dark markets
darknet market bitcoin dark web deep web drug url
reputable indian pharmacies best online pharmacy india reputable indian online pharmacy
darknet markets links darknet market lists cryptomarkets darknet
dark web market tor marketplace dark markets
darknet drugs darknet markets url tor drug market
deep web drug store deep web drug links drug markets onion
dark web markets how to get on dark web tor dark web
deep web drug store darknet drug market darknet websites
bitcoin dark web darknet drug links darknet marketplace
dark net dark market list dark internet
darkmarkets darknet search engine dark web market urls
dark markets 2024 deep web markets darknet sites
dark market list https://alldarknetmarkets.com/ – darknet market links black internet
darknet seiten deep dark web darknet drug links
darknet magazine how to get on dark web dark market link
dark web access https://darkweb-storelist.com/ – dark net dark web market
how to access dark web darknet markets onion address dark web marketplaces
the dark internet dark web search engine deep web drug url
dark website dark web market links dark web sites links
dark websites bitcoin dark web deep web drug links
darkmarket 2024 dark web link tor markets
tor market url darknet links dark web link
tor drug market darknet markets onion address darkmarket link
darknet magazine tor drug market drug markets onion
dark web market darknet drug store best darknet markets
tor marketplace darknet markets 2024 darkmarket 2024
tor marketplace dark web markets dark markets 2024
tor markets deep web drug links dark web link
darknet market list darknet drug links dark web access
dark web access dark market url dark market 2024
darknet seiten the dark internet deep web drug url
darknet drugs dark market url darknet markets links
india pharmacy: indian pharmacies safe – reputable indian online pharmacy
darknet markets onion address deep dark web darknet search engine
dark web markets dark web marketplaces darknet links
darkmarket 2024 dark internet deep dark web
deep web drug markets darkmarkets darknet market
dark market 2024 darkmarket link darknet search engine
darkmarket the dark internet bitcoin dark web
darknet marketplace deep web markets darkmarkets
dark market onion drug markets dark web deep web sites
drug markets onion dark markets dark web access
dark market onion dark web marketplaces dark web drug marketplace
dark net https://darknet-marketspro.com/ – darknet magazine tor markets links
https://mexicanpharm.store/# mexico pharmacy
dark web markets darkmarket link darknet magazine
darknet market list dark web market dark web links
tor markets links dark market onion dark web link
darknet markets links tor market bitcoin dark web
dark internet https://alldarkwebmarkets.com/ – darknet drugs deep web links
tor market dark market dark market link
bitcoin dark web how to access dark web dark markets 2024
http://canadapharm.shop/# canadian pharmacy 24h com
dark internet darknet websites darkmarkets
tor market url dark net tor darknet
tor darknet dark web marketplaces dark web marketplaces
tor market url drug markets dark web tor darknet
dark web marketplaces dark web sites links onion dark website
dark web markets darknet markets onion address blackweb
dark web sites darkmarket link darkmarket
onion market dark net darknet market lists
darknet market list free dark web tor darknet
dark web market list darknet drugs dark markets
darkmarket 2024 dark web market urls dark market 2024
the dark internet dark market 2024 darkmarket url
dark web links dark market list onion dark website
dark market url dark market onion dark web market
dark web sites darknet sites dark web search engines
deep web search darknet markets onion darknet drugs
darknet market cryptomarkets darknet blackweb official website
drug markets onion darknet market deep web drug url
darknet market lists dark internet dark web link
the dark internet darknet marketplace darknet markets 2024
darknet drug links dark web websites onion dark website
dark web sites links tor marketplace tor markets links
dark web drug marketplace onion market darknet markets 2024
free dark web the dark internet dark market link
darknet market list deep web drug links dark web markets
darkweb marketplace https://alldarknetmarkets.com/ – tor market links darknet drugs
darkmarket 2024 dark market link how to access dark web
darknet markets 2024 dark market url bitcoin dark web
darkmarket 2024 darknet markets onion address dark web markets
darknet markets onion darknet market links tor dark web
tor markets 2024 darknet market list deep web sites
onion dark website https://alldarkwebmarkets.com/ – dark web market urls dark web sites
dark web access darknet site tor drug market
darknet markets darknet markets onion address darknet markets onion address
darknet market tor dark web dark web search engine
darkmarket list darknet drugs darkweb marketplace
darknet search engine black internet bitcoin dark web
dark web search engine tor market links dark website
dark web market list darknet drug market cryptomarkets darknet
mexico pharmacy: buying prescription drugs in mexico online – purple pharmacy mexico price list
tor market url onion dark website darkmarket url
deep web markets darkmarket link darknet seiten
dark web links darknet drug market dark web access
dark web link the dark internet darknet market
dark web link tor markets darknet markets
darkmarkets blackweb darknet markets onion address
darknet markets links darknet links dark web websites
tor markets links darknet seiten dark net
how to access dark web dark website dark web sites links
darknet drug store dark markets 2024 darknet drug links
how to get on dark web dark internet darknet drug store
tor markets deep web search dark web sites links
darknet sites darknet magazine dark web access
dark market url tor darknet darknet websites
tor markets links drug markets dark web darkmarkets
darknet market links dark markets 2024 darknet markets onion address
darknet marketplace darknet seiten tor markets links
darknet drug links onion market dark web market
tor dark web https://darknet-marketspro.com/ – dark web market darkmarket 2024
darknet markets 2024 tor drug market darkmarket 2024
darknet magazine https://alldarkwebmarkets.com/ – dark web drug marketplace tor drug market
dark web market list dark websites dark market 2024
dark market onion deep web sites darknet sites
best darknet markets darknet drug market tor marketplace
dark web markets blackweb blackweb
black internet darknet links dark web link
onion market dark markets dark market 2024
dark web markets darknet seiten dark web sites links
dark web market links darknet drugs darkweb marketplace
dark markets best darknet markets black internet
dark web markets darknet magazine tor markets
tor markets links how to get on dark web dark web market list
mexican pharmacy: mexican pharmaceuticals online – mexico pharmacies prescription drugs
dark web market list black internet onion dark website
darkmarket 2024 deep web drug url deep web search
tor drug market dark web marketplaces darknet market lists
tor market links dark web markets darknet site
dark web site best darknet markets dark market 2024
darknet drug market dark markets deep web drug store
dark web markets darkmarket link darkmarket
darknet market links deep web drug store tor marketplace
tor market links deep web links dark website
darknet markets 2024 darkmarkets dark websites
deep web sites dark websites deep web search
darknet market lists dark web market links darkmarket url
darkmarket link tor markets links deep web links
darknet websites the dark internet dark web websites
dark market 2024 darknet seiten darknet markets
dark web market urls darknet site dark web links
darknet site dark web link darknet markets 2024
deep web markets onion dark website tor marketplace
darkmarket url tor markets 2024 darknet sites
deep web drug markets darkmarket url darkmarket url
deep web drug store https://darknet-marketspro.com/ – dark web access dark market
dark market url blackweb official website darknet websites
https://canadapharm.shop/# canada pharmacy online
deep web drug url deep web drug url dark web marketplaces
dark websites the dark internet darknet markets 2024
onion dark website dark market url darknet market lists
dark markets 2024 https://alldarkwebmarkets.com/ – the dark internet deep web search
dark market 2024 blackweb official website dark market url
deep web drug markets darknet markets darkmarket link
dark market darkmarket dark market onion
darknet drugs darknet drug store tor market url
deep web links dark web link darkmarket link
free dark web dark markets 2024 darknet seiten
darknet websites darknet marketplace deep web drug url
dark web search engine dark net dark web site
darknet markets 2024 darknet drug links dark market onion
tor markets darkmarket link darknet drug links
dark web websites darkmarket link dark web markets
dark websites dark web search engine darknet websites
tor darknet dark net dark web drug marketplace
dark web site cryptomarkets darknet tor markets links
darknet markets onion deep web drug url darknet links
dark web link dark markets 2024 drug markets onion
dark market url darknet drug market darknet marketplace
black internet free dark web dark web market list
dark market list dark web market urls dark market
dark web search engine dark web access deep dark web
darkmarket list free dark web dark web markets
darkmarket deep web search darknet drugs
darknet site tor darknet dark web marketplaces
tor marketplace darknet marketplace darknet markets onion
dark web market darknet site how to get on dark web
dark web market links tor markets 2024 deep web drug links
darknet drug market dark web websites darknet drug links
dark net dark market link tor markets links
dark web market list tor markets links darknet marketplace
darknet marketplace https://alldarknetmarkets.com/ – dark web market dark market link
deep dark web dark website darknet drug store
dark web market darknet drugs dark web access
tor marketplace https://darkweb-storelist.com/ – darknet markets onion dark web market links
darknet drug store darkmarket link darknet drugs
darknet markets onion address darknet drug store drug markets dark web
darknet drug links dark web market dark web drug marketplace
darknet markets 2024 bitcoin dark web deep web markets
Greetings! Very useful advice within this post! It’s the little changes that will make the greatest changes.
Many thanks for sharing!
deep web links darknet drugs tor drug market
onion market deep web markets dark web site
dark web search engine darknet websites darknet markets onion
blackweb dark website tor markets
deep web links deep web search dark websites
tor darknet dark websites darkmarket list
deep web drug url drug markets onion onion market
deep web links dark markets 2024 dark markets
darknet links dark markets 2024 darknet drug store
darknet market list darknet markets 2024 darknet markets onion
darkmarket 2024 dark web marketplaces how to get on dark web
tor markets links dark websites onion dark website
tor drug market dark market link darknet markets 2024
black internet tor market url darknet seiten
dark web access dark web websites dark net
dark websites darknet marketplace darknet marketplace
deep web drug store dark web sites links tor marketplace
dark web market dark internet dark websites
dark market link deep web drug markets darknet links
best darknet markets dark websites darknet markets onion address
dark web links darkmarket 2024 dark web market
darknet markets links deep web drug markets darknet drug links
darknet market links darknet markets dark web websites
darknet markets url dark markets 2024 darkmarket link
tor drug market blackweb darkmarket
dark web markets dark web site darknet drug market
darkmarket 2024 tor markets 2024 deep web drug markets
tor darknet https://darknet-marketspro.com/ – darknet markets 2024 how to get on dark web
dark web drug marketplace darknet markets url blackweb
cryptomarkets darknet darknet drugs tor market links
dark web market links tor markets links tor darknet
dark markets darknet drugs dark web market urls
india pharmacy mail order: top 10 pharmacies in india – top online pharmacy india
best darknet markets https://alldarkwebmarkets.com/ – tor marketplace darkweb marketplace
darknet market lists tor market dark website
darknet search engine darknet drug store deep dark web
deep web drug markets deep web search darknet market links
free dark web dark web market urls dark market list
cryptomarkets darknet darkmarket list deep web drug links
deep web links darknet magazine tor market
darknet websites dark web search engine darknet drugs
darkmarket list darknet markets free dark web
darkmarket link darknet search engine darkmarket 2024
best darknet markets dark website darknet markets onion
deep web drug markets dark market list dark web markets
deep web links darknet marketplace deep web drug url
darknet site darknet sites darkmarket
tor darknet dark web market links darknet market list
deep web markets onion dark website darkmarket
tor dark web darknet markets onion address tor markets links
darknet websites darknet markets dark web links
darknet drug market dark market darknet drug store
darknet site darknet websites darknet drugs
drug markets dark web darknet markets onion address deep web links
dark market link darknet drug links dark market list
darknet site dark market list tor darknet
darknet links cryptomarkets darknet deep web links
tor markets 2024 darknet market lists bitcoin dark web
dark web sites links darknet market list darknet sites
tor marketplace tor marketplace dark web market urls
blackweb official website dark net deep web drug url
dark market onion dark website deep web drug links
dark websites https://darknet-marketspro.com/ – darknet market dark market url
deep web drug markets blackweb free dark web
darknet seiten tor markets links dark website
zithromax capsules: generic zithromax online paypal – zithromax 250 price
darknet market https://alldarkwebmarkets.com/ – dark market dark market onion
darkmarket link how to access dark web darknet site
dark web market dark web search engines darkmarket list
dark market link deep web markets dark net
blackweb official website darknet market list bitcoin dark web
dark web sites darknet markets onion darknet market lists
darknet links dark websites dark web market
tor darknet tor market links darknet markets onion address
darknet site the dark internet darkmarket 2024
darknet search engine dark market 2024 free dark web
darknet magazine dark web markets deep web markets
darkmarket tor markets 2024 darknet markets links
dark web market drug markets onion darknet market lists
darknet markets onion onion dark website darknet site
tor markets 2024 darknet markets onion dark market list
dark market black internet bitcoin dark web
dark markets deep web links darknet markets 2024
darknet websites darknet markets deep web links
blackweb official website darknet websites dark web marketplaces
deep web links free dark web tor market
tor market url dark market url dark markets 2024
dark markets 2024 dark market onion tor markets 2024
darknet drug links dark market onion blackweb official website
dark market list darkweb marketplace cryptomarkets darknet
the dark internet dark web links dark net
the dark internet darknet magazine darknet sites
dark web drug marketplace dark internet darknet drug links
darknet sites dark web link darknet markets links
darknet markets 2024 dark web link blackweb official website
dark web market urls free dark web dark web markets
dark markets 2024 dark markets darkmarket
darkmarket link https://darknet-marketspro.com/ – dark web drug marketplace tor markets 2024
tor markets 2024 deep web drug url dark web drug marketplace
darknet markets links deep web links darknet websites
the dark internet https://darkweb-storelist.com/ – blackweb best darknet markets
free dark web dark market 2024 dark market
dark market link dark markets 2024 darknet markets links
darknet magazine best darknet markets dark web search engines
deep web markets dark web search engine dark web websites
dark market 2024 dark websites onion dark website
darknet drug store tor drug market dark market link
deep web sites deep dark web dark market link
darkmarket 2024 dark web link darkmarket 2024
darknet drug links drug markets onion dark web access
https://cytotec.directory/# buy cytotec pills online cheap
dark web search engines darknet drug market dark market 2024
darkmarket dark website dark market
darknet markets 2024 how to access dark web tor darknet
darknet drug store darknet search engine darknet markets onion
dark web sites dark web market deep web drug url
dark website darknet drug store dark web sites
tor markets 2024 dark web market urls darknet seiten
deep web links darknet market links dark market url
darknet market darknet market onion market
deep web drug markets dark web site dark website
tor darknet darknet drug market dark market
deep web links tor drug market deep web drug store
blackweb tor dark web onion market
dark market tor markets 2024 onion market
dark web marketplaces deep web sites tor darknet
dark web market links free dark web darknet market list
deep web drug links darknet markets 2024 darknet magazine
dark website bitcoin dark web bitcoin dark web
darkmarket link dark web markets how to get on dark web
They always have the newest products on the market http://cytotec.directory/# buy cytotec over the counter
dark markets tor markets 2024 darknet search engine
tor marketplace darknet markets url dark web market
tor markets https://alldarknetmarkets.com/ – dark net bitcoin dark web
drug markets dark web dark web sites tor market links
dark web websites darkmarket 2024 dark market 2024
darknet drug links darknet drugs dark market list
tor markets https://darkweb-storelist.com/ – deep web drug links darknet market
deep web links how to get on dark web deep web drug store
darknet marketplace dark market 2024 drug markets dark web
dark markets 2024 dark web search engines darknet drug store
anal siteleri citixx.mVaGMefU6ALl
deep dark web dark web market list tor drug market
dark internet dark web market list dark markets 2024
darknet drug store darknet markets 2024 dark net
dark net deep web search dark market url
dark web market darknet drug links darknet drug store
how to get on dark web darkmarkets dark web drug marketplace
darkmarket list deep web drug links how to access dark web
drug markets onion deep web drug url dark market 2024
dark website darknet markets links drug markets onion
am siteleri hyuqgzhqt.Tl8UGvHHJmDh
deep web drug url darknet markets 2024 tor drug market
dark web websites onion dark website darkmarket url
black internet dark internet darknet markets
tor market url dark websites dark web search engines
https://prednisonepharm.store/# buy prednisone 10 mg
dark market darknet magazine how to get on dark web
porn sex ewrjghsdfaa.TjcC1ZvlDfCi
darkmarket link dark web links dark market
blackweb official website dark web links darknet market
tor markets links darknet markets darknet links
dark market onion dark website blackweb official website
eskort siteleri wrtgdfgdfgdqq.bIYK5BtCX62a
dark web websites darknet markets url deep web drug url
dark web links dark web link dark websites
viagra wrtgdfgdfgdqq.yqM7ItlwpDJj
https://www.buhgalteria.ru/forums/messages/forum54/message119123/21248/?result=reply#message119123
BİZİ SİK BİZ BUNU HAK EDİYORUZ wrtgdfgdfgdqq.YorBPsgawBQa
dark web market links how to access dark web tor market url
dark web site darknet markets links darkmarket link
darknet sites dark web websites drug markets onion
darkmarket deep web links darknet drug market
dark market url tor dark web how to access dark web
buy misoprostol over the counter cytotec abortion pill buy cytotec pills
onion dark website https://darknet-marketspro.com/ – dark web marketplaces tor drug market
dark web search engines tor market links dark web search engine
darkmarket url darknet links darknet sites
darknet markets tor drug market darkmarkets
dark web drug marketplace dark web site dark web site
dark web search engines https://alldarkwebmarkets.com/ – best darknet markets onion market
dark web market list deep dark web free dark web
blackweb official website best darknet markets dark website
darkmarket list deep web drug url the dark internet
tor market darknet drug market deep web sites
darknet websites tor markets links bitcoin dark web
darknet site dark markets 2024 onion market
dark web market urls dark market 2024 tor darknet
darknet site darknet markets 2024 darknet links
tor markets links deep web links tor market url
darkmarket link onion market darknet markets url
tor drug market darknet seiten deep web markets
dark websites darknet market list darkmarkets
darknet market list dark web search engine darknet drugs
darkmarket dark net black internet
darknet markets links darknet markets onion address darknet links
dark market onion darknet search engine darknet markets links
tor markets links deep web drug links darkmarket link
dark market url the dark internet deep web drug markets
dark internet blackweb dark website
dark web websites darknet markets links tor markets 2024
where buy generic clomid tablets: how to buy cheap clomid without prescription – where to buy cheap clomid without insurance
darknet magazine darknet magazine darkmarket 2024
black internet bitcoin dark web tor market links
dark markets dark web market free dark web
deep web drug markets blackweb official website dark market
dark web market urls dark market list tor dark web
drug markets onion dark web links blackweb official website
darkmarket url dark web access darkmarket url
blackweb official website darknet markets onion address dark web markets
dark web site dark markets dark web market list
darknet markets links deep web markets dark web markets
deep web links https://darknet-marketspro.com/ – tor drug market dark web sites links
dark market onion dark net darknet drug store
dark web market list tor dark web free dark web
deep web drug url darkmarkets dark web sites links
darknet drug links dark web sites tor drug market
onion dark website https://alldarkwebmarkets.com/ – tor market url tor marketplace
dark market 2024 darknet market list darknet markets url
darkmarkets darknet marketplace tor markets 2024
darkmarket link darkmarket deep dark web
darknet markets links dark web search engine darknet markets onion address
how to access dark web dark market 2024 dark net
dark web marketplaces deep web drug store dark market url
dark web market list deep web markets black internet
dark market link the dark internet darknet markets onion
darknet market links darknet market dark web sites links
dark market onion dark web market list darkmarkets
dark web sites links dark market 2024 darknet market lists
darknet markets 2024 drug markets onion dark web markets
tor market url tor markets 2024 onion market
dark web websites deep web sites best darknet markets
darknet drug market dark market url darknet websites
Delivering worldwide standards with every prescription https://zithromaxpharm.online/# how to get zithromax over the counter
dark net darkmarket link deep dark web
the dark internet darknet marketplace deep web drug links
dark internet tor markets 2024 dark markets 2024
deep web drug links dark net free dark web
onion market deep web drug url dark web sites
dark web market links deep web markets darkweb marketplace
free dark web darknet market lists darknet markets url
darknet drug store dark markets tor drug market
darkmarket 2024 deep web markets dark market
darknet markets url darknet market list dark web market urls
darknet markets url dark website darkmarket link
darkmarket darknet marketplace dark markets
dark websites https://darknet-marketspro.com/ – darknet drug links dark web market urls
dark market list dark internet darknet markets 2024
deep web markets darkmarket link dark web market list
deep web links darknet search engine dark web drug marketplace
blackweb darknet seiten dark websites
dark web drug marketplace darknet sites onion dark website
tor market links dark web search engines dark web sites links
darknet drug store https://alldarkwebmarkets.com/ – darkmarket link dark web market
dark market list darkmarkets deep web drug store
darknet drugs dark web sites darknet market list
darknet market lists dark web search engine darknet market list
the dark internet dark market 2024 darknet drug store
dark websites dark market list deep web drug store
best darknet markets drug markets dark web dark website
deep web links dark web link drug markets dark web
darknet markets onion dark market url darkweb marketplace
darknet markets url dark market onion dark web link
dark market dark web search engine dark markets
how to access dark web dark web markets darknet seiten
darknet drug store dark web search engines dark web access
dark web drug marketplace deep web markets dark web site
cryptomarkets darknet darknet markets onion deep web drug markets
http://nolvadex.pro/# tamoxifen skin changes
darknet magazine cryptomarkets darknet dark markets
drug markets dark web dark web market drug markets dark web
darkmarket 2024 darknet markets onion darknet market links
tor markets dark market link darknet market links
blackweb darknet markets url darknet market list
tor market deep web sites darknet drugs
darknet drug market dark web access darknet market links
darkmarket link darknet sites tor darknet
tor market url how to get on dark web dark web sites
dark web site dark markets 2024 tor markets
darknet sites dark web market urls dark web markets
deep web links darknet market lists dark markets
dark website dark web market urls blackweb official website
darknet market list https://alldarknetmarkets.com/ – dark market onion dark web market urls
dark net dark market onion darknet market
deep web drug markets dark web links darknet websites
tor marketplace dark market onion dark market 2024
drug markets onion black internet tor darknet
dark web access https://alldarkwebmarkets.com/ – darknet sites dark web marketplaces
tor markets links deep web sites darknet search engine
https://zaimy-na-kartu-tinkoff.ru/
dark web sites free dark web deep web drug links
darkmarket dark web search engines darknet sites
how to access dark web darkmarkets blackweb official website
dark market list darknet markets links tor markets 2024
dark internet darknet markets blackweb
darknet markets links deep web sites tor dark web
dark web site dark market url dark internet
dark web drug marketplace darknet markets tor markets 2024
dark web market free dark web onion dark website
darknet markets onion darknet markets links darkweb marketplace
how to get on dark web darknet websites tor drug market
deep web drug url dark web market urls darknet sites
dark web search engine darknet market dark internet
darknet markets onion address darknet seiten darknet drug links
darkmarket link darknet market lists dark web marketplaces
dark market onion deep web drug store darknet markets links
darknet market lists darknet sites darknet markets links
blackweb dark web market links darkmarket list
tor markets darknet drug store dark web link
onion dark website darknet site drug markets onion
dark web markets darknet drug store blackweb official website
cryptomarkets darknet tor market darkmarket link
dark market list darknet marketplace darknet drug market
dark websites tor marketplace tor marketplace
darknet drugs dark market list dark market url
dark web access tor market darkweb marketplace
tor market url https://alldarknetmarkets.com/ – darknet drug links tor dark web
deep web links dark web sites darknet market
deep web markets dark web links darkmarket url
deep web drug url https://alldarkwebmarkets.com/ – darknet site how to access dark web
darknet markets onion tor drug market drug markets onion
darkmarkets tor marketplace darkmarket
Speedy service with a smile https://prednisonepharm.store/# prednisone tablets canada
dark market onion dark web search engines darkmarket list
dark web site tor markets deep dark web
dark markets darkmarket url darknet drug links
dark web access darknet markets onion address darknet seiten
black internet darkweb marketplace darknet drug market
dark web access darkmarkets darknet seiten
where to get cheap clomid prices: can you get cheap clomid – where can i buy cheap clomid without a prescription
dark web search engine darknet market list dark web market links
dark market deep web drug markets dark market link
dark markets 2024 deep web links darknet market links
best darknet markets blackweb darknet market
darkmarkets deep web drug markets darknet drug store
dark web link darknet market free dark web
dark web websites cryptomarkets darknet dark web link
onion dark website darknet markets url cryptomarkets darknet
tor markets links how to access dark web darkmarkets
cryptomarkets darknet dark web search engine darknet search engine
darknet markets tor dark web drug markets dark web
darkmarket link darknet magazine onion dark website
dark web markets dark web sites links tor markets
darknet markets 2024 darknet drugs deep dark web
darknet sites dark web market links darknet markets onion address
dark web sites bitcoin dark web dark web search engine
darknet market darknet market lists darkmarket list
tor marketplace the dark internet how to access dark web
dark market list darkmarkets deep web links
tor markets dark net deep web links
darknet market links https://darknet-marketspro.com/ – darknet drug links deep web search
tor market links darkmarket url deep web drug store
dark market url dark web site dark market url
darknet markets 2024 https://alldarkwebmarkets.com/ – dark web search engine tor market
dark market 2024 darknet site tor markets links
dark market list deep web drug links deep web links
dark net darknet marketplace deep web drug links
dark web link dark internet darknet markets
darknet marketplace dark market dark web sites links
darknet markets links drug markets dark web tor dark web
darkmarket link drug markets dark web deep web drug store
darknet markets links darknet site darknet markets links
darkmarket url tor market darknet links
darknet market lists dark web markets blackweb
tor market links darknet drug links darknet sites
darkmarket link the dark internet dark web market links
dark web market dark web marketplaces dark websites
deep web links how to get on dark web darknet sites
http://cytotec.directory/# buy cytotec pills
dark web sites darkweb marketplace dark website
darknet drug store dark web market urls darkmarket
dark web link drug markets onion dark web market urls
dark web sites tor darknet dark website
tor dark web darknet markets onion deep web drug store
tor marketplace tor market url darknet marketplace
tor market url deep dark web tor drug market
dark web site dark web access darknet markets onion
black internet cryptomarkets darknet darknet market
deep web sites darknet markets onion market
dark market onion market dark markets
dark web market list https://alldarknetmarkets.com/ – darkmarket darkmarket list
darknet site darknet websites dark net
darkmarket list dark web site dark web drug marketplace
onion market https://alldarkwebmarkets.com/ – blackweb official website darknet markets onion
cryptomarkets darknet onion market deep dark web
dark markets 2024 dark web site tor markets links
darknet markets onion address deep web drug store dark market url
dark web links blackweb official website deep web search
deep web markets tor dark web onion dark website
deep web links darknet websites darknet magazine
darknet drug links dark market list cryptomarkets darknet
darknet markets onion how to access dark web deep web drug links
deep web sites deep web drug store darkmarket
darknet markets dark market tor marketplace
darknet search engine dark market onion dark market link
deep web markets dark web search engine how to get on dark web
dark web marketplaces dark web search engines darknet marketplace
dark net darknet markets url deep web links
darkmarket cryptomarkets darknet onion dark website
darknet site tor darknet darknet site
https://zithromaxpharm.online/# buy azithromycin zithromax
dark web search engines deep web search darknet market
dark web market darknet markets dark web sites
best darknet markets deep web sites dark market
darknet site dark web drug marketplace darknet drug store
dark web drug marketplace dark market list dark web drug marketplace
best darknet markets darknet markets onion address darkmarket link
darknet drug store dark web marketplaces dark web site
darknet sites cryptomarkets darknet darknet sites
darknet market dark web market list how to get on dark web
dark web market list darknet seiten blackweb official website
Their commitment to global patient welfare is commendable https://zithromaxpharm.online/# how to get zithromax
dark markets deep web markets blackweb
darkmarket https://alldarknetmarkets.com/ – darkmarket list deep web drug markets
dark web market darknet drugs darknet markets
darknet drugs dark web market list dark web market list
dark web websites https://darkweb-storelist.com/ – dark web markets dark markets
dark internet dark market onion dark market url
tor dark web darknet drug market dark internet
deep web drug url dark web websites darknet drugs
dark market tor market darknet drug market
onion market deep web drug url darknet drugs
darknet market links tor market url best darknet markets
darknet marketplace deep web drug markets deep web search
deep web drug store deep web drug links tor drug market
dark market onion dark web market darknet search engine
onion market dark website darkmarket url
dark web marketplaces deep web drug store darknet drug market
deep dark web bitcoin dark web onion dark website
cryptomarkets darknet darknet site darknet market links
dark web websites darknet websites tor market url
darkmarket 2024 tor market deep web drug store
tor market links darknet sites how to get on dark web
deep web drug links tor darknet dark web site
darknet drug store dark web market darknet websites
dark markets dark web search engines dark market 2024
darknet markets dark internet dark web link
deep web sites deep web links cryptomarkets darknet
dark web market links blackweb official website free dark web
darknet markets onion deep web sites deep web sites
deep web drug links darknet drug market blackweb
blackweb deep web links darknet markets
dark web market list deep web drug markets deep dark web
tamoxifen rash: tamoxifen rash – nolvadex for sale amazon
darknet markets links https://alldarknetmarkets.com/ – tor market links the dark internet
deep web links dark web market links dark markets 2024
darknet markets onion darknet market dark markets 2024
how to get on dark web https://darkweb-storelist.com/ – deep web search best darknet markets
dark web sites dark web drug marketplace dark net
buy tamoxifen what is tamoxifen used for tamoxifen for breast cancer prevention
dark websites the dark internet onion dark website
deep web search darknet market list dark market
dark web market urls dark web link dark markets 2024
blackweb darknet market links darkweb marketplace
darknet sites darknet markets onion address deep web drug markets
dark market onion market dark web marketplaces
darkmarket url dark web access darknet drug market
deep web drug url cryptomarkets darknet darkmarket 2024
the dark internet deep web drug url how to get on dark web
darkmarkets dark web sites links darknet markets links
the dark internet dark market black internet
dark web search engines how to get on dark web dark web market urls
drug markets onion deep web drug markets darknet links
dark web markets deep web drug store best darknet markets
dark market darknet marketplace tor markets
best darknet markets dark web site darknet markets
darknet markets onion dark websites dark web search engine
dark web market links deep web sites darkmarket url
dark web market darknet search engine blackweb official website
best darknet markets dark web access dark web market list
tor market darknet markets url darknet market links
dark web search engine dark market link dark web search engines
https://cytotec.directory/# cytotec online
deep web sites darkmarket 2024 dark web drug marketplace
darkmarket link drug markets dark web cryptomarkets darknet
darknet markets onion address https://alldarknetmarkets.com/ – deep web drug links dark markets
tor dark web bitcoin dark web tor markets links
dark web link darknet markets links deep dark web
deep web links https://darkweb-storelist.com/ – darknet websites dark web markets
best darknet markets darknet market darknet drugs
deep web drug links dark web sites darknet search engine
darkmarket url onion dark website darknet market list
free dark web onion dark website darkmarket list
dark market url black internet darkweb marketplace
tor markets links dark internet dark web websites
dark web sites darkmarket list tor market links
darknet markets 2024 best darknet markets tor marketplace
blackweb dark web sites links darknet drug store
darknet seiten dark web websites dark internet
dark internet dark market 2024 darknet market list
darknet markets 2024 darknet markets tor markets
Their global outlook is evident in their expansive services http://clomidpharm.shop/# where to buy cheap clomid
free dark web blackweb darknet seiten
dark web site darknet sites darknet markets url
dark web market links dark web market dark web sites
darknet seiten tor marketplace darknet market lists
tor marketplace dark web link dark markets
blackweb deep web markets free dark web
tor markets 2024 darknet marketplace deep web search
darknet markets onion address dark web market links dark market url
deep dark web dark market 2024 darknet drugs
dark web market urls dark web links dark market url
deep web links dark web markets darknet drug links
free dark web dark web link dark markets 2024
darkmarket list dark web access darknet markets
darknet magazine https://alldarknetmarkets.com/ – darkweb marketplace darkmarket url
darknet drug store darknet market links dark web search engine
deep web drug markets darkmarket link how to access dark web
dark market https://darkweb-storelist.com/ – tor market darknet seiten
dark web drug marketplace dark web access darknet markets links
deep web drug store dark market list deep web drug url
cryptomarkets darknet dark web site tor markets links
dark web market list darknet drug store darknet drug market
darknet markets 2024 cryptomarkets darknet tor dark web
darknet drug store black internet darknet drug store
dark web sites tor markets dark web links
darknet markets onion how to get on dark web dark web search engine
darknet market links blackweb official website dark markets 2024
darknet drugs onion dark website dark market
dark web search engines free dark web tor markets links
darkmarket link darknet drug market drug markets onion
darknet drug links drug markets onion blackweb
dark web market urls tor market url darknet markets links
dark markets bitcoin dark web dark web sites
darknet markets black internet tor market
dark web market darknet drug links dark market url
dark web sites deep web drug markets darknet links
dark web sites links darknet markets links darkmarket list
drug markets onion deep web drug markets dark market
deep web drug store dark web drug marketplace cryptomarkets darknet
darknet links dark market onion darknet drug links
darknet drug store tor dark web tor markets
deep web drug url dark web drug marketplace deep web links
darknet markets darkmarkets deep web links
darknet markets 2024 tor marketplace deep dark web
dark market list dark market url darkmarkets
dark web websites darknet market darknet drug links
black internet best darknet markets darknet markets 2024
dark web market list drug markets dark web dark market
dark web market links https://darknet-marketspro.com/ – dark web market drug markets onion
prednisone cream over the counter: prednisone 10mg tabs – medicine prednisone 5mg
dark web markets tor dark web darknet market list
darknet market links how to get on dark web bitcoin dark web
darkmarket url black internet deep web search
Szpiegowskie telefonu – Ukryta aplikacja śledząca, która rejestruje lokalizację, SMS-y, dźwięk rozmów, WhatsApp, Facebook, zdjęcie, kamerę, aktywność w Internecie. Najlepsze do kontroli rodzicielskiej i monitorowania pracowników. Szpiegowskie Telefonu za Darmo – Oprogramowanie Monitorujące Online.
sektor benim zaten amin evladi pompadirha.n5YdwEZ57456
bahis siteleri child porn asillartaklitler.tfQ3W5ZdIM0L
seksi siteler hephupx.Uq9hpRXhHuOa
anal siteleri hepxhupx.8iLtx318eGRK
am siteleri juljulfbi.tYnouPMGomEC
porno izle bjluajszz.xn5dPc6UCASD
amciik siteleri bxjluajsxzz.JroWH5w1VuaL
house porn 0qbxjluaxcxjsxzz.x2DEpBoPTMKK
Thank you for your sharing. I am worried that I lack creative ideas. It is your article that makes me full of hope. Thank you. But, I have a question, can you help me? https://www.binance.info/bg/join?ref=IJFGOAID
Najlepsza aplikacja do kontroli rodzicielskiej, aby chronić swoje dzieci – potajemnie tajny monitor GPS, SMS-y, połączenia, WhatsApp, Facebook, lokalizacja. Możesz zdalnie monitorować aktywność telefonu komórkowego po pobraniu i zainstalowaniu apk na telefonie docelowym.
Thanks for sharing. I read many of your blog posts, cool, your blog is very good. https://www.binance.info/join?ref=OMM3XK51
Your article helped me a lot, is there any more related content? Thanks! https://www.binance.info/it/join?ref=53551167
Can you be more specific about the content of your article? After reading it, I still have some doubts. Hope you can help me. https://www.binance.com/lv/register?ref=V3MG69RO
Your point of view caught my eye and was very interesting. Thanks. I have a question for you. https://accounts.binance.com/it/register?ref=JHQQKNKN
Your article helped me a lot, is there any more related content? Thanks! https://www.binance.com/zh-TC/join?ref=GJY4VW8W
bahis siteleri incest category pokkerx.jAVbMgSuD4Rl
bahis siteleri porn sex incest footballxx.weWXZZeTliBy
watch porn video mobileidn.EMtdHzgqwy3m
anal sikis siteleri bingoxx.Tutd8M1wRm8k
seksi siteler 250tldenemebonusuxx.qizoTbcBmxXI
bahis siteleri porn eyeconartxx.5pUNMOecelDz
Thank you for your sharing. I am worried that I lack creative ideas. It is your article that makes me full of hope. Thank you. But, I have a question, can you help me? https://accounts.binance.com/lv/register?ref=VDVEQ78S
porn vvsetohimalxxvc.uIBcqHH1hGL2
Can you be more specific about the content of your article? After reading it, I still have some doubts. Hope you can help me. https://www.binance.info/tr/join?ref=WTOZ531Y
porn siteleri tthighereduhryyy.4EYF0RBCAFl
Sitedeki indirimler gerçekten cazip, her zaman buradan alışveriş yapmayı tercih ediyorum.
Müşteri hizmetleriyle iletişime geçtiğimde çok yardımcı oldular, teşekkür ederim.
Thank you for your sharing. I am worried that I lack creative ideas. It is your article that makes me full of hope. Thank you. But, I have a question, can you help me?
Thanks for sharing. I read many of your blog posts, cool, your blog is very good.
download porn videos 4k gghkyogg.XG7MHQeDWWg
hd porn 4k ggjennifegg.Ffs4sAuDawe
porn video in 4k ggjinnysflogg.FDhDSf2wIhD
Uși termopan moderne și elegante te așteaptă pe http://www.ferestremd.com!
Jaluzele moderne și elegante care îți completează perfect ferestrele, găsești pe http://www.ferestremd.com!
Your point of view caught my eye and was very interesting. Thanks. I have a question for you.
Bir Gastronize bardak yıkama sever olarak bu güzel bilgilendirmeler için teşekkür ederim.
Your posts are always so well-researched and informative I appreciate how thorough and detailed your content is
Thanks for sharing. I read many of your blog posts, cool, your blog is very good.
Your positivity and enthusiasm are infectious It’s clear that you are truly passionate about what you do and it’s inspiring to see
Emeğinize sağlık, Joseph Campbell hakkındaki bilgilendirmeler için teşekkür ederim.
Thanks for sharing. I read many of your blog posts, cool, your blog is very good.
I just like the helpful information you provide in your articles
köpek oteli satın alma konusunda bu kadar net bilgiler internette maalesef yok bu yüzden çok iyi ve başarılı olmuş teşekkürler.
It’s great to hear such positive feedback from you. We’re eager to showcase this exceptional post on our site.
Your point of view caught my eye and was very interesting. Thanks. I have a question for you.
çok bilgilendirici bir yazı olmuş ellerinize sağlık teşekkür ederim
I like the efforts you have put in this, regards for all the great content.
sitenizi takip ediyorum makaleler Faydalı bilgiler için teşekkürler, Sao Paulo’yı ve Arif Pala’yı asla bırakmam.
I don’t think the title of your article matches the content lol. Just kidding, mainly because I had some doubts after reading the article.
This blog has opened my eyes to new ideas and perspectives that I may not have considered before Thank you for broadening my horizons
I really like reading through a post that can make men and women think. Also, thank you for allowing me to comment!
Good post! We will be linking to this particularly great post on our site. Keep up the great writing
fashionflag porn videos 4k download fashionflag.NBMyfBLhqZE
There is definately a lot to find out about this subject. I like all the points you made
goodhere Cuckold porn vurucutewet.z8cQPrOffMA
ladyandtherose Granny porn backlinkseox.ErUDpd68mni
jenniferroy 集団セックス japanesexxporns.GTdeIKhhSK4
Great information shared.. really enjoyed reading this post thank you author for sharing this post .. appreciated
landuse Cuckold porn lancdcuse.bCY1CXgYuOK
Hi there to all, for the reason that I am genuinely keen of reading this website’s post about olive oil polyphenol to be updated on a regular basis, it carries pleasant stuff.
falbobrospizzamadison Gays porn jkkıjxxx.rl230TQkTws
सेलिब्रिटी अश्लील qqyyooppxx.C8H3WijvTX0
नानी के पोर्न के बा hjkvbasdfzxzz.Avht5Yu46PF
I am truly thankful to the owner of this web site who has shared this fantastic piece of writing about olive oil for hair at this place.
Can you be more specific about the content of your article? After reading it, I still have some doubts. Hope you can help me.
Bilgiler için teşekkür ederim, latte macchiato hakkında işime son derece yaradı.
किशोर अश्लीलता txechdyzxca.swqVbtYvTNb
I appreciate you sharing this blog post about olive oil gluten free, thanks again, cool.
Güzel aydınlatıcı makale için teşekkürler, americano hakkında daha iyisi şamda kayısı, umarım faydalı çalışmalarınızın devamı gelir.
रूसी अश्लील साहित्य hkyonet.0yRnd2u5mYb
I am truly thankful to the owner of this web site who has shared this fantastic piece of writing at at this place.
Konular mükemmel olduğu gibi site teması da içeriğe müthiş uyum sağlamış, iyi ki cappuccino var, tebrikler.
milf ਪੋਰਨ madisonivysex.OvP0GOFyh5i
Yerden ısıtma, geleneksel radyatörlerin aksine daha temiz ve sessiz bir ısıtma yöntemi sunar. Ayrıca, zeminin yüzeyini ısıtarak toz ve alerjen birikimini azaltabilir, böylece daha sağlıklı bir iç mekan ortamı oluşturabilir. Yerden ısıtma sistemleri, modern bina tasarımlarında ve yenileme projelerinde giderek daha popüler hale gelmektedir. Yerden Isıtma Yerden Isıtma
Güzel aydınlatıcı makale için teşekkürler daha iyisi samda kayısı umarım faydalı çalışmalarınızın devamı gelir.
ladesbet ਮਿਸ਼ਨਰੀ ਸ਼ੈਲੀ ਪੋਰਨ ladesinemi.ZPsT2b8wwvd
ladesbet 女の子の自慰行為ポルノ ladestinemi.Gb1DIMTphph
Nice post. I learn something totally new and challenging on websites
I don’t think the title of your article matches the content lol. Just kidding, mainly because I had some doubts after reading the article.
Good post! We will be linking to this particularly great post on our site. Keep up the great writing
Your blog has helped me through some tough times and I am so grateful for your wise words and positive outlook
Your writing style is so engaging and easy to follow I find myself reading through each post without even realizing I’ve reached the end
4k IPTV service: Crystal clear, lifelike images.
Thanks for sharing. I read many of your blog posts, cool, your blog is very good.
Your writing is so inspiring and motivating I always leave your blog feeling more determined and resilient
You’re so awesome! I don’t believe I have read a single thing like that before. So great to find someone with some original thoughts on this topic. Really.. thank you for starting this up. This website is something that is needed on the internet, someone with a little originality!
GuinchoSorocaba
Your positivity and optimism are contagious It’s impossible to read your blog without feeling uplifted and inspired Keep up the amazing work
Your latest blog post was truly inspiring and had some great insights. I can’t wait to see what else you have in store.
Keep up the amazing work!
Your posts are always so well-researched and informative I appreciate how thorough and detailed your content is
I have been struggling with this issue for a while and your post has provided me with much-needed guidance and clarity Thank you so much
site sorocaba
Daha önce araştırıp pek Türkçe kaynak bulamadığım sorundu Elinize sağlık eminim arayan çok kişi vardır.
Hocam detaylı bir anlatım olmuş, web tasarım nasıl çıkmış iyice öğrendim, eline sağlık.
Your words have a way of touching hearts and inspiring minds Thank you for using your platform to spread love and positivity
Osmanoğlu İnşaatosmanoğlu inşaat Osmanoğlu İnşaat
gerçekten güzel bir yazı olmuş. Yanlış bildiğimiz bir çok konu varmış. Teşekkürler.
Your point of view caught my eye and was very interesting. Thanks. I have a question for you.
Your article helped me a lot, is there any more related content? Thanks!
Your writing is so eloquent and engaging You have a gift for connecting with your readers and making us feel understood
Your posts are so thought-provoking and often leave me pondering long after I have finished reading Keep challenging your readers to think outside the box
Thank you for the amazing blog post!
Thanks for sharing. I read many of your blog posts, cool, your blog is very good.
I love how this blog celebrates diversity and inclusivity It’s a reminder that we are all unique and should embrace our differences
Thank you for creating such valuable content. Your hard work and dedication are appreciated by so many.
Your blog has become my go-to source for positive and uplifting content Thank you for consistently delivering high-quality posts
Your posts always leave me feeling motivated and empowered You have a gift for inspiring others and it’s evident in your writing
glutensiz poğaça tarifi
I’m often to blogging and i really appreciate your content. The article has actually peaks my interest. I’m going to bookmark your web site and maintain checking for brand spanking new information.
ağlayan kek Tarifi
lazer kesim saç modelleri
Alinazik Tarifi
pankek tarifi
Bu güzel bilgilendirmeler için teşekkür ederim.
Loving the flexibility of IPTV Premium’s subscription plans. I can choose the plan that best fits my budget and needs!
Your point of view caught my eye and was very interesting. Thanks. I have a question for you.
Your article helped me a lot, is there any more related content? Thanks!
I just like the helpful information you provide in your articles
I very delighted to find this internet site on bing, just what I was searching for as well saved to fav
This is really interesting, You’re a very skilled blogger. I’ve joined your feed and look forward to seeking more of your magnificent post. Also, I’ve shared your site in my social networks!
Marketing Digital em Sorocaba: Impulsione Sua Marca Local
Hi there to all, for the reason that I am genuinely keen of reading this website’s post to be updated on a regular basis. It carries pleasant stuff.
Pretty! This has been a really wonderful post. Many thanks for providing these details.
Çok işime yaradı bende bunu nasıl yapacağımı araştırıyorum. Paylaşım için teşekkür ederim.
Very well presented. Every quote was awesome and thanks for sharing the content. Keep sharing and keep motivating others.
Yerli porno izle, Türk seks izle, Sex izle, Porno izle
IPTV OnePlus: the best IPTV provider UK has!
I recently went on a custom-built tour with ArcticSafari.is and it was an unforgettable experience. We spent the day enjoying the midnight sun, and our guide was incredibly knowledgeable and friendly. I highly recommend ArcticSafari.is for anyone looking to make the most of their time in Iceland.
I recently went on a countryside tour with ArcticSafari.is and it was an unforgettable experience. We spent the day exploring the stunning landscapes, and our guide was incredibly knowledgeable and friendly. I highly recommend ArcticSafari.is for anyone looking to make the most of their time in Iceland.
アナルポルノ .5WMP9PAvTPY
Discover the tranquil oasis of Hotel Breiðdalsvík, surrounded by the rugged beauty of Iceland’s East Fjords. Breiðdalsá River: Renowned for excellent trout and salmon fishing in the beautiful Breiðdalur Valley. Experience genuine small-town hospitality and fresh regional cuisine at breiddalsvik.is.
Discover the tranquil oasis of Hotel Breiðdalsvík, surrounded by the rugged beauty of Iceland’s East Fjords. Heydalakirkja Church: A picturesque church with historical significance, rebuilt in 1975. Experience genuine small-town hospitality and fresh regional cuisine at breiddalsvik.is.
Discover the tranquil oasis of Hotel Breiðdalsvík, surrounded by the rugged beauty of Iceland’s East Fjords. Heydalakirkja Church: A picturesque church with historical significance, rebuilt in 1975. Experience genuine small-town hospitality and fresh regional cuisine at breiddalsvik.is.
Discover the tranquil oasis of Hotel Breiðdalsvík, surrounded by the rugged beauty of Iceland’s East Fjords. Meleyri Beach: A charming black sand beach perfect for a relaxing stroll and birdwatching. Experience genuine small-town hospitality and fresh regional cuisine at breiddalsvik.is.
Discover the tranquil oasis of Hotel Breiðdalsvík, surrounded by the rugged beauty of Iceland’s East Fjords. Breiðdalsá River: Renowned for excellent trout and salmon fishing in the beautiful Breiðdalur Valley. Experience genuine small-town hospitality and fresh regional cuisine at breiddalsvik.is.
Discover the tranquil oasis of Hotel Breiðdalsvík, surrounded by the rugged beauty of Iceland’s East Fjords. Breiðdalsheiði Volcano: An ancient volcano with stunning views, ideal for adventurous hikes. Experience genuine small-town hospitality and fresh regional cuisine at breiddalsvik.is.
I’m often to blogging and i really appreciate your content. The article has actually peaks my interest. I’m going to bookmark your web site and maintain checking for brand spanking new information.
websitem için çok işime yaradı teşekkür ederim
Endüstriyel tesislerde güvenli ve verimli muayene hizmetleri için MapperX’i tercih edin. Daha fazla bilgi için: MapperX.
MapperX, kapsamlı denetim ve muayene hizmetleri ile enerji sektöründe öne çıkıyor. Ayrıntılar için: MapperX.
Termografik muayene konusunda lider MapperX, GES santral bakımında en iyi hizmeti sunuyor. Daha fazla bilgi için: Termografik Muayene.
I am truly thankful to the owner of this web site who has shared this fantastic piece of writing at at this place.
Drone destekli termal inceleme hizmetleriyle GES santrallerinizin bakımını hızlandırın: Denetim ve Muayene.
Termal inceleme ile enerji verimliliğinizi en üst seviyeye çıkarın. Daha fazla bilgi için: MapperX.
Drone destekli termal inceleme ile GES santral bakımınızı hızlandırın. Detaylı bilgi için: Denetim ve Muayene.
Hatay’daki inşaat projelerinizde dayanıklı ve kaliteli kereste ürünleri arıyorsanız, kereste.com.tr‘de ihtiyaçlarınıza uygun çözümler bulabilirsiniz.
I really like reading through a post that can make men and women think. Also, thank you for allowing me to comment!
I am truly thankful to the owner of this web site who has shared this fantastic piece of writing at at this place.
I just like the helpful information you provide in your articles
Antakya’da mobilya yapımında kullanabileceğiniz kaliteli ahşap ürünleri kereste.com.tr‘de bulabilirsiniz. Geniş ürün yelpazesi sizi bekliyor.
There is definately a lot to find out about this subject. I like all the points you made
Çeşitli kereste gruplarıyla Hatay’daki projelerinizi zenginleştirmek istiyorsanız, kereste.com.tr‘de sunulan ürünleri inceleyerek ihtiyacınıza uygun çözümleri bulabilirsiniz.
Can you be more specific about the content of your article? After reading it, I still have some doubts. Hope you can help me.
Pretty! This has been a really wonderful post. Many thanks for providing these details.
Termografik muayene ile enerji kaybını en aza indirmek için MapperX’i tercih edin: MapperX.
Termografik muayene hizmetleri ile enerji kayıplarını önlemek için MapperX’i tercih edin. Ayrıntılar için: MapperX.
Termal inceleme ile enerji verimliliğinizi artırmak için MapperX’i tercih edin. Daha fazla bilgiye buradan ulaşabilirsiniz: MapperX.
Your point of view caught my eye and was very interesting. Thanks. I have a question for you.
Your article helped me a lot, is there any more related content? Thanks!
Your point of view caught my eye and was very interesting. Thanks. I have a question for you.
En Yakın Elektrikçi , İstanbul Elektrikçi
I don’t think the title of your article matches the content lol. Just kidding, mainly because I had some doubts after reading the article.
bahçelievler elektrikçi
aramalarım sonunda buraya geldim ve kesinlikle işime yarayan bir makale oldu. teşekkür ederim
Your article helped me a lot, is there any more related content? Thanks!
Can you be more specific about the content of your article? After reading it, I still have some doubts. Hope you can help me.
Your point of view caught my eye and was very interesting. Thanks. I have a question for you.
GplPixel – Free Download Best of Premium WordPress, WooCommerce,PHP, Shopify, Website Templates, Envato market,Download Free Nulled, WP nulled,free plugins,ThemeForest
Aile hukuku ile ilgili her türlü hukuki desteği Ankara boşanma avukatı Ahmet Erenoğlu’ndan alabilirsiniz. Uzman ekibi ile hizmet vermektedir.
Boşanma davalarınızda profesyonel bir avukat arıyorsanız, Ankara boşanma avukatı Ahmet Erenoğlu’na başvurabilirsiniz. Hukuki süreçte size rehberlik edecektir.
I don’t think the title of your article matches the content lol. Just kidding, mainly because I had some doubts after reading the article.
Your point of view caught my eye and was very interesting. Thanks. I have a question for you.
Emeğinize sağlık, bilgilendirmeler için teşekkür ederim.
Thank you for your sharing. I am worried that I lack creative ideas. It is your article that makes me full of hope. Thank you. But, I have a question, can you help me?
Estetica dentara este o ramura a stomatologiei al carei principal scop este de a corecta defectele danturii pacientilor. La cabinetul nostru, aceasta procedura se realizeaza numai cu tehnologii de ultima generatie oferind astfel calitatea lucrarii efectuate. Apeland la serviciile noastre de estetica dentara (coroane dentare, fatete dentare, implanturi dentare) veti dobandi un zambet incantator, invidiat de toti cei din jur.
Thanks for sharing. I read many of your blog posts, cool, your blog is very good.
For the reason that the admin of this site is working, no uncertainty very quickly it will be renowned, due to its quality contents about extra virgin olive oil EVOO.
Good post! We will be linking to this particularly great post of smoke point of olive oil on our site, keep up the great writing.
Thank you very much for sharing, I learned a lot from your article. Very cool. Thanks.
Great information shared.. really enjoyed reading this post of Hollywood Smile, thank you author for sharing this post, appreciated.
https://www.heritagefamilypantry.com/OvlnJuticq8
Naturally like your Liberica Coffee web site however you need to take a look at the spelling on several of your posts, a number of them are rife with spelling problems and I find it very bothersome to tell the truth on the other hand I will surely come again again.
https://betovis34.net/ F6iRStPjftB
I don’t think the title of your article matches the content lol. Just kidding, mainly because I had some doubts after reading the article.
QKfZBaz87Ao
I just like the helpful information you provide in your articles
mdheON5BkTq
Your point of view caught my eye and was very interesting. Thanks. I have a question for you.
Her gün makyaj yapan biri olarak micellar temizleme suyu hayatımı kurtardı, cildim yumuşacık oluyor.
Nazik temizleyici köpük cildimi tahriş etmeden temizliyor, hassas ciltler için mükemmel bir ürün.
Nice post. I learn something totally new and challenging on websites
I just like the helpful information you provide in your articles
The key to getting the most out of a solar energy system is consistent solar inspections, and MapperX offers some of the best services available.
naturally like your web site however you need to take a look at the spelling on several of your posts. A number of them are rife with spelling problems and I find it very bothersome to tell the truth on the other hand I will surely come again again.
Perpa Kameram kamera fiyatları, kamera sistemleri, perpakameram, perpa kamera, istanbul kamera fiyatları uygun fiyatlar için iletişime geçin
Eser Sertifika | Online Sertifika programı sertifika fiyatı, eser sertifika, sertifika, adalet sertifikası, çocuk sertifika, esnaf sertifika, mobilya sertifika başvuru için iletişime geçiniz.
çınar haberleri, çınar gündem, çınar olay, çınar ilçe haberleri, Diyarbakır haberleri
Aydın haberleri tarafsız haber yayıncılık aydın, aydın haber, aydın haberleri En doğru ve En tarafsız haber sayfanız
En Uygun Kumanda Modelleri | Kumanda Sepeti <a href=" https://www.kumandasepeti.com/ kumanda, kumanda modelleri, tv kumandası fiyat, kumanda fiyatı, tv tamiri,adaptörler,led tv fiyatları,televizyon ekran tamiri,tv led değişimi,tv ekran fiyatları,lg tv ekran fiyatları,grundig kumanda,axen televizyon kumandası,televizyon panel,televizyon led,samsung led tv led,panel arızası tamiri,lg lcd led,tv let fiyatlari,tv paneli Kredi kartına taksit fırası sizlerle.
Diyarbakır Haberleri tarafsız haber yayıncılığı anlayışıyla doğru ve güvenilir bilgilere ulaşmanızı sağlar Diyarbakır Olay, Diyarbakır Gündem, Diyarbakır Haber, Diyarbakır haberleri, Gündem haberleri, Diyarbakır bismil haber, Diyarbakır çınar gündem, diyarbakır ergani
Regular solar inspections are essential for solar farm operators, and MapperX provides a quality service to meet this need.
promosyon powerbank,promosyon termoslar,promosyon matara,promosyon ajanda,promosyon defterler,promosyon takvim
Your article helped me a lot, is there any more related content? Thanks!
From start to finish, your content is simply amazing. You have a talent for making complex topics easy to understand and I always come away with valuable insights.
Nur Medikal GiyimHemşire forması, cerrahi bone, doktor kıyafeti, hemşire kıyafeti, desenli formalar, sabo terlik, hastane terlikleri, airmax sabo terlik, ortopedik terlik, tesettür hemşire forması
Bediroğlu Hırdavat | Mahmut Kurt şanlıurfa Bediroğlu urfa stihl, Şanlıurfa stihl bayi, Şanlıurfa husqvarna bayi, güneydoğu felco bayi, Şanlıurfa taral bayisi, motorlu testere yedek parça,Şanlıurfa Stihl Bayi, benzinli testere yedek parça, testere zinciri, ağaç kesme pala, klavuz, elektronik bobin, hava filtresi, stihl Şanlıurfa bayi, stihl Şanlıurfa, Şanlıurfa stihl, stihl servisi, Şanlıurfa stihl servis
Aydın haberleri tarafsız haber yayıncılık aydın, aydın haber, aydın haberleri En doğru ve En tarafsız haber sayfanız
Van Haberleri tarafsız haber yayıncılığı anlayışıyla doğru ve güvenilir bilgilere ulaşmanızı sağlar. Van Sesi Gazetesi yıllardır Van ve çevresinde güvenilir haberleri sunma konusundaki kararlılığıyla bilinir. Van Olay, Van Gündem, Van Haber, Van haberleri, Gündem haberleri, van erciş, van gevaş, van edremit En doğru ve En tarafsız haber sayfanız
Harman Yolu Bereket Burada sezer süt sağma, sezer süt sağım makinesi, süt sağma yedek parça, sezer marka yedek parça, motorlu testere, motorlu tırpan, ağaç kesme makinası, benzinli ürünler, motor yağı, buji, eğe, stihl zincir
Nur Medikal GiyimHemşire forması, cerrahi bone, doktor kıyafeti, hemşire kıyafeti, desenli formalar, sabo terlik, hastane terlikleri, airmax sabo terlik, ortopedik terlik, tesettür hemşire forması
Bediroğlu Hırdavat | Mahmut Kurt şanlıurfa Bediroğlu urfa stihl, Şanlıurfa stihl bayi, Şanlıurfa husqvarna bayi, güneydoğu felco bayi, Şanlıurfa taral bayisi, motorlu testere yedek parça,Şanlıurfa Stihl Bayi, benzinli testere yedek parça, testere zinciri, ağaç kesme pala, klavuz, elektronik bobin, hava filtresi, stihl Şanlıurfa bayi, stihl Şanlıurfa, Şanlıurfa stihl, stihl servisi, Şanlıurfa stihl servis
En Uygun Kumanda Modelleri | Kumanda Sepeti <a href=" https://www.kumandasepeti.com/ kumanda, kumanda modelleri, tv kumandası fiyat, kumanda fiyatı, tv tamiri,adaptörler,led tv fiyatları,televizyon ekran tamiri,tv led değişimi,tv ekran fiyatları,lg tv ekran fiyatları,grundig kumanda,axen televizyon kumandası,televizyon panel,televizyon led,samsung led tv led,panel arızası tamiri,lg lcd led,tv let fiyatlari,tv paneli Kredi kartına taksit fırası sizlerle.
Van Haberleri tarafsız haber yayıncılığı anlayışıyla doğru ve güvenilir bilgilere ulaşmanızı sağlar. Van Sesi Gazetesi yıllardır Van ve çevresinde güvenilir haberleri sunma konusundaki kararlılığıyla bilinir. Van Olay, Van Gündem, Van Haber, Van haberleri, Gündem haberleri, van erciş, van gevaş, van edremit En doğru ve En tarafsız haber sayfanız
Harman Yolu Bereket Burada sezer süt sağma, sezer süt sağım makinesi, süt sağma yedek parça, sezer marka yedek parça, motorlu testere, motorlu tırpan, ağaç kesme makinası, benzinli ürünler, motor yağı, buji, eğe, stihl zincir
Eser Sertifika | Online Sertifika programı sertifika fiyatı, eser sertifika, sertifika, adalet sertifikası, çocuk sertifika, esnaf sertifika, mobilya sertifika başvuru için iletişime geçiniz
Your article helped me a lot, is there any more related content? Thanks!
promosyon powerbank,promosyon termoslar,promosyon matara,promosyon ajanda,promosyon defterler,promosyon takvim
Eser Sertifika | Online Sertifika programı sertifika fiyatı, eser sertifika, sertifika, adalet sertifikası, çocuk sertifika, esnaf sertifika, mobilya sertifika başvuru için iletişime geçiniz
promosyon powerbank,promosyon termoslar,promosyon matara,promosyon ajanda,promosyon defterler,promosyon takvim
Teknoloji kıbrısTeknoloji kıbrıs, kıbrıs teknoloji Teknoloji kıbrıs ile şimdi kredi kartına taksit fırsatları ile sizlerleyiz.
Thank you for your sharing. I am worried that I lack creative ideas. It is your article that makes me full of hope. Thank you. But, I have a question, can you help me? https://accounts.binance.com/bg/register?ref=IJFGOAID
Bediroğlu Hırdavat | Mahmut Kurt şanlıurfa Bediroğlu urfa stihl, Şanlıurfa stihl bayi, Şanlıurfa husqvarna bayi, güneydoğu felco bayi, Şanlıurfa taral bayisi, motorlu testere yedek parça,Şanlıurfa Stihl Bayi, benzinli testere yedek parça, testere zinciri, ağaç kesme pala, klavuz, elektronik bobin, hava filtresi, stihl Şanlıurfa bayi, stihl Şanlıurfa, Şanlıurfa stihl, stihl servisi, Şanlıurfa stihl servis
Nur Medikal GiyimHemşire forması, cerrahi bone, doktor kıyafeti, hemşire kıyafeti, desenli formalar, sabo terlik, hastane terlikleri, airmax sabo terlik, ortopedik terlik, tesettür hemşire forması
Van Haberleri tarafsız haber yayıncılığı anlayışıyla doğru ve güvenilir bilgilere ulaşmanızı sağlar. Van Sesi Gazetesi yıllardır Van ve çevresinde güvenilir haberleri sunma konusundaki kararlılığıyla bilinir. Van Olay, Van Gündem, Van Haber, Van haberleri, Gündem haberleri, van erciş, van gevaş, van edremit En doğru ve En tarafsız haber sayfanız
En Uygun Kumanda Modelleri | Kumanda Sepeti <a href=" https://www.kumandasepeti.com/ kumanda, kumanda modelleri, tv kumandası fiyat, kumanda fiyatı, tv tamiri,adaptörler,led tv fiyatları,televizyon ekran tamiri,tv led değişimi,tv ekran fiyatları,lg tv ekran fiyatları,grundig kumanda,axen televizyon kumandası,televizyon panel,televizyon led,samsung led tv led,panel arızası tamiri,lg lcd led,tv let fiyatlari,tv paneli Kredi kartına taksit fırası sizlerle.
Thank you for your sharing. I am worried that I lack creative ideas. It is your article that makes me full of hope. Thank you. But, I have a question, can you help me?
b0GUhBrvJvf
I am truly thankful to the owner of this web site who has shared this fantastic piece of writing at at this place.bandırma baykan kombi arıza
promosyon powerbank,promosyon termoslar,promosyon matara,promosyon ajanda,promosyon defterler,promosyon takvim
I don’t think the title of your article matches the content lol. Just kidding, mainly because I had some doubts after reading the article.
This UK IPTV provider stands out with its quality streams and solid customer support.
Thanks for sharing. I read many of your blog posts, cool, your blog is very good.
Nur Medikal GiyimHemşire forması, cerrahi bone, doktor kıyafeti, hemşire kıyafeti, desenli formalar, sabo terlik, hastane terlikleri, airmax sabo terlik, ortopedik terlik, tesettür hemşire forması
Bediroğlu Hırdavat | Mahmut Kurt şanlıurfa Bediroğlu urfa stihl, Şanlıurfa stihl bayi, Şanlıurfa husqvarna bayi, güneydoğu felco bayi, Şanlıurfa taral bayisi, motorlu testere yedek parça,Şanlıurfa Stihl Bayi, benzinli testere yedek parça, testere zinciri, ağaç kesme pala, klavuz, elektronik bobin, hava filtresi, stihl Şanlıurfa bayi, stihl Şanlıurfa, Şanlıurfa stihl, stihl servisi, Şanlıurfa stihl servis
En İyi Güvenlik kamera fiyatları, kamera sistemleri, en iyi güvenlik, eniyiguvenlik, istanbul kamera fiyatları uygun fiyatlar için iletişime geçin
Perpa Kameram kamera fiyatları, kamera sistemleri, perpakameram, perpa kamera, istanbul kamera fiyatları uygun fiyatlar için iletişime geçin
En Uygun Kumanda Modelleri | Kumanda Sepeti <a href=" https://www.kumandasepeti.com/ kumanda, kumanda modelleri, tv kumandası fiyat, kumanda fiyatı, tv tamiri,adaptörler,led tv fiyatları,televizyon ekran tamiri,tv led değişimi,tv ekran fiyatları,lg tv ekran fiyatları,grundig kumanda,axen televizyon kumandası,televizyon panel,televizyon led,samsung led tv led,panel arızası tamiri,lg lcd led,tv let fiyatlari,tv paneli Kredi kartına taksit fırası sizlerle.
En İyi Güvenlik kamera fiyatları, kamera sistemleri, en iyi güvenlik, eniyiguvenlik, istanbul kamera fiyatları uygun fiyatlar için iletişime geçin
Perpa Kameram kamera fiyatları, kamera sistemleri, perpakameram, perpa kamera, istanbul kamera fiyatları uygun fiyatlar için iletişime geçin
gerçekten çok yararlı bi konu teşekkürler
En İyi Güvenlik kamera fiyatları, kamera sistemleri, en iyi güvenlik, eniyiguvenlik, istanbul kamera fiyatları uygun fiyatlar için iletişime geçin
Perpa Kameram kamera fiyatları, kamera sistemleri, perpakameram, perpa kamera, istanbul kamera fiyatları uygun fiyatlar için iletişime geçin
Bediroğlu Hırdavat | Mahmut Kurt şanlıurfa Bediroğlu urfa stihl, Şanlıurfa stihl bayi, Şanlıurfa husqvarna bayi, güneydoğu felco bayi, Şanlıurfa taral bayisi, motorlu testere yedek parça,Şanlıurfa Stihl Bayi, benzinli testere yedek parça, testere zinciri, ağaç kesme pala, klavuz, elektronik bobin, hava filtresi, stihl Şanlıurfa bayi, stihl Şanlıurfa, Şanlıurfa stihl, stihl servisi, Şanlıurfa stihl servis
Nur Medikal GiyimHemşire forması, cerrahi bone, doktor kıyafeti, hemşire kıyafeti, desenli formalar, sabo terlik, hastane terlikleri, airmax sabo terlik, ortopedik terlik, tesettür hemşire forması
En Uygun Kumanda Modelleri | Kumanda Sepeti <a href=" https://www.kumandasepeti.com/ kumanda, kumanda modelleri, tv kumandası fiyat, kumanda fiyatı, tv tamiri,adaptörler,led tv fiyatları,televizyon ekran tamiri,tv led değişimi,tv ekran fiyatları,lg tv ekran fiyatları,grundig kumanda,axen televizyon kumandası,televizyon panel,televizyon led,samsung led tv led,panel arızası tamiri,lg lcd led,tv let fiyatlari,tv paneli Kredi kartına taksit fırası sizlerle.
KCpsikoloji | Uzman desteği ile Sağlığınıza ve Özgürlüğünüze Kavuşun rezonans terapi,moraterapi,alkol bıraktırma,diyetisyen desteği,sigara bıraktırma,iştah kapatma,bölgesel incelme
I don’t think the title of your article matches the content lol. Just kidding, mainly because I had some doubts after reading the article.
I don’t think the title of your article matches the content lol. Just kidding, mainly because I had some doubts after reading the article.
Very well presented. Every quote was awesome and thanks for sharing the content. Keep sharing and keep motivating others. balıkesir nakliye firmaları
Thanks for sharing. I read many of your blog posts, cool, your blog is very good.
naturally like your web site however you need to take a look at the spelling on several of your posts. A number of them are rife with spelling problems and I find it very bothersome to tell the truth on the other hand I will surely come again again. bandırma şehirler arası nakliyat
This is my first time pay a quick visit at here and i am really happy to read everthing at one place balıkesir nakliye fiyatları
Very well presented. Every quote was awesome and thanks for sharing the content. Keep sharing and keep motivating others. bandırma lastik
Your article helped me a lot, is there any more related content? Thanks!
This is my first time pay a quick visit at here and i am really happy to read everthing at one place balıkesir nakliye fiyatları
Your article helped me a lot, is there any more related content? Thanks!
Download Premium Themes and Plugins
I’m often to blogging and i really appreciate your content. The article has actually peaks my interest. I’m going to bookmark your web site and maintain checking for brand spanking new information. banvit tavuk çiftliği kurmak istiyorum
Thank you for your sharing. I am worried that I lack creative ideas. It is your article that makes me full of hope. Thank you. But, I have a question, can you help me?
I don’t think the title of your article matches the content lol. Just kidding, mainly because I had some doubts after reading the article.
Your point of view caught my eye and was very interesting. Thanks. I have a question for you.
I appreciate you sharing this blog post. Thanks Again. Cool. bandırma nakliye firmaları
I don’t think the title of your article matches the content lol. Just kidding, mainly because I had some doubts after reading the article.
Malatya Karaca Ticaret | NURKAN KARACA Malatya stihl bayi,Malatya stihl servis,Hızar motoru,Motorlu testere,Motorlu tırpan, Çim biçme makinası,Malatya karacalar,Malatya stihl, nurkan karaca
Motorlu testere, çim biçme makinası, stihl yetkili bayi, stihl yetkili servis, husqvarna yetkili servis, yetkili bayi, mapaş bayi, alpina, oleomac, felco budama makası
Aydın haberleri tarafsız haber yayıncılık aydın, aydın haber, aydın haberleri En doğru ve En tarafsız haber sayfanız
Harman Yolu Bereket Burada sezer süt sağma, sezer süt sağım makinesi, süt sağma yedek parça, sezer marka yedek parça, motorlu testere, motorlu tırpan, ağaç kesme makinası, benzinli ürünler, motor yağı, buji, eğe, stihl zincir
Video booth ve Fotoğraf kabini kiralama Wideo360 | 360 Video Booth,Selfie Booth video 360, 360 video booth, video booth, selfie booth, booth video 360 video booth
Van Haberleri tarafsız haber yayıncılığı anlayışıyla doğru ve güvenilir bilgilere ulaşmanızı sağlar. Van Sesi Gazetesi yıllardır Van ve çevresinde güvenilir haberleri sunma konusundaki kararlılığıyla bilinir. Van Olay, Van Gündem, Van Haber, Van haberleri, Gündem haberleri, van erciş, van gevaş, van edremit En doğru ve En tarafsız haber sayfanız
For the reason that the admin of this site is working, no uncertainty very quickly it will be renowned, due to its quality contents. ısıtıcı
Malatya Karaca Ticaret | NURKAN KARACA Malatya stihl bayi,Malatya stihl servis,Hızar motoru,Motorlu testere,Motorlu tırpan, Çim biçme makinası,Malatya karacalar,Malatya stihl, nurkan karaca
Motorlu testere, çim biçme makinası, stihl yetkili bayi, stihl yetkili servis, husqvarna yetkili servis, yetkili bayi, mapaş bayi, alpina, oleomac, felco budama makası
Harman Yolu Bereket Burada sezer süt sağma, sezer süt sağım makinesi, süt sağma yedek parça, sezer marka yedek parça, motorlu testere, motorlu tırpan, ağaç kesme makinası, benzinli ürünler, motor yağı, buji, eğe, stihl zincir
Aydın haberleri tarafsız haber yayıncılık aydın, aydın haber, aydın haberleri En doğru ve En tarafsız haber sayfanız
Video booth ve Fotoğraf kabini kiralama Wideo360 | 360 Video Booth,Selfie Booth video 360, 360 video booth, video booth, selfie booth, booth video 360 video booth
Van Haberleri tarafsız haber yayıncılığı anlayışıyla doğru ve güvenilir bilgilere ulaşmanızı sağlar. Van Sesi Gazetesi yıllardır Van ve çevresinde güvenilir haberleri sunma konusundaki kararlılığıyla bilinir. Van Olay, Van Gündem, Van Haber, Van haberleri, Gündem haberleri, van erciş, van gevaş, van edremit En doğru ve En tarafsız haber sayfanız
I don’t think the title of your article matches the content lol. Just kidding, mainly because I had some doubts after reading the article.
Your point of view caught my eye and was very interesting. Thanks. I have a question for you.
Thanks for sharing. I read many of your blog posts, cool, your blog is very good.
I very delighted to find this internet site on bing, just what I was searching for as well saved to fav bandırma ariston kombi
naturally like your web site however you need to take a look at the spelling on several of your posts. A number of them are rife with spelling problems and I find it very bothersome to tell the truth on the other hand I will surely come again again. güvenlik kamera sistemleri
I do not even understand how I ended up here, but I assumed this publish used to be great fabrika ısıtma sistemleri
MapperX’s thermal inspection at our 800 MW solar installation in Western Australia detected malfunctioning wiring, which was causing a 5% drop in energy output. After repairs, energy production increased by 7%.
Your point of view caught my eye and was very interesting. Thanks. I have a question for you.
I’m often to blogging and i really appreciate your content. The article has actually peaks my interest. I’m going to bookmark your web site and maintain checking for brand spanking new information. güvenlik kamera
naturally like your web site however you need to take a look at the spelling on several of your posts. A number of them are rife with spelling problems and I find it very bothersome to tell the truth on the other hand I will surely come again again. gece görüşlü kamera seti fiyatları
I don’t think the title of your article matches the content lol. Just kidding, mainly because I had some doubts after reading the article.
naturally like your web site however you need to take a look at the spelling on several of your posts. A number of them are rife with spelling problems and I find it very bothersome to tell the truth on the other hand I will surely come again again. bandırma baymak kombi bakımı
For the reason that the admin of this site is working, no uncertainty very quickly it will be renowned, due to its quality contents about Turkey teeth.
I appreciate you sharing this blog post. Thanks Again. Cool. bandırma oto çekici
I’m so impressed by the depth and clarity of your writing. This post manages to be both engaging and informative, which is not an easy feat. You’ve done a phenomenal job of breaking down this topic, and I’m truly grateful for the insights you’ve shared.
Hi there to all, for the reason that I am genuinely keen of reading this website’s post to be updated on a regular basis. It carries pleasant stuff. google web sitesi kurma
I don’t think the title of your article matches the content lol. Just kidding, mainly because I had some doubts after reading the article.
I really like reading through a post that can make men and women think. Also, thank you for allowing me to comment! dursunbeyliler nakliyat
I don’t think the title of your article matches the content lol. Just kidding, mainly because I had some doubts after reading the article.
I don’t think the title of your article matches the content lol. Just kidding, mainly because I had some doubts after reading the article.
Your point of view caught my eye and was very interesting. Thanks. I have a question for you.
Your article helped me a lot, is there any more related content? Thanks!
I don’t think the title of your article matches the content lol. Just kidding, mainly because I had some doubts after reading the article.
Thank you for your sharing. I am worried that I lack creative ideas. It is your article that makes me full of hope. Thank you. But, I have a question, can you help me?
Your article helped me a lot, is there any more related content? Thanks!
Thanks for sharing. I read many of your blog posts, cool, your blog is very good.
Diyarbakır Haberleri tarafsız haber yayıncılığı anlayışıyla doğru ve güvenilir bilgilere ulaşmanızı sağlar Diyarbakır Olay, Diyarbakır Gündem, Diyarbakır Haber, Diyarbakır haberleri, Gündem haberleri, Diyarbakır bismil haber, Diyarbakır çınar gündem, diyarbakır ergani En doğru ve En tarafsız haber sayfanız
seo hizmeti, seo fiyat, web tasarım, web yazılım, seo yönetimi, seo fiyatı, backlink analizi, backlink fiyat, Google ads yönetimi
diyarbakır haber, çınar haberleri, çınar gündem, çınar olay, çınar ilçe haberleri, Diyarbakır haberleri
I don’t think the title of your article matches the content lol. Just kidding, mainly because I had some doubts after reading the article.
Thanks for sharing. I read many of your blog posts, cool, your blog is very good.
Diyarbakır Haberleri tarafsız haber yayıncılığı anlayışıyla doğru ve güvenilir bilgilere ulaşmanızı sağlar Diyarbakır Olay, Diyarbakır Gündem, Diyarbakır Haber, Diyarbakır haberleri, Gündem haberleri, Diyarbakır bismil haber, Diyarbakır çınar gündem, diyarbakır ergani En doğru ve En tarafsız haber sayfanız
diyarbakır haber, çınar haberleri, çınar gündem, çınar olay, çınar ilçe haberleri, Diyarbakır haberleri
seo hizmeti, seo fiyat, web tasarım, web yazılım, seo yönetimi, seo fiyatı, backlink analizi, backlink fiyat, Google ads yönetimi
Nur Medikal GiyimHemşire forması, cerrahi bone, doktor kıyafeti, hemşire kıyafeti, desenli formalar, sabo terlik, hastane terlikleri, airmax sabo terlik, ortopedik terlik, tesettür hemşire forması
seo hizmeti, seo fiyat, web tasarım, web yazılım, seo yönetimi, seo fiyatı, backlink analizi, backlink fiyat, Google ads yönetimi
Bediroğlu Hırdavat | Mahmut Kurt şanlıurfa Bediroğlu urfa stihl, Şanlıurfa stihl bayi, Şanlıurfa husqvarna bayi, güneydoğu felco bayi, Şanlıurfa taral bayisi, motorlu testere yedek parça,Şanlıurfa Stihl Bayi, benzinli testere yedek parça, testere zinciri, ağaç kesme pala, klavuz, elektronik bobin, hava filtresi, stihl Şanlıurfa bayi, stihl Şanlıurfa, Şanlıurfa stihl, stihl servisi, Şanlıurfa stihl servis
Can you be more specific about the content of your article? After reading it, I still have some doubts. Hope you can help me.
Takipteyim kaliteli ve güzel bir içerik olmuş dostum.
Probag | Sırt Çantası ve Alet çantası alet çantası, takım çantası, çanta üretimi
Probag | Sırt Çantası ve Alet çantası alet çantası, takım çantası, çanta üretimi
Özlem Bahçe | Koham Budama Makası koham budama makası, koham 35 mm, koham şarjlı makas, akülü şarjlı, akülü makas
Özlem Bahçe | Koham Budama Makası koham budama makası, koham 35 mm, koham şarjlı makas, akülü şarjlı, akülü makas
Your article helped me a lot, is there any more related content? Thanks!
https://quicktelecast.com/stalagmites-reveal-australias-pre-colonial-bushfire-history/
I don’t think the title of your article matches the content lol. Just kidding, mainly because I had some doubts after reading the article.
Your point of view caught my eye and was very interesting. Thanks. I have a question for you.
GES denetim ve muayene ile güneş enerji santrallerimiz hiç olmadığı kadar verimli ve güvenli. Harika bir hizmet!
GES Elektriksel Ölçüm ve Testler, sistemimizi daha güvenli hale getirdi. Detaylı analiz ve raporlamaları gerçekten çok başarılı!
seo hizmeti, seo fiyat, web tasarım, web yazılım, seo yönetimi, seo fiyatı, backlink analizi, backlink fiyat, Google ads yönetimi
Nur Medikal GiyimHemşire forması, cerrahi bone, doktor kıyafeti, hemşire kıyafeti, desenli formalar, sabo terlik, hastane terlikleri, airmax sabo terlik, ortopedik terlik, tesettür hemşire forması
Didim Taksi | Çamlık Taksi | Altınkum Taksi didim taksi, havaalanı taksi, korsan taksi, altınkum taksi, çamlık taksi
Bediroğlu Hırdavat | Mahmut Kurt şanlıurfa Bediroğlu urfa stihl, Şanlıurfa stihl bayi, Şanlıurfa husqvarna bayi, güneydoğu felco bayi, Şanlıurfa taral bayisi, motorlu testere yedek parça,Şanlıurfa Stihl Bayi, benzinli testere yedek parça, testere zinciri, ağaç kesme pala, klavuz, elektronik bobin, hava filtresi, stihl Şanlıurfa bayi, stihl Şanlıurfa, Şanlıurfa stihl, stihl servisi, Şanlıurfa stihl servis
Didim Taksi | Çamlık Taksi | Altınkum Taksi didim taksi, havaalanı taksi, korsan taksi, altınkum taksi, çamlık taksi
En iyi saç bakım şampuanlarını keşfetmek için Sisteme 11’i ziyaret edin.
I don’t think the title of your article matches the content lol. Just kidding, mainly because I had some doubts after reading the article.
Didim Taksi | İhsan Taksi didim taksi, konforlu taksi, aydın taksi, çamlık taksi
Kıbrıs Kariyer | Kıbrıs iş ara kıbrıs kariyer, iş bulmak kıbrıs, kıbrıs işveren, kıbrıs asgari ücret
Dxd Global | Development dxd global, global dxd, deluxe bilisim, deluxe global, IT solutions, web developer, worpress global, wordpress setup
Çağra LTD | Mutfak ürünleri | Bahçe aksesuar Kıbrıs mutfak gereçleri, hırdavat kıbrıs, kıbrıs hırdavat, matkap kıbrıs, kıbrıs inşaat ürünleri, kıbrıs mobilya
Kavazelectronics | Kıbrıs Elektronik eşyalar Kıbrıs elektronik eşyalar, beyaz eşya kıbrıs, kıbrıs tv fiyatları, davlumbaz kıbrıs, beyaz eşya fiyatları
Deluxe Promosyon | 2025 Promosyon ürünleri eşantiyon hediyelik, ajanda 2025, promosyon ucuz, hızlı promosyon ürünü, kalem yapımı promosyon
I don’t think the title of your article matches the content lol. Just kidding, mainly because I had some doubts after reading the article.
q8SZ69Ahg3I
Thank you for your sharing. I am worried that I lack creative ideas. It is your article that makes me full of hope. Thank you. But, I have a question, can you help me?
Kıbrıs Kariyer | Kıbrıs iş ara kıbrıs kariyer, iş bulmak kıbrıs, kıbrıs işveren, kıbrıs asgari ücret
Dijital Ajans | Deluxe Bilişim seo hizmeti,sosyal medya ajansı,kurumsal seo hizmeti,yazılım desteği, wordpress site kurulumu, eticaret site kurulumu,,sosyal medya ajans
Çağra LTD | Mutfak ürünleri | Bahçe aksesuar Kıbrıs mutfak gereçleri, hırdavat kıbrıs, kıbrıs hırdavat, matkap kıbrıs, kıbrıs inşaat ürünleri, kıbrıs mobilya
Dxd Global | Development dxd global, global dxd, deluxe bilisim, deluxe global, IT solutions, web developer, worpress global, wordpress setup
Deluxe Promosyon | 2025 Promosyon ürünleri eşantiyon hediyelik, ajanda 2025, promosyon ucuz, hızlı promosyon ürünü, kalem yapımı promosyon
Kavazelectronics | Kıbrıs Elektronik eşyalar Kıbrıs elektronik eşyalar, beyaz eşya kıbrıs, kıbrıs tv fiyatları, davlumbaz kıbrıs, beyaz eşya fiyatları
Your article helped me a lot, is there any more related content? Thanks! https://accounts.binance.com/en-IN/register?ref=UM6SMJM3
Your article helped me a lot, is there any more related content? Thanks! https://accounts.binance.com/id/register?ref=GJY4VW8W
Can you be more specific about the content of your article? After reading it, I still have some doubts. Hope you can help me.
Hocam Ellerinize Sağlık, boşanma avukatı hakkında Detaylı ve Güzel Makale Olmuş.
Kıbrıs Kariyer | Kıbrıs iş ara kıbrıs kariyer, iş bulmak kıbrıs, kıbrıs işveren, kıbrıs asgari ücret
Deluxe Promosyon | 2025 Promosyon ürünleri eşantiyon hediyelik, ajanda 2025, promosyon ucuz, hızlı promosyon ürünü, kalem yapımı promosyon
Thanks for sharing. I read many of your blog posts, cool, your blog is very good.
Hocam Ellerinize Sağlık, köpek oteli hakkında Detaylı ve Güzel Makale Olmuş.
Can you be more specific about the content of your article? After reading it, I still have some doubts. Hope you can help me.
Kıbrıs Kariyer | Kıbrıs iş ara kıbrıs kariyer, iş bulmak kıbrıs, kıbrıs işveren, kıbrıs asgari ücret
Deluxe Promosyon | 2025 Promosyon ürünleri eşantiyon hediyelik, ajanda 2025, promosyon ucuz, hızlı promosyon ürünü, kalem yapımı promosyon
Hocam Ellerinize Sağlık, köpek oteli hakkında Detaylı ve Güzel Makale Olmuş.
Hocam Ellerinize Sağlık, köpek oteli ve pet otel hakkında Detaylı ve Güzel Makale Olmuş.
Your article helped me a lot, is there any more related content? Thanks!
Hocam Ellerinize Sağlık bubble tea Hakkında Detaylı ve Güzel Makale Olmuş.
Thank you for your sharing. I am worried that I lack creative ideas. It is your article that makes me full of hope. Thank you. But, I have a question, can you help me?
For the reason that the admin of this site is working, no uncertainty very quickly it will be renowned, due to its quality contents about Caramel Macchiato.
I don’t think the title of your article matches the content lol. Just kidding, mainly because I had some doubts after reading the article.
Your point of view caught my eye and was very interesting. Thanks. I have a question for you.
Your point of view caught my eye and was very interesting. Thanks. I have a question for you.
Thanks for sharing. I read many of your blog posts, cool, your blog is very good.
Thank you for your sharing. I am worried that I lack creative ideas. It is your article that makes me full of hope. Thank you. But, I have a question, can you help me?
Thanks for sharing. I read many of your blog posts, cool, your blog is very good.
What a brilliant post. See more: https://thanhdatmedical.vn ! Your ability to deliver valuable insights with clarity and precision is unmatched. I’m always so impressed by the quality of your work, and this piece is no exception. Thank you for creating such meaningful content.
Your article helped me a lot, is there any more related content? Thanks!
I don’t think the title of your article matches the content lol. Just kidding, mainly because I had some doubts after reading the article.
Thank you for your sharing. I am worried that I lack creative ideas. It is your article that makes me full of hope. Thank you. But, I have a question, can you help me?
This post is another example of why I always look forward to reading your content. It’s thoughtful, engaging, and so well-organized. You make even the most difficult topics feel approachable and clear—thank you for sharing your expertise.
Thanks for sharing. I read many of your blog posts, cool, your blog is very good.
Thanks for sharing. I read many of your blog posts, cool, your blog is very good.
Thanks for sharing. I read many of your blog posts, cool, your blog is very good.
I don’t think the title of your article matches the content lol. Just kidding, mainly because I had some doubts after reading the article.
Your article helped me a lot, is there any more related content? Thanks!
Your article helped me a lot, is there any more related content? Thanks!
I don’t think the title of your article matches the content lol. Just kidding, mainly because I had some doubts after reading the article.
For the reason that the admin of this site is working, no uncertainty very quickly it will be renowned, due to its quality contents about Yunnan Coffee.
Thank you for your sharing. I am worried that I lack creative ideas. It is your article that makes me full of hope. Thank you. But, I have a question, can you help me?
Your article helped me a lot, is there any more related content? Thanks!
Thanks for sharing. I read many of your blog posts, cool, your blog is very good.
I don’t think the title of your article matches the content lol. Just kidding, mainly because I had some doubts after reading the article. https://www.binance.info/en/register?ref=JHQQKNKN
Can you be more specific about the content of your article? After reading it, I still have some doubts. Hope you can help me.
Can you be more specific about the content of your article? After reading it, I still have some doubts. Hope you can help me.
Thank you for your sharing. I am worried that I lack creative ideas. It is your article that makes me full of hope. Thank you. But, I have a question, can you help me?
I don’t think the title of your article matches the content lol. Just kidding, mainly because I had some doubts after reading the article. https://www.binance.com/ur/register?ref=WTOZ531Y
Your point of view caught my eye and was very interesting. Thanks. I have a question for you.
Your article helped me a lot, is there any more related content? Thanks!
Your article helped me a lot, is there any more related content? Thanks!
Your article helped me a lot, is there any more related content? Thanks!
Your article helped me a lot, is there any more related content? Thanks!
I don’t think the title of your article matches the content lol. Just kidding, mainly because I had some doubts after reading the article.
I don’t think the title of your article matches the content lol. Just kidding, mainly because I had some doubts after reading the article.
Your article helped me a lot, is there any more related content? Thanks!
Can you be more specific about the content of your article? After reading it, I still have some doubts. Hope you can help me.
Thank you for your sharing. I am worried that I lack creative ideas. It is your article that makes me full of hope. Thank you. But, I have a question, can you help me?
Can you be more specific about the content of your article? After reading it, I still have some doubts. Hope you can help me.
For the reason that the admin of this site is working, no uncertainty very quickly it will be renowned, due to its quality contents about menopause.
Your article helped me a lot, is there any more related content? Thanks! https://www.binance.com/hu/register?ref=FIHEGIZ8
Thank you for your sharing. I am worried that I lack creative ideas. It is your article that makes me full of hope. Thank you. But, I have a question, can you help me?
Thank you for your sharing. I am worried that I lack creative ideas. It is your article that makes me full of hope. Thank you. But, I have a question, can you help me?
I don’t think the title of your article matches the content lol. Just kidding, mainly because I had some doubts after reading the article. https://www.binance.info/en-NG/register-person?ref=JHQQKNKN
Thank you for your sharing. I am worried that I lack creative ideas. It is your article that makes me full of hope. Thank you. But, I have a question, can you help me?
Your point of view caught my eye and was very interesting. Thanks. I have a question for you. https://www.binance.info/bn/register-person?ref=UM6SMJM3
Can you be more specific about the content of your article? After reading it, I still have some doubts. Hope you can help me.
Your article helped me a lot, is there any more related content? Thanks!
I don’t think the title of your article matches the content lol. Just kidding, mainly because I had some doubts after reading the article. https://www.binance.info/bg/register?ref=V2H9AFPY
Thanks for sharing. I read many of your blog posts, cool, your blog is very good. https://www.binance.info/ES_la/register-person?ref=T7KCZASX
Can you be more specific about the content of your article? After reading it, I still have some doubts. Hope you can help me.
Your point of view caught my eye and was very interesting. Thanks. I have a question for you.
Can you be more specific about the content of your article? After reading it, I still have some doubts. Hope you can help me.
Your point of view caught my eye and was very interesting. Thanks. I have a question for you. https://www.binance.info/pl/register-person?ref=YY80CKRN
I don’t think the title of your article matches the content lol. Just kidding, mainly because I had some doubts after reading the article. https://www.binance.com/ar/register?ref=V2H9AFPY
Thanks for sharing. I read many of your blog posts, cool, your blog is very good.
Thank you for your sharing. I am worried that I lack creative ideas. It is your article that makes me full of hope. Thank you. But, I have a question, can you help me?
Thanks for sharing. I read many of your blog posts, cool, your blog is very good.
Your article helped me a lot, is there any more related content? Thanks!
Thanks for sharing. I read many of your blog posts, cool, your blog is very good.
Can you be more specific about the content of your article? After reading it, I still have some doubts. Hope you can help me.
zIPdZQtkdTv
Your article helped me a lot, is there any more related content? Thanks!
Your point of view caught my eye and was very interesting. Thanks. I have a question for you.
Thanks for sharing. I read many of your blog posts, cool, your blog is very good.
Can you be more specific about the content of your article? After reading it, I still have some doubts. Hope you can help me.
Thank you for your sharing. I am worried that I lack creative ideas. It is your article that makes me full of hope. Thank you. But, I have a question, can you help me?
Can you be more specific about the content of your article? After reading it, I still have some doubts. Hope you can help me.
Your point of view caught my eye and was very interesting. Thanks. I have a question for you.
Thank you for your sharing. I am worried that I lack creative ideas. It is your article that makes me full of hope. Thank you. But, I have a question, can you help me?
Your article helped me a lot, is there any more related content? Thanks!
Your point of view caught my eye and was very interesting. Thanks. I have a question for you.
I don’t think the title of your article matches the content lol. Just kidding, mainly because I had some doubts after reading the article.
I don’t think the title of your article matches the content lol. Just kidding, mainly because I had some doubts after reading the article.
Thank you for your sharing. I am worried that I lack creative ideas. It is your article that makes me full of hope. Thank you. But, I have a question, can you help me?
Thanks for sharing. I read many of your blog posts, cool, your blog is very good.
Can you be more specific about the content of your article? After reading it, I still have some doubts. Hope you can help me.
Your article helped me a lot, is there any more related content? Thanks!
Your point of view caught my eye and was very interesting. Thanks. I have a question for you. https://www.binance.com/hu/register?ref=IQY5TET4
Thank you for your shening. I am worried that I lack creative ideas. It is your enticle that makes me full of hope. Thank you. But, I have a question, can you help me? https://accounts.binance.com/ro/register?ref=HX1JLA6Z
Can you be more specific about the content of your article? After reading it, I still have some doubts. Hope you can help me. https://accounts.binance.com/ka-GE/register-person?ref=ILE8IH9H
Thanks for sharing. I read many of your blog posts, cool, your blog is very good. https://www.binance.info/fr/register?ref=T7KCZASX
Thank you for your sharing. I am worried that I lack creative ideas. It is your article that makes me full of hope. Thank you. But, I have a question, can you help me?
Your article helped me a lot, is there any more related content? Thanks! https://accounts.binance.com/ph/register?ref=IU36GZC4
Your point of view caught my eye and was very interesting. Thanks. I have a question for you.
Can you be more specific about the content of your article? After reading it, I still have some doubts. Hope you can help me.
Can you be more specific about the content of your article? After reading it, I still have some doubts. Hope you can help me. https://www.binance.com/fr-AF/register?ref=JHQQKNKN
Your article helped me a lot, is there any more related content? Thanks! https://accounts.binance.info/ar-BH/register?ref=S5H7X3LP
Can you be more specific about the content of your article? After reading it, I still have some doubts. Hope you can help me. https://www.binance.info/sl/register?ref=I3OM7SCZ
I don’t think the title of your article matches the content lol. Just kidding, mainly because I had some doubts after reading the article.
Your point of view caught my eye and was very interesting. Thanks. I have a question for you. https://www.binance.com/ur/register?ref=SZSSS70P
Your point of view caught my eye and was very interesting. Thanks. I have a question for you. https://accounts.binance.info/register-person?ref=IXBIAFVY
Thank you for your sharing. I am worried that I lack creative ideas. It is your article that makes me full of hope. Thank you. But, I have a question, can you help me?
Thanks for sharing. I read many of your blog posts, cool, your blog is very good.
I don’t think the title of your article matches the content lol. Just kidding, mainly because I had some doubts after reading the article.
Can you be more specific about the content of your article? After reading it, I still have some doubts. Hope you can help me. https://www.binance.com/register?ref=IXBIAFVY
Can you be more specific about the content of your article? After reading it, I still have some doubts. Hope you can help me.
Thanks for sharing. I read many of your blog posts, cool, your blog is very good. https://www.binance.info/register?ref=QCGZMHR6
Your article helped me a lot, is there any more related content? Thanks! https://accounts.binance.com/bg/register-person?ref=V2H9AFPY
Your point of view caught my eye and was very interesting. Thanks. I have a question for you.
Your article helped me a lot, is there any more related content? Thanks! https://www.binance.info/en-ZA/register?ref=B4EPR6J0
Can you be more specific about the content of your article? After reading it, I still have some doubts. Hope you can help me. https://accounts.binance.info/zh-TC/register?ref=DCKLL1YD
Can you be more specific about the content of your article? After reading it, I still have some doubts. Hope you can help me.
Can you be more specific about the content of your article? After reading it, I still have some doubts. Hope you can help me.
I don’t think the title of your article matches the content lol. Just kidding, mainly because I had some doubts after reading the article.
Your article helped me a lot, is there any more related content? Thanks!
Thank you for your sharing. I am worried that I lack creative ideas. It is your article that makes me full of hope. Thank you. But, I have a question, can you help me? https://www.binance.info/register?ref=JW3W4Y3A
Your point of view caught my eye and was very interesting. Thanks. I have a question for you. https://accounts.binance.com/register/person?ref=QCGZMHR6
Купить аккаунты криптобирж и быстро начать торговлю на ведущих криптовалютных биржах, но сталкиваетесь с ограничениями или длительной процедурой верификации? купить аккаунты криптобирж
I don’t think the title of your article matches the content lol. Just kidding, mainly because I had some doubts after reading the article.